Backdoored SDKs and malicious pre-installed apps the greatest threats…
When Google’s security team identified what they dubbed the “Chamois” malware family in 2017, they noted its unusual complexity and sophistication.
First spotted during a routine advertising traffic quality evaluation, the ad fraud malware was distributed through a range of channels, and had quietly become one of the largest and most multifaceted malicious apps seen on Android to date.
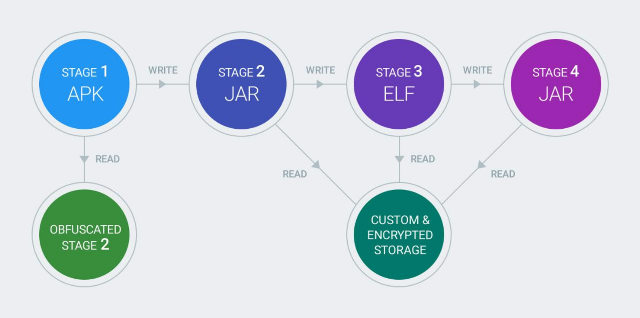
Chamois (named after a mountain goat native to the Pyrenees – and noted for its leather, rather than malevolence) had been rather elegantly coded. It had a four-stage delivery payload; used a range of obfuscation and anti-analysis techniques; custom encrypted file storage for its configuration files; and it was big.
As Android security engineers Bernhard Grill, Megan Ruthven, and Xin Zhao wrote at the time: “Our security teams sifted through more than 100K lines of sophisticated code written by seemingly professional developers [to analyse the malware].”
The malware could drive the traffic of unwitting users to ads, install apps in the background, conduct telephony fraud by sending premium text messages; and was also capable of downloading and executing additional plugins. Now, it’s back.
Android Malware “Chamois” Returns via SDK, Pre-Installation
After its first two variants were detected and disrupted by Google, it re-emerged in November 2017 outside of the Google Play store, and in 2018 was back with a vengeance, hitting a significant 199 million installs last year, according to the annual Android security report [pdf], published today by Google.
“Chamois uses a variety of distribution mechanisms including being pre-installed, added as an advertising SDK [software development kit], and injected into popular sideloaded applications”, the report notes, describing it as a “well-engineered, sophisticated piece of malware”. Google has now identified five variants.
“Google Play Protect classifies Chamois as a backdoor due to the remote command-and-control capabilities it has. The payloads for Chamois range from a variety of ad fraud payloads to SMS fraud to dynamic code loading,” the report notes.
Refreshed detection and remediation techniques once again led to a “sharp decline in installs” in 2018, but the malware looks certain to remerge. (Google Play Protect scans over 50 billion apps every day across more than two billion devices, the report notes: Google has launched a new Play Protect developer site).
Android Malware “Idle Coconut” Adds Your Phone to a Proxy Network
Also among the other malware variants most commonly identified on Android in 2018 was “Idle Coconut”; an SDK that developers include in their apps for monetisation.
“The apps double as end points of a certain commercial VPN [Ed: Computer Business Review has pressed Google for a name] that routes traffic through affected Android devices. The SDKs use a websocket for communications with a command-and-control (CnC) server and then connect to hosts that the CnC commanded over “normal” sockets. None of this behavior is disclosed and the user’s device unknowingly becomes used in a proxy network”, the report notes.
The two greatest threats to Android users in 2018 stemmed from an increase in pre-installed PHAs and backdoored SDKs; the former via supply chain exploits/persuasion of an OEM that an app is legitimate and a welcome addition and/or over the air (OTA) updates that bundle legitimate system updates with PHAs the report notes.
Read this: HolaVPN Network: Unencrypted and Abused?
The annual security report more broadly points to successes including:
- In 2018 only 0.08% of devices that used Google Play exclusively for app downloads were affected by PHAs.
- In contrast, devices that installed apps from outside of Google Play were affected by PHAs 8 times more often. Nevertheless, those devices still saw a 15% reduction in malware rates as compared to the previous year.
- In 2018 Google Play Protect prevented 1.6 billion PHA install attempts from outside of Google Play.
Work to boost Android security further in 2018 included delivery of a strengthened application sandbox; hardened developer APIs; and increased investment in hardware-backed security, Google said in the report.
To read the original article;



