Exploitation attempts of a highly critical vulnerability discovered in the Drupal content management software (CMS) on February 20 were blocked by Cloudfare using Web Application Firewall (WAF) rules designed to protect its customers’ websites from being compromised.
According to Drupal project team’s security advisory, the websites impacted by the vulnerability tracked as CVE-2019-6340 are those that have the Drupal 8 core RESTful Web Services (rest) module turned on, and also allow PATCH or POST requests.
To avoid having to ask each of their customers to update their installations after a patched version was released by Drupal on the same day, Cloudfare “identified the type of vulnerability” within 15 minutes, and they “were able to deploy rules to block the exploit well before any real attacks were seen.”
First attack observed 48 hours after vulnerability disclosure
After analyzing Drupal’s patch in depth, the company’s security team discovered that a potential exploit would be based on deserialization which can be abused with the help of a maliciously crafted serialized Object.
The worst part was that potential attackers could exploit CVE-2019-6340 without any authentication requirements, allowing for all the data on the system to be modified or deleted.
Following multiple tweaks, Cloudfare eventually deployed a WAF rule they named D0020 which was very effective in automatically blocking attackers trying to exploit the highly critical vulnerability present in unpatched Drupal installations.
Cloudfare says that “The rule was already deployed in ‘drop’ mode by the time our first attack was observed at around 7pm UTC on Friday the 22nd of February 2019, and to date it has matched zero false positives. This is less than 48 hours from the announcement from Drupal.”
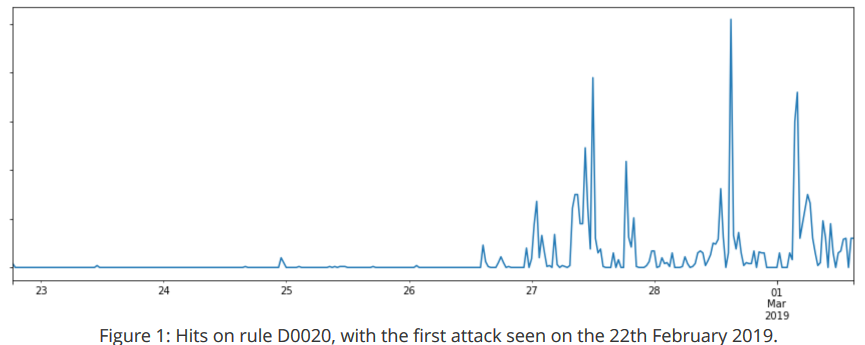
While at first, the threat actors were only probing for vulnerable Drupal installations by remotely invoking commands like phpinfo and executing test payloads, the attacks soon picked up trying to drop backdoor payloads designed to help crooks to maintain their access even if the server would’ve been patched later on.
“The pattern we saw here is fairly typical of a newly announced vulnerability. [..] This vulnerability was weaponized within two days of disclosure, but that is by no means the shortest time frame we’ve seen,” concludes Cloudfare.
To read the original article:



