Scammers pushing snake oil products compromised hundreds of GoDaddy accounts and used 15,000 subdomains to redirect to spam pages, some of which tried to impersonate popular websites.
The campaigns changed patterns over time but remained sufficiently consistent in some respects to allow automatic identification.
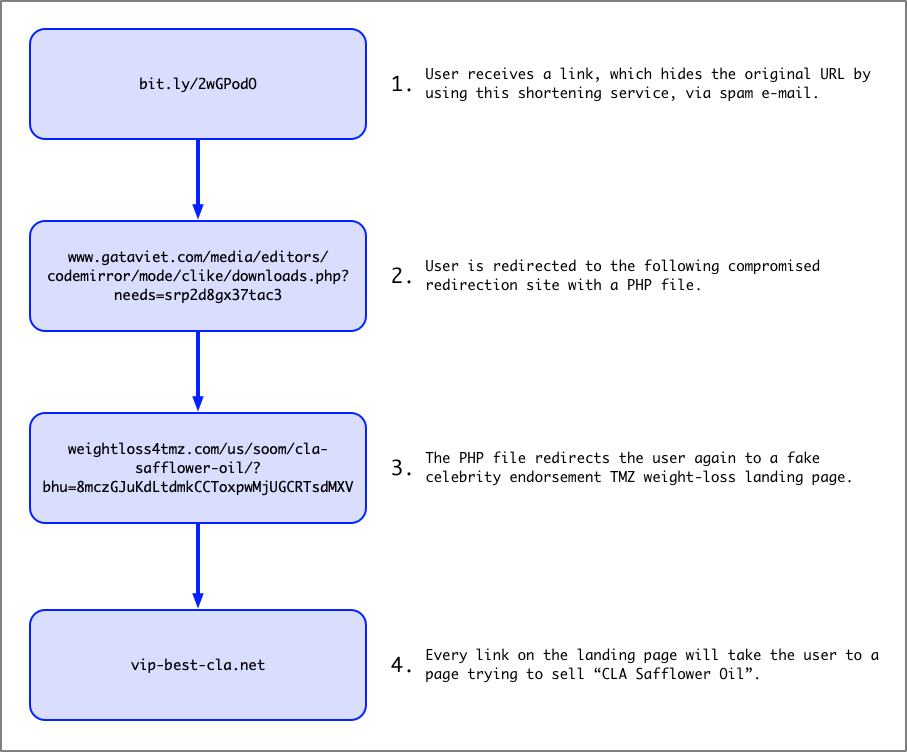
From short link to scam page
Using compromised GoDaddy accounts, the scammers created subdomains with redirection scripts that took the victim to a landing page where they saw a fake celebrity endorsement for the “miracle” product and then to the sale page.
The initial lure would typically come via email and the URL is converted into a short link, to keep the potential victim in the dark about the initial destination.
Jeff White, Palo Alto Networks Unit 42 researcher, spent two years monitoring campaigns that have “scam” written all over them, yet fool a large number of individuals. The products promoted this way range from diet pills to brain boosters and CBD oil.
Getting to know them
Using tools for pattern identification in images and RiskIQ’s PassiveTotal service, White was able to discover multiple redirection styles used in the illegal activity. In many cases, several redirects would occur before the victim reached the final result.
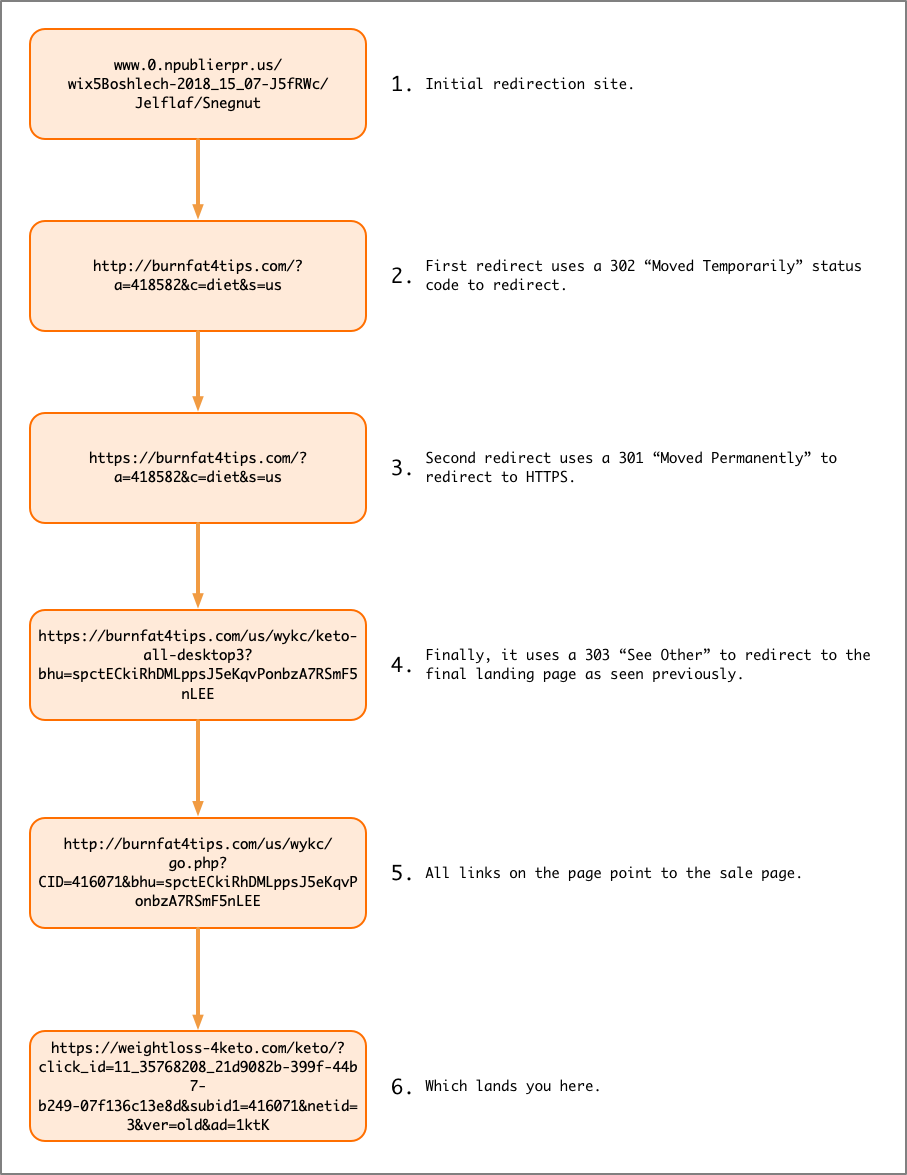
“Using RiskIQ’s PassiveTotal service to pivot on sites that redirected to or from the compromised sites, I was able to map out 689 landing pages that mapped back to a whopping 21,611 potentially compromised websites.”
One Palo Alto Networks customer received hundreds of emails that led to these campaigns. Studying some of the messages to find the origin of the initial URL, White determined there was “similar structure of one simple English word used as a subdomain to an unrelated second level domain.”
From more than 4,000 sites enumerated from PassiveTotal where this naming pattern was visible and were linked to known landing pages, there were 3,000 unique second-level domains and most of them resolved to GoDaddy’s link shortening service.
While similar to other shortening services like Bit.ly, GoDaddy’s allows pointing a DNS A Record to an IP address and define where to forward the user.
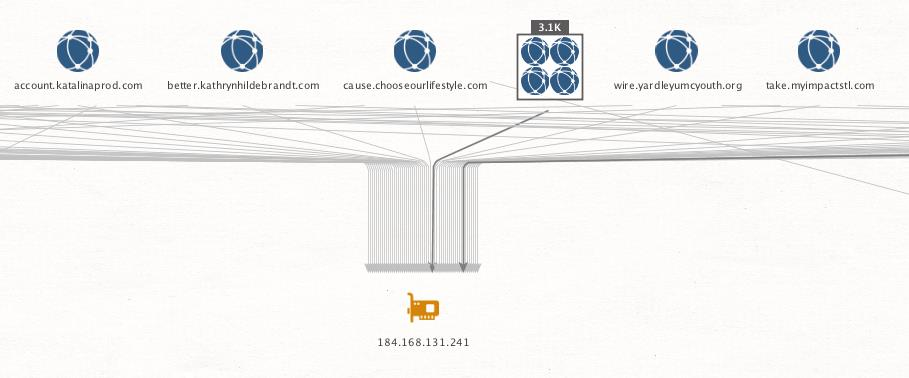
Looking at the scale of the campaigns, White reasoned that the scammers automated the creation of subdomains that pointed to their redirector and generated them using a dictionary of simple English words.
Shady affiliate marketing business
Looking at the large collection, White realized that the activity is part of affiliate marketing business, where advertisers pay affiliates to promote products. Basically, an advertiser pays for traffic to head to their sale page.
“Technically, there is nothing wrong with affiliate marketing, but when affiliates use less than scrupulous methods for traffic generation, it puts the onus on the marketing company (merchant and/or affiliate network) to filter out the bad apples,” says White.
Merchants have the capability to track the affiliates engaged in this type of illegal activity but both parties are in on the scheme. Oftentimes, vendors are the ones providing the fake celebrity endorsement templates the affiliates display to potential victims, trying to elicit a click anywhere on the page that takes them to the sale page.
Re-billing clause in the small print
These operations are fueled by a low prosecution rate and large profits, leaving victims to deal with financial losses.
After ensnaring the victim with the fake endorsements, the scammers will try to convince them to try a sample of the product, asking in return only the shipping costs.
Hidden in fine print, though, is a line informing that it’s a subscription-based deal that is renewed automatically until the victim cancels it.
Multiple billing cycles can pass this way and if the victim tries to cancel the subscription they are stonewalled. With no one answering their calls, the victim takes the issue to the bank to cancel the charges.
Based on the large dataset, White was able to identify recurring patterns for these campaigns and contacted GoDaddy’s Threat Intelligence team to stop the illegal activity.
“After writing some new scripts to automate and collect shadow domains for these campaigns and working with GoDaddy’s abuse teams, we were able to successfully identify and shut down over 15,000 subdomains being used across these campaigns,” White writes in a detailed report of his research.
To read the original article:



