Avanan identified a new phishing attack that bypasses EOP (Exchange Online Protection) URL filters, which scan Office documents like Word (.docx), Excel (.xlsx), and PowerPoint (.pptx). (See the other popular link parsers that failed to detect this attack.)
The attack emails include a .docx attachment containing a malicious link that leads to a credential harvesting login page. Link parsers that do not scan the full document, but rely instead on a relationship (xml.rels) file for the list of links included in the attachment, fail to identify the malicious URL.
Like the index of a book, the relationship file lists the essential of the parts of the document — external links and images, or internal document components, like font tables. Sometimes, key terms might not be included in the index, but they are still in the book. In this attack, hackers deleted the external links from the relationship file to bypass link parsers that only read the index rather than the “book.”
Background
Office Open XML files are the default format for all Office applications. Office documents (.docx, .xlsx, .pptx) are made up of a number of XML files that include all the font, image, formatting, and object information which make up the document.
To see this for yourself, convert any .docx file to a ZIP, unzip the file, and view it in your computer’s document finder (see below).
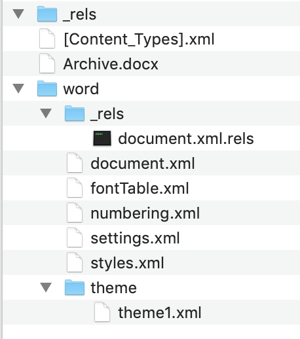
This is what an unzipped .docx file looks like in macOS.
Shown above, the relationship directory (word/_rels/document.xml.rels) is an XML file that maps relationships within the .docx file (to font tables, document settings, comments, footnotes, style definitions, numbering definitions) and with resources outside of the package, such as links and images. When the document includes web links, they are added to the document.xml.rels relationships file.
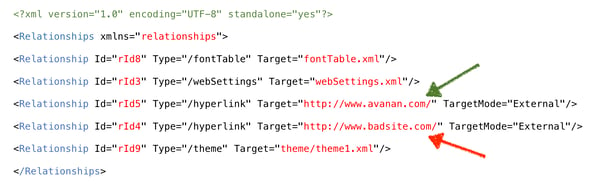
This example relationship file contains internal resources, such as font, theme, and web settings, and external resources, including a safe and malicious link.
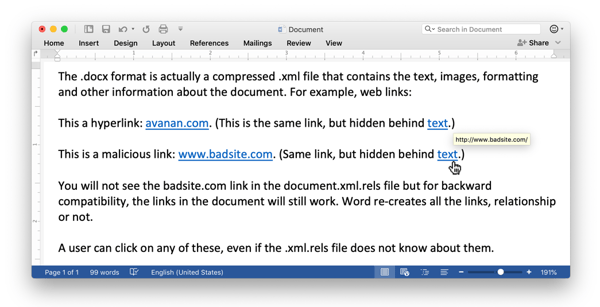
The links from the relationship file above are rendered as hyperlinks in a Word document.
If, for some reason, one of these links is broken, the link will still work when the user clicks on it in the original document. For backward compatibility, Word will resolve the link.
How the NoRelationship attack works
When scanning attachments for malicious content, most email filters will scan the document for external web links and compare them to a database of malicious sites, or even follow the links and evaluate their target.
Many parsers, however, take a shortcut and only look at the document.xmls.rels file, which typically contains a list of al the URLs that are within the full document.
If, for some reason, the document contains URL links that are not included in the xmls.rels file, these parses will not see them, even though they are still active and clickable within the document. The hackers are deleting the URLs from the relationship files so that the parsers do not see them.
Which link parsers do the NoRelationship Attack bypass?
Avanan tested this vulnerability on the most popular security tools to determine which populations could be affected by this attack.
| Security Engine | Vulnerable to the NoRelationship Attack? |
| Microsoft EOP (default Office 365 security) | Yes |
| Microsoft Advanced Threat Protection (ATP) | No |
| ProofPoint | Yes |
| F-Secure | Yes |
| Mimecast | No |
Conclusion
Fittingly, Avanan detected the NoRelationship Attack right before Valentine’s day.
None of these hyperlinks should have gone undetected, because the URLs are known to be malicious. By removing the malicious links from the document.xml.rels relationship file, hackers confused link parsers that only scan the relationship file for external links. It seems there are no shortcuts to be had in email scanning. The only solution is to scan the entire file.
To read the origina article:
https://www.avanan.com/resources/the-norelationship-attack-bypasses-office-365



