The malicious actors behind the DDoS attacks against Electrum Bitcoin wallet users have switched to a new malware loader for their botnet Trojan, after previously using the Smoke Loader tool and the RIG exploit kit.
Since the attacks targeting Electrum’s infrastructure have begun, Malwarebytes Labs’ research team estimates that “the amount of stolen funds has increased to USD $4.6 million.”
Botnet reached a maximum of 152K bots
In addition, the botnet used to launch the DDoS attacks has reached a maximum of 152,000 compromised machines, with a plateau of 100,000 according to a public online tracker monitoring clients attacking electrumx servers.
As shown in the graphs above, while the researchers have been able to only find three methods the bad actors have used to distribute the ElectrumDoSMiner payload onto Electrum users’ machines, the number of malicious binaries designed to download the Trojan could very well be in the hundreds.
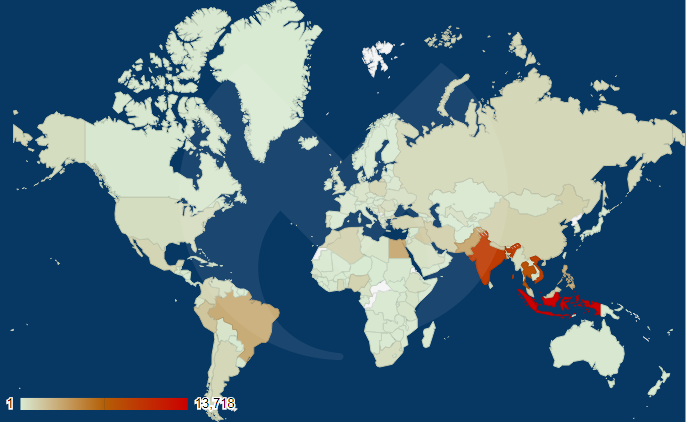
Further analysis also showed that the infected machines forced to be part of the Electrum DDoS botnet are mostly from the Asia Pacific region (APAC) and from South America (Brazil and Peru).
“We believe as some machines get cleaned up, new ones are getting infected and joining the others to perform DoS attacks. Malwarebytes detects and removes ElectrumDoSMiner infections on more than 2,000 endpoints daily,” state the MalwareBytes Labs researchers.
The MalwareBytes Labs’ team provides a list of Indicators of Compromise, including ElectrumDoSMiner infrastructure IP addresses and a Trojan.BeamWinHTTP binary hash. Additionally, ElectrumDoSMiner infrastructure binary hashes can be downloaded from HERE.
In related news, US and EMEA security professionals said that DDoS attacks are seen as the biggest threats to their organizations, with approximately half of the companies having been attacked during 2018.
Another 75% of interviewed professionals stated that they are deeply concerned about “bot traffic (bot robots and scrapers) stealing company information, despite the same number already deploying a bot traffic manager solution.”
To read the original article:



