A new Ransomware-as-a-Service called Jokeroo is being promoted on underground hacking sites and via Twitter that allows affiliates to allegedly gain access to a fully functional ransomware and payment server.
A Ransomware-as-a-Service is when a developer creates a ransomware and a payment site and allows affiliates to sign up and distribute the ransomware. As part of this deal, the affiliates and the developer will split the payments that are received from victims.
According to a malware researcher named Damian, the Jokeroo RaaS first started promoting itself as a GandCrab Ransomware RaaS on the underground hacking forum Exploit.in.
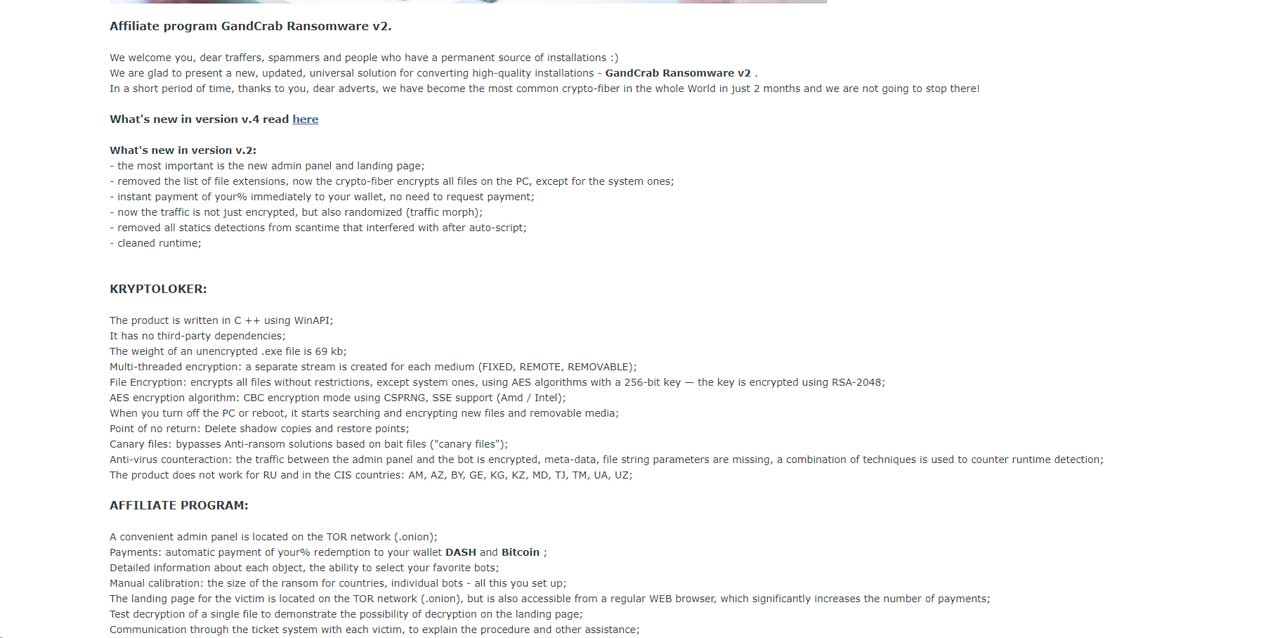
Soon after, security researcher David Montenegro found that the group changed their RaaS named to Jokeroo RaaS.
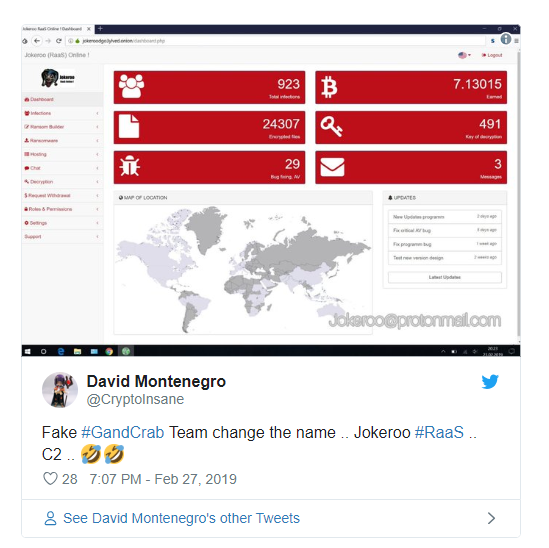
Since then, the developers have been promoting their service on Twitter and stating that they have nothing to do with GandCrab.

Unlike most ransomware-as-a-service offerings, in order to become an affiliate a would-be criminal has to pay to join a particular membership package. These packages range from $90 USD, where the affiliate earns 85% of the ransom payments, to $300 and $600 packages where the affiliates keep all of the revenue and gets extra perks such as Salsa20 encryption, different ransomware variants, and different payment cryptocurrency options.
Below is the base set of offerings a $90 affiliate gets when they join:
You can change and customize your ransomware
Name of the project
Change the demand of ransom
Change all the logo, An icon in format .ICO, Remove the jokeroo logo
You can choose the extension
A description to help the victim in format .TXT
Ransomware update manually
You can create 1 ransomware
The victim can pay you in Bitcoin
Withdrawal in Bitcoin
You can infected in unlimited
You will have news about the dashboard
Undetectable by AV update regularly
Spread manually
Show the IP of the victim
We will touch 15% fees ransom
You will be able to manage all the victims since the dashboard
Display: CD key, PC Name, Encrypted files, Operating System (OS)
Lifetime license !Included on the page are images of the dashboard that an affiliate would gain access. For example, below you can see the main dashboard page for the Jokeroo RaaS. Even though the below images states that the RaaS has earned 7.13 bitcoins and has 923 infections, BleepingComputer thinks this is test data as the ransomware has not been seen in the wild or submitted to ID Ransomware.
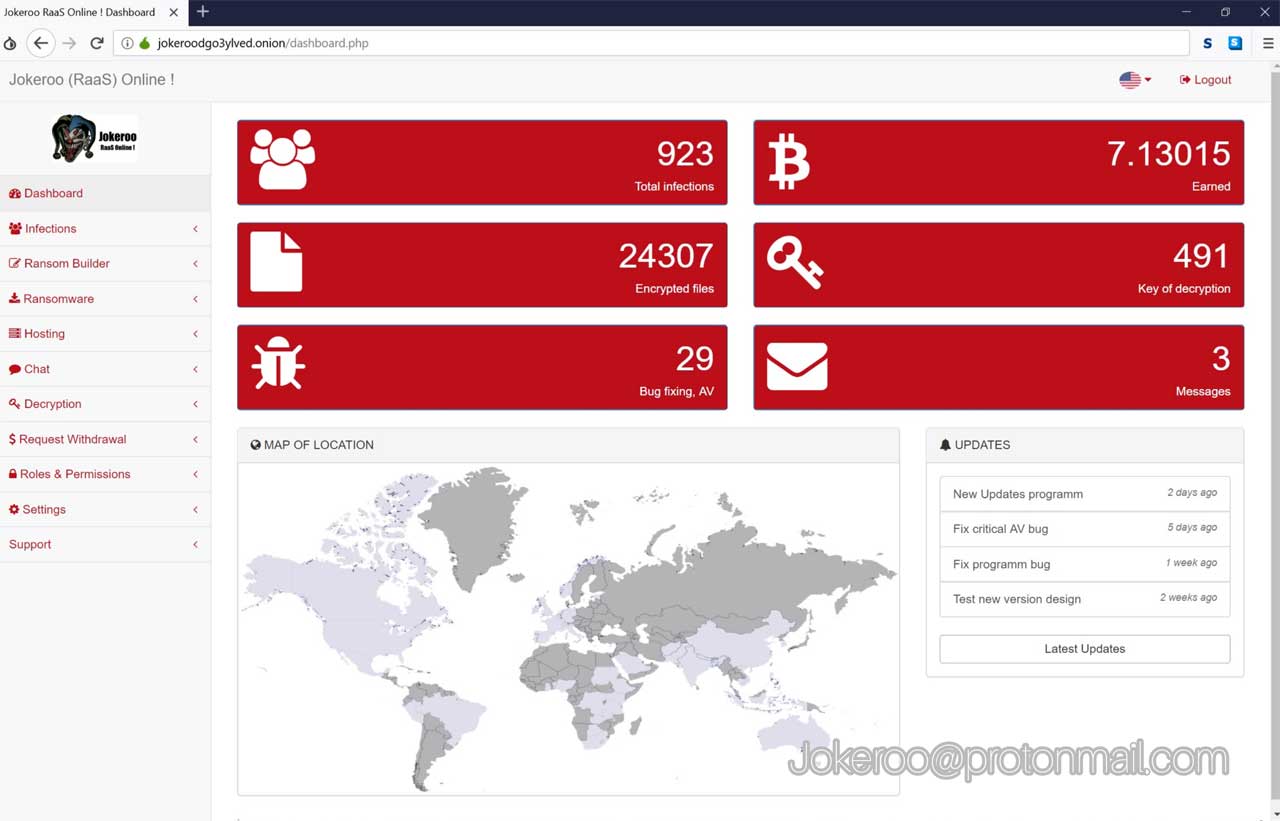
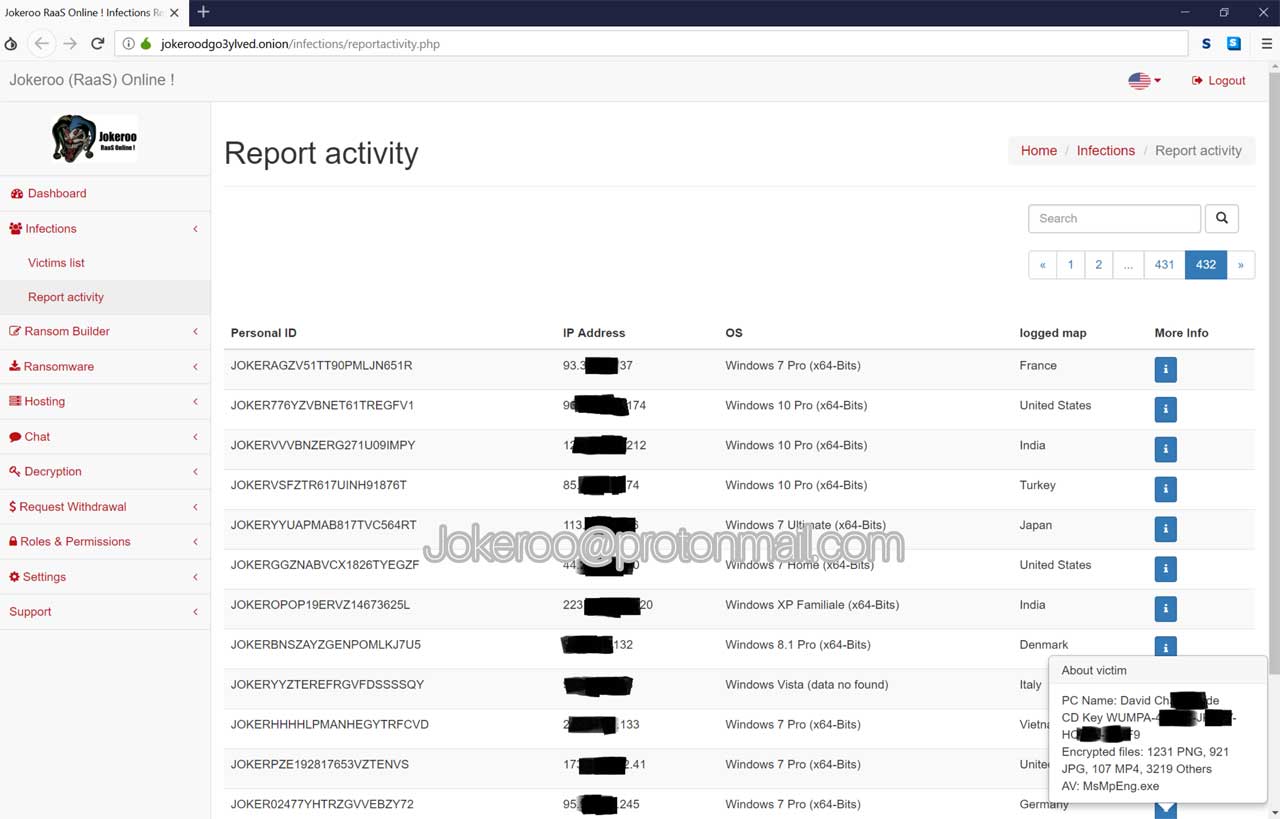
This dashboard will also allow affiliates to see a list of their victims, when they were infected, and if they have paid.
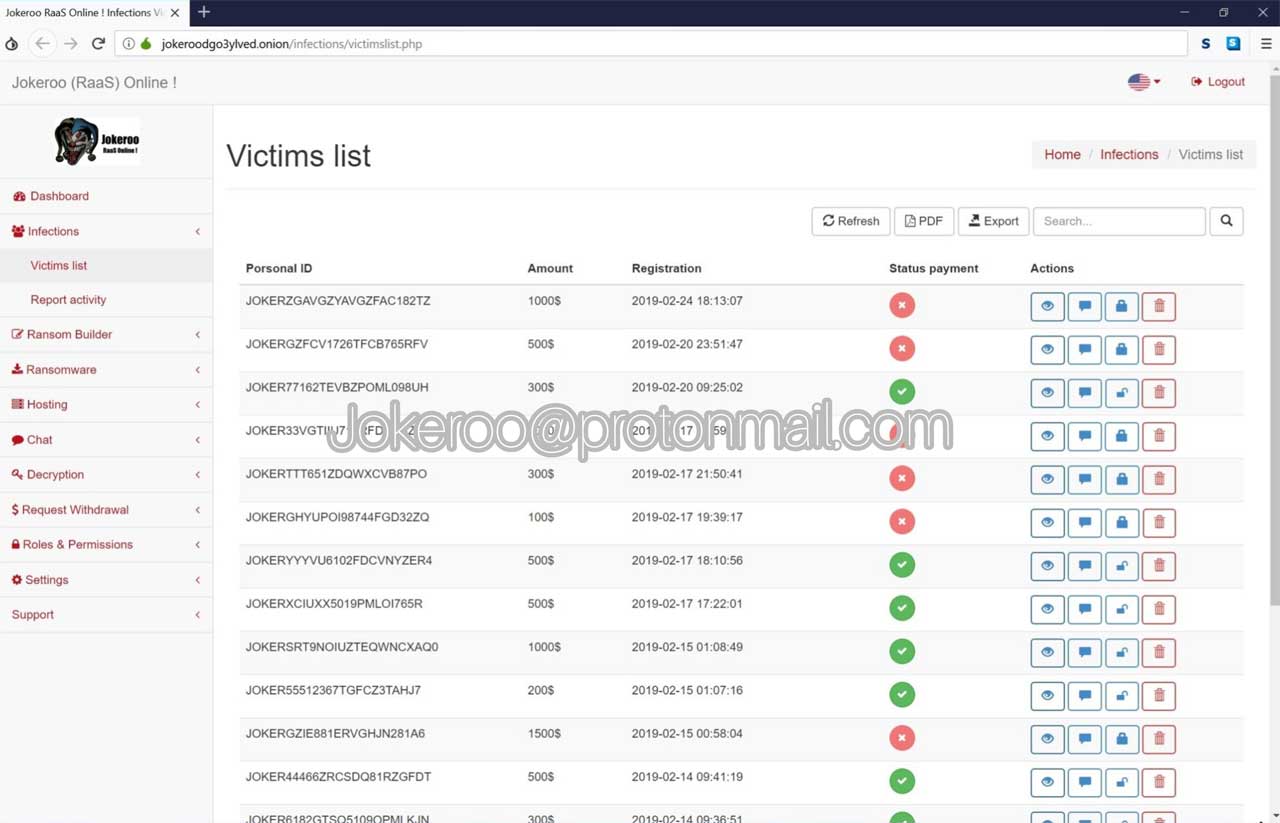
Affiliates will also be able to dig down deeper into the victim list to see their IP addresses, Windows version, and geographic location.
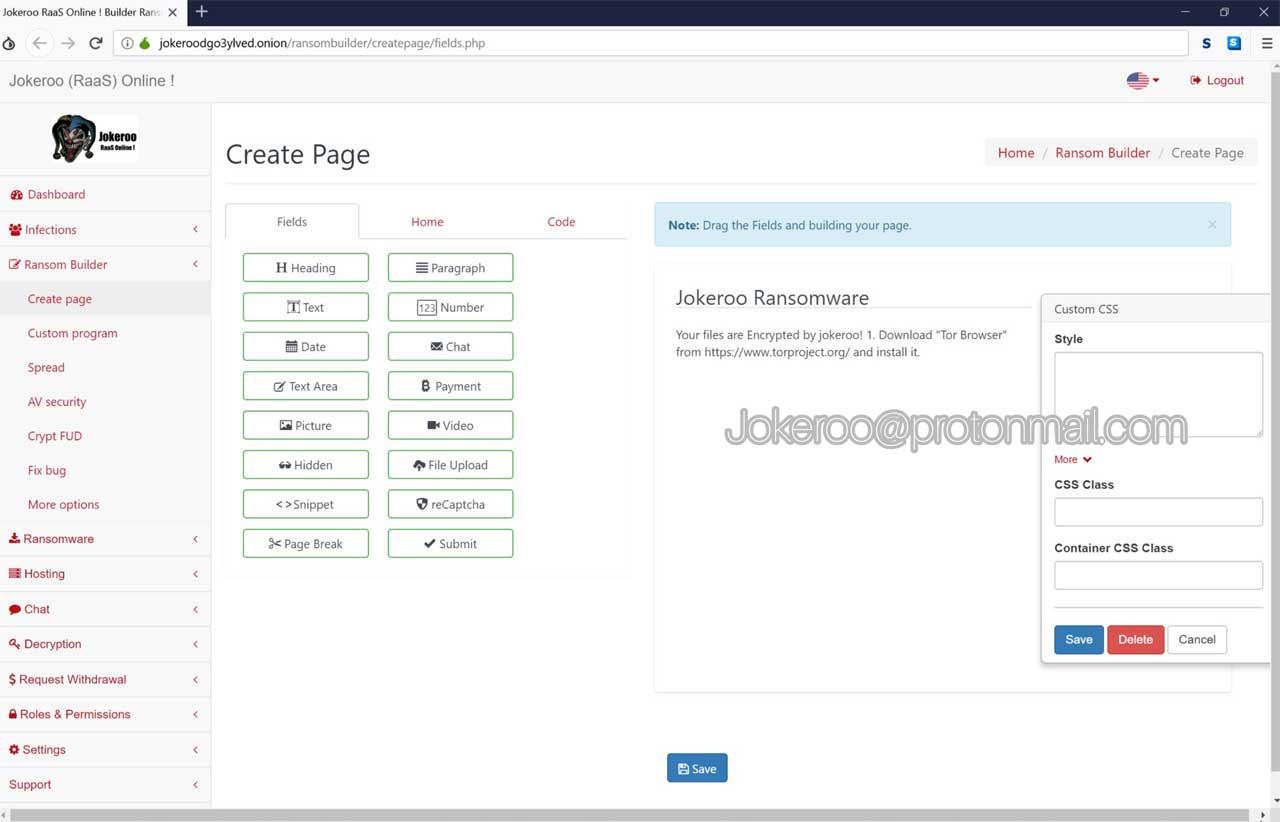
The last picture shows that affiliates can create their own customized ransom note that will be dropped by the ransomware.
Once again, while the RaaS page has been created, there is no indication that this ransomware is currently being distributed. As we get more information, we will update this article.
To read the otriginal article:



