skimming devices is thriving and changing at the rate of technological advancements.
Card skimming is when cybercriminals add their own spying equipment to an automated teller machine (ATM) or point-of-sale system (PoS) to copy the information they process from credit or debit cards.
Offline carders organize in closed networks
Known as “real/offline carding,” this technique is ancient and has been giving headaches to both banks and the customers that got their cards copied.
Closed communities of professional skimmers have evolved into networks that provide both logistics and information for running card skimming operations. They have engineers, cashers, extractors, technicians, decoders, and vendors, all contributing their expertise, products, and services.
.png)
The typical targets include ATMs, PoS terminals, and gas stations, according to a report from Advanced Intelligence (AdvIntel) a fraud prevention company based in New York.
Exclusive skimming networks rely on technological advancements to develop, upgrade, and sell top-of-the-line products that are both powerful and stealthy.
Audio skimmers
Yelisey Boguslaskiy, director of security research at AdvIntel, monitored these markets and noticed a preference among criminals for audio skimmers. This was based on information from reputable shops and source intelligence.
At a price of about $1,500, audio skimmers are not a new thing. They’ve been around since 2010 and the method they used has been mentioned as early as 1992.
These devices capture the data and usually encrypt it, then store it in MP3 format. Because of the encryption, that price is just the first payment as sellers also charge for the decryption, otherwise the data is useless and cannot be used cloning cards or for online purchases.
Fast swiping with upgraded version
Audio skimmers turn into a more potent kit when they are fitted with a camera that captures the card PIN number, becoming what is known as a video skimmer. The set is popular on the Russian-speaking underground forums because they can be installed quicker.
Flash audio skimmers are the upgraded variant of audio skimming gadgets and can cost more than $2,000.
“They use timing-calculating algorithms to “reed” the audio when the card is been scanned by the ATM, which allows them to decode a track in 1-2 seconds and immediately convert it into text format,” Boguslaskiy explains.
Furthermore, they can run uninterrupted for more than 20 hours and have a recording capacity of 500 dumps – that is full data from the tracks on the card’s magnetic stripe.
Smartphones and Bluetooth technology have also seen increased adoption among Russian skimmers. Boguslaskiy says that one actor offered instructions on how to build a skimming assembly using an off-the-shelf Bluetooth card reader and an Android smartphone.
.jpg)
Basically, the skimmer sends the information it captures to the smartphone. This way, the fraudster can touch the ATM only once and then sit in its vicinity to receive the dumps.
The researcher says that the trend is clearly against flash skimmers, a cheaper variant ($300-$500) that fits into the bezel of an ATM to read the cards. The reason is that they are not as efficient as the audio version.
Apart from being more vulnerable to radio jamming and jittering, they have a low reading rate of just up to 50% of the cards.
Dedicated shops
Sellers of card skimming ‘ware’ have dedicated websites where they offer all the kits necessary for slurping data on the card when clients put their plastic in an ATM.
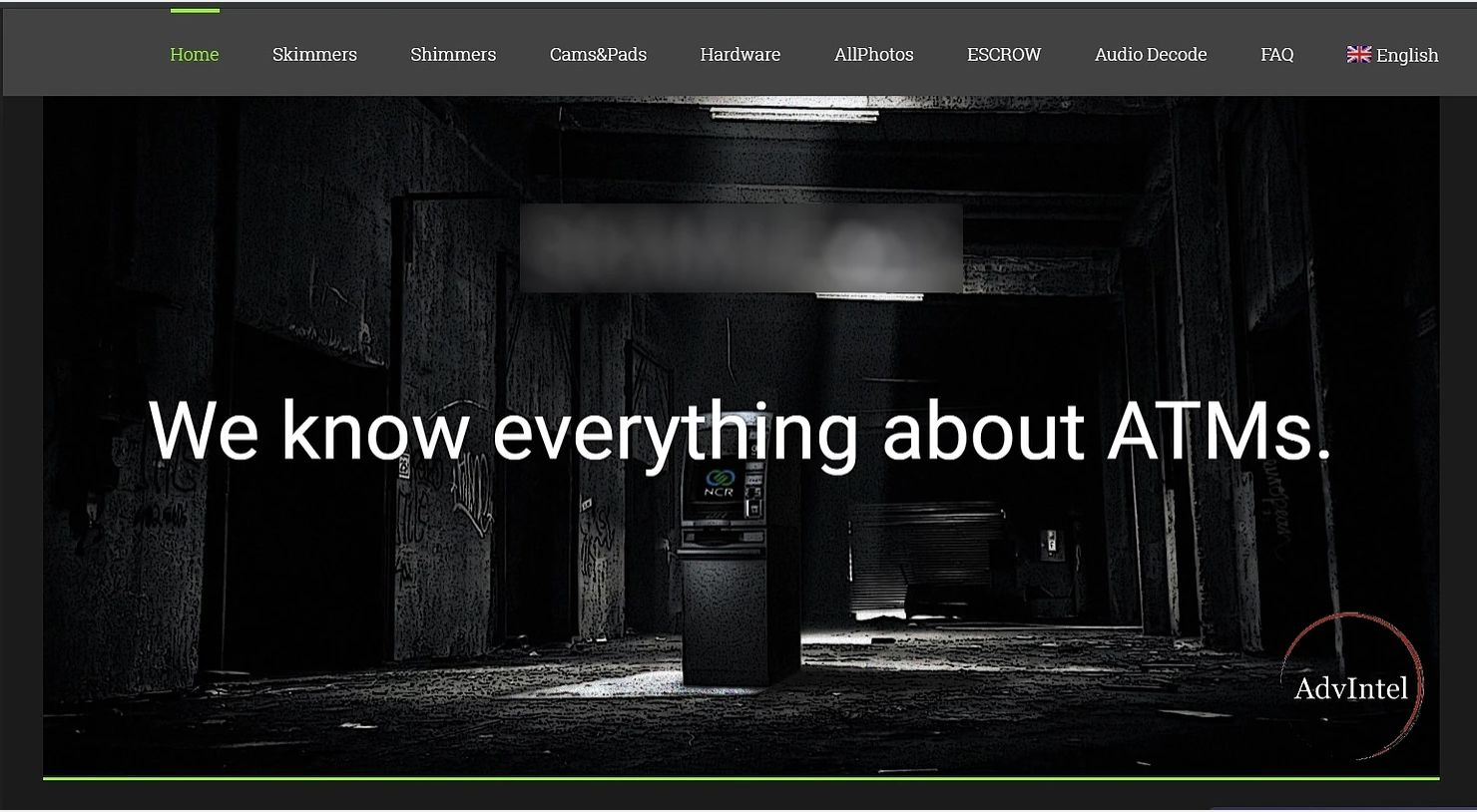
Technological advancements give “lone-wolf” cybercriminals the opportunity to build card readers using off-the-shelf components. This offers them a ticket to enter private circles, some them in the business for more than 10 years.
“Russian-speaking real carding communities have traditionally been exclusive and tight-lipped regarding their skimming operations. Skimming developers form exclusive trusted underground criminal networks thereby connecting talented engineers, their trusted sellers, and wealthy carder buyers of such tools,” says Boguslaskiy.



