Riltok is one of numerous families of mobile banking Trojans with standard (for such malware) functions and distribution methods. Originally intended to target the Russian audience, the banker was later adapted, with minimal modifications, for the European “market.” The bulk of its victims (more than 90%) reside in Russia, with France in second place (4%). Third place is shared by Italy, Ukraine, and the United Kingdom.
We first detected members of this family back in March 2018. Like many other bankers, they were disguised as apps for popular free ad services in Russia. The malware was distributed from infected devices via SMS in the form “%USERNAME%, I’ll buy under a secure transaction. youlabuy[.]ru/7*****3” or “%USERNAME%, accept 25,000 on Youla youla-protect[.]ru/4*****7”, containing a link to download the Trojan. Other samples were also noticed, posing as a client of a ticket-finding service or as an app store for Android.
It was late 2018 when Riltok climbed onto the international stage. The cybercriminals behind it kept the same masking and distribution methods, using names and icons imitating those of popular free ad services.
In November 2018, a version of the Trojan for the English market appeared in the shape of Gumtree.apk. The SMS message with a link to a banker looked as follows: “%USERNAME%, i send you prepayment gumtree[.]cc/3*****1”.
Italian (Subito.apk) and French (Leboncoin.apk) versions appeared shortly afterwards in January 2019. The messages looked as follows:
- “%USERNAME%, ti ho inviato il soldi sul subito subito-a[.]pw/6*****5” (It.)
- “% USERNAME%, ti ho inviato il pagamento subitop[.]pw/4*****7” (It.)
- “%USERNAME%, je vous ai envoyé un prepaiement m-leboncoin[.]top/7*****3” (Fr.)
- “%USERNAME%, j’ai fait l’avance (suivi d’un lien): leboncoin-le[.]com/8*****9” (Fr.)
Let’s take a more detailed look at how this banking Trojan works.
Infection
The user receives an SMS with a malicious link pointing to a fake website simulating a popular free ad service. There, they are prompted to download a new version of the mobile app, under which guise the Trojan is hidden. To be installed, it needs the victim to allow installation of apps from unknown sources in the device settings.
During installation, Riltok asks the user for permission to use special features in AccessibilityService by displaying a fake warning:
If the user ignores or declines the request, the window keeps opening ad infinitum. After obtaining the desired rights, the Trojan sets itself as the default SMS app (by independently clicking Yes in AccessibilityService), before vanishing from the device screen.
Now installed and having obtained the necessary permissions from the user, Riltok contacts its C&C server.
In later versions, when it starts, the Trojan additionally opens a phishing site in the browser that simulates a free ad service so as to dupe the user into entering their login credentials and bank card details. The entered data is forwarded to the cybercriminals.
Communication with C&C
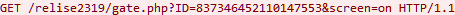
Riltok actively communicates with its C&C server. First off, it registers the infected device in the administrative panel by sending a GET request to the relative address gate.php (in later versions gating.php) with the ID (device identifier generated by the setPsuedoID function in a pseudo-random way based on the device IMEI) and screen (shows if the device is active, possible values are “on”, “off”, “none”) parameters.
Then, using POST requests to the relative address report.php, it sends data about the device (IMEI, phone number, country, mobile operator, phone model, availability of root rights, OS version), list of contacts, list of installed apps, incoming SMS, and other information. From the server, the Trojan receives commands (for example, to send SMS) and changes in the configuration.
Trojan anatomy
The family was named Riltok after the librealtalk-jni.so library contained in the APK file of the Trojan. The library includes such operations as:
- Get address of cybercriminal C&C server
- Get configuration file with web injects from C&C, as well as default list of injects
- Scan for app package names that generated AccessibilityEvent events in the list of known banking/antivirus/other popular apps
- Set malware as default SMS app
- Get address of the phishing page that opens when the app runs, and others
The configuration file contains a list of injects for mobile banking apps – links to phishing pages matching the mobile banking app used by the user. In most so-called Western versions of the Trojan, the package names in the default configuration file are erased.
Through AccessibilityService, the malware monitors AccessibilityEvent events. Depending on which app (package name) generated the event, Riltok can:
- Open a fake Google Play screen requesting bank card details
- Open a fake screen or phishing page in a browser (inject) mimicking the screen of the relevant mobile banking app and requesting user/bank card details
- Minimize the app (for example, antivirus applications or device security settings)
Additionally, the Trojan can hide notifications from certain banking apps.
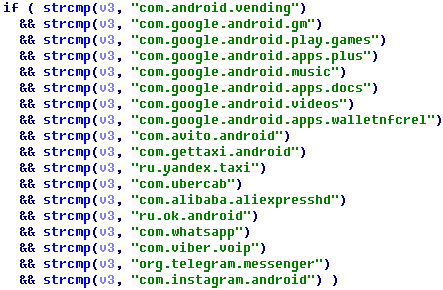
List of package names of apps on events from which the Trojan opens a fake Google Play window (for the Russian version of the Trojan)
When bank card details are entered in the fake window, Riltok performs basic validation checks: card validity period, number checksum, CVC length, whether the number is in the black list sewn into the Trojan code:
At the time of writing, the functionality of most of the Western versions of Riltok was somewhat pared down compared to the Russian one. For example, the default configuration file with injects is non-operational, and the malware contains no fake built-in windows requesting bank card details.
Conclusion
Threats are better prevented than cured, so do not follow suspicious links in SMS, and be sure to install apps only from official sources and check what permissions you are granting during installation. As Riltok shows, cybercriminals can apply the same methods of infection to victims in different countries with more or less the same success.
Kaspersky products detect the above-described threat with the verdict Trojan-Banker.AndroidOS.Riltok.
To read the original article: