Hundreds of million computers from many vendors may have been exposed to hack due to a serious flaw in PC-Doctor software.
Experts at SafeBreach discovered that the Dell SupportAssist software, that comes preinstalled on most Dell PCs, was affected by a DLL hijacking vulnerability tracked as CVE-2019-12280. The flaw could have been exploited by an attacker with regular user permissions to execute arbitrary code with elevated privileges by planting specially crafted DLL files in specific locations.
SupportAssist is used to check the health of systems’ hardware and software when an issue is detected it sends necessary system state information to Dell for troubleshooting to begin.
Obviously, thee checks require elevated privileges because many services run with SYSTEM permissions.
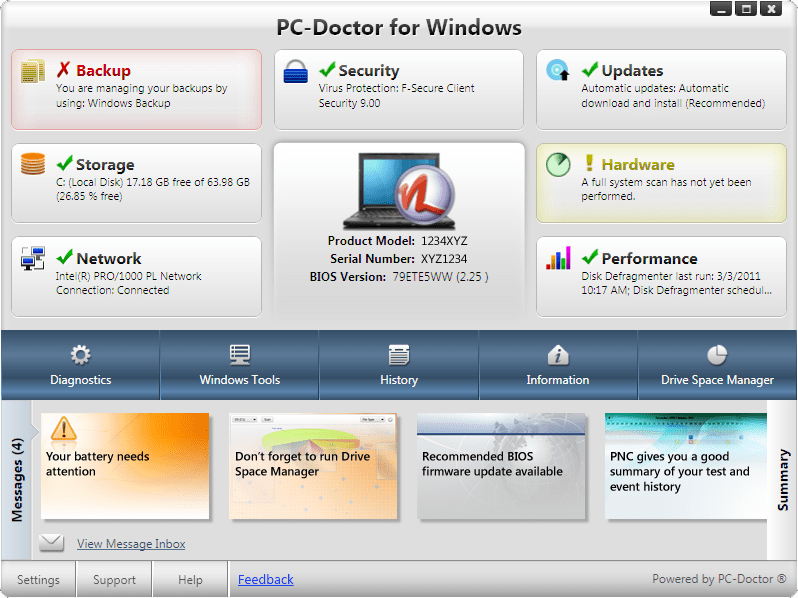
According to the experts, SupportAssist leverages a component developed by the PC-Doctor company to access sensitive low-level hardware (including the physical memory, PCI and SMBios).
Experts discovered that just after the Dell Hardware Support service starts, it executes DSAPI.exe which in turn executes pcdrwi.exe. Both executable run with SYSTEM privileges.
Then the service executes several PC-Doctor executables in order to collect system information. The executables are regular PE files using the extension – “p5x”.
Three of the p5x executables attempt to find the following DLL files on the user PATH environment variable: LenovoInfo.dll, AlienFX.dll, atiadlxx.dll, atiadlxy.dll.
Experts discovered that in their test environment, the path c:\python27 had an ACL which allowed any authenticated user to write files onto the ACL. This means that it was possible to escalate privileges and allow a regular user to write the missing DLL file and achieve code execution as SYSTEM.
“The vulnerability gives attackers the ability to load and execute malicious payloads by a signed service.” reads the post published by Safebreach.
“This ability might be abused by an attacker for different purposes such as execution and evasion, for example:
- Application Whitelisting Bypass
- Signature Validation Bypassing”
The root causes for the vulnerability are the lack of safe DLL loading and the lack of digital certificate validation against the binary.
SafeBreach reported the flaw to Dell in late April and a few days later Dell confirmed the issue but pointed out that it affects a SupportAssist component provided by PC-Doctor.
Dell addressed the vulnerability in late May with the release of SupportAssist for Business 2.0.1 and SupportAssist for Home PCs 3.2.2.
Users received the updates automatically because the software has automatic updates enabled by default.
Now considering that PC-Doctor is pre-installed on over 100 million computers worldwide the extent of the problem could be huge. SafeBreach researchers discovered that the flawed component is also present in CORSAIR Diagnostics, Staples EasyTech Diagnostics, and Tobii I-Series and Tobii Dynavox diagnostic tools.
To read the original article:
https://securityaffairs.co/wordpress/87490/breaking-news/pc-doctor-component-flaw.html



