Two zero-day vulnerabilities impacting Microsoft’s Edge and Internet Explorer (IE) browsers could allow an attacker to steal sensitive user information, new research reveals.
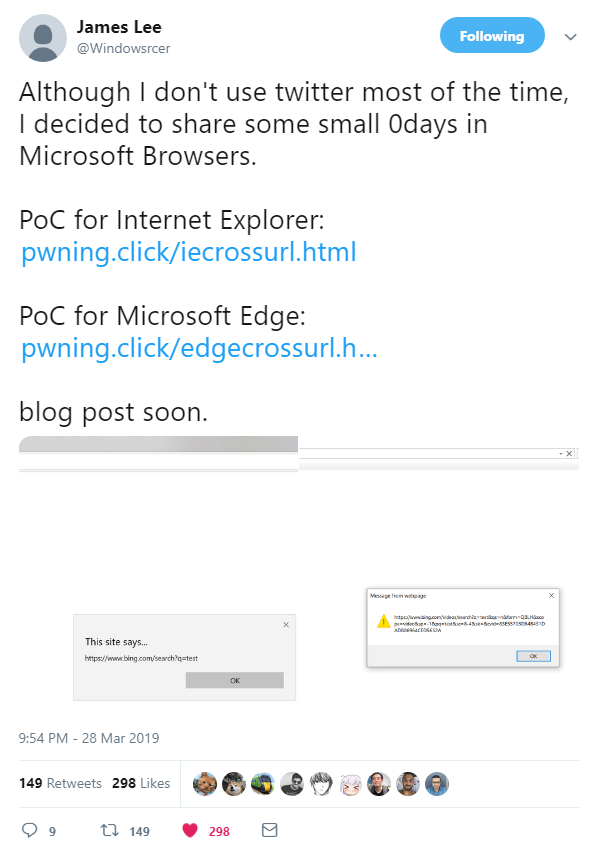
Last week, researcher James Lee took to Twitter to disclose two variants of the same browser exploit, each of which leverages a flaw in the Performance API to bypass same-origin policy in IE and Edge, respectively.
Lee’s proof of concepts – independently verified by The Daily Swig – show how a malicious site containing an <embed> element that links to a specially crafted redirect could force the Performance API to leak URLs.
Found in all browsers, the Performance API is used by web admins to find performance-related information for webpages.
Giving attackers the ability to read URLs cross-domain throws up some pretty serious security concerns because these links could contain sensitive information, such as usernames or any session/OAuth tokens.
According to Lee, his exploit originally worked across all major browsers, although Microsoft is the last vendor to address the vulnerability, which remains unpatched in Edge and IE.
“I reported to MSRC [Microsoft Security Response Center] 10 months ago, yet [there’s been] no reply for both cases and several more upcoming bugs,” Lee said last week.
“I used Twitter for disclosure because MSRC ignored reports for a few months,” he told The Daily Swig. “They handled more severe bugs I sent but kept ignoring [same-origin policy] violation-related issues.”
Just a few hours after the Edge and IE flaws was disclosed, researcher @terjanq used the Performance API to leak whether a site has the X-Frame-Options HTTP response header, cross-domain.
Microsoft’s apparent reticence to address the Performance API flaw suggests the company may no longer be concerned with patching less severe vulnerabilities ahead of Edge’s upcoming shift to the Chromium browser engine.
“I hope MSRC checks security vulnerability reports sent by researchers more thoroughly from now on,” Lee said.
To read the original article:
https://portswigger.net/daily-swig/zero-day-hole-in-microsoft-edge-exposes-users-secrets