The Fin8 organization initially targeted networks of companies in the hospitality and retail industries, but it disappeared from the radar later in 2017. Then in March, cybersecurity researchers began detecting renewed activity from the FIN8 group in the hotel industry, noting that the bad actors had evolved the malware they were using to steal data from the POS devices.
That evolution is continuing with the introduction of Badhatch, which creates a backdoor, according to Gigamon researchers. In a blog posted Tuesday, the Gigamon researchers also outlined other variants of malware the hacking group has used, such as ShellTea, a backdoor also known as PunchBuggy, and PoSlurp – or PunchTrack – a memory scraper tool.
What all this shows is a hacking operation that continues to change and adapt its tools, according to Justin Warner, director of applied threat research at Gigamon.
“The variations in the FIN8 tools highlight the human element of cybercrime; FIN8 is a business with developers who modify their products to fit the needs of their users and drive success of a specific use case,” Warner tells Information Security Media Group. “The constant evolution and modification of their toolset speaks to the adaptiveness and likely dynamic nature of the group and certainly sets them apart from many financially motivated actors that leverage the same tools in the same exact configurations for every campaign. While they are set apart, this does not necessarily make them more ‘sophisticated’ or successful. They just approach the problem differently.”
The Return of FIN8
FIN8 caught the attention of cybersecurity researchers at FireEye and other companies following a number of attacks in 2017. At the time, FIN8 used the ShellTea backdoor to access networks of companies in the hospitality and retail sectors, taking aim at POS devices. The group used malware called PoSlurp to scrape credit card and other payment data from the devices.
FireEye researchers found that the group targeted hotels because the POS systems they use often run embedded versions of Microsoft Windows 7 operating system, which often isn’t updated or patched. POS systems also don’t tend to use anti-virus products, researchers noted.
When FireEye detected FIN8’s re-emergence in March, it noted several improvements to the group’s malicious tools that were aimed at making them more difficult to detect.
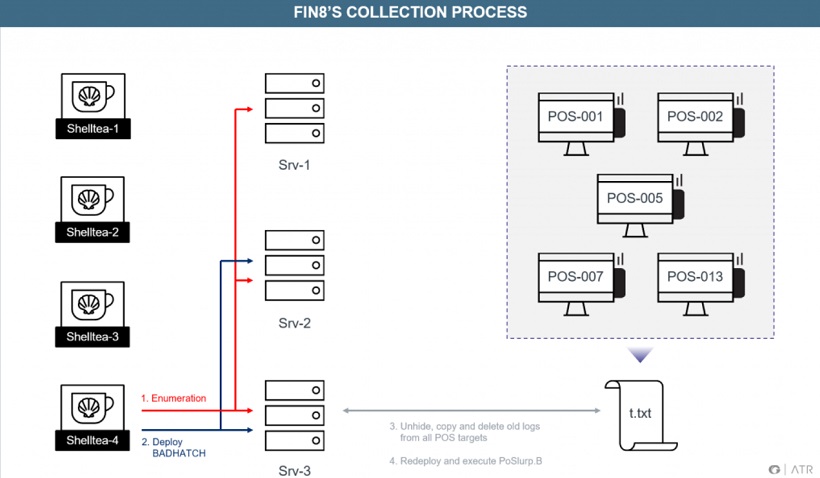 (Image: Gigamon)The campaigns that use the newer Badhatch malware begin like other FIN8 campaigns, with phishing emails aimed at getting someone to click on the message, according to the Gigamon researchers. Once someone clicks on the attached malicious Microsoft Word document, a PowerShell command downloads a second PowerShell script that includes the installation of a backdoor. The Badhatch PowerShell script at first appears similar to ShellTea, or PunchBuggy, researchers wrote.
(Image: Gigamon)The campaigns that use the newer Badhatch malware begin like other FIN8 campaigns, with phishing emails aimed at getting someone to click on the message, according to the Gigamon researchers. Once someone clicks on the attached malicious Microsoft Word document, a PowerShell command downloads a second PowerShell script that includes the installation of a backdoor. The Badhatch PowerShell script at first appears similar to ShellTea, or PunchBuggy, researchers wrote.
Badhatch uses a different command-and-control protocol from other malware, according to Gigamon. In addition, it is capable of injecting commands into a variety of processes, starting an interactive shell and downloading and uploading files from user-supplied paths.
It also doesn’t appear to use any sophisticated methods to avoid sandbox detection, researchers found.
“Badhatch, like ShellTea, is a backdoor that enables attackers to remotely control victim systems through a dedicated command-and-control channel,” Gigamon’s Warner says. “Where ShellTea is utilized and installed as a persistent and stealthy initial foothold, Badhatch is deployed as a post-compromise tool providing the attackers an interactive reverse shell. The use of a secondary post-compromise backdoor is common in many attack chains as it provides an additional foothold should one tool of their arsenal be discovered. Badhatch utilizes techniques relatively common amongst malware, specifically backdoors, and does not go out of its way to evade defensive mechanisms.”
Warner said there have been variations in FIN8’s tradecraft, but essentially the group gains access to a company’s network via phishing and then moves laterally through internal corporate systems, persistently planting backdoors as needed. Along the way, the PoSlurp POS scraping tool is remotely deployed to areas where it can access sensitive card data.
“In many cases, depending on implementation, sensitive card data is not only available on the point-of-sale terminal itself, where cards are scanned, but is also available on back-of-house processing systems,” he says.
The method works on payment cards where the magnetic stripe is used for a transaction, but the use of an EMV chip, designed to improve the security of transactions, doesn’t guarantee immunity, Warner says. Adoption of cards with chips is increasing, but many retailers still use magnetic stripe-based payment methods.
“Additionally, depending on the specific implementation of the systems in the retailer, some of the card data from a chip-and-PIN transaction might still be processed in a way that enables scraping but will not be as useable to recreate forged cards due to missing cryptographic information stored on the chip,” Warner says. “Despite the partial theft, attackers could still leverage the stolen information to process ‘card-not-present’ transactions, such as online purchases.”
Gigamon says that so far, it isn’t aware of any fraud tied to the use of the stolen information.
Monetary Motivation
FIN8 is part of an active community of financially motivated hacker groups, according to Gigamon. In a recent report, the cybersecurity firm found that 71 percent of breaches were financially motivated and that 39 percent were conducted by organized criminal groups.
Such operations can have a significant return for the hacker groups. A similar organization, called FIN7, reportedly stole more than 15 million credit cards from 3,600 business since first being detected in 2015, generating billions in profits, Gigamon researchers wrote.
“The recent U.S. indictments of members of FIN7, a separate financially motivated group, offer a good glimpse of what some of these groups likely look like behind the scenes: dozens of members operating a small business that profits greatly off the losses of others,” Warner tells ISMG. “Simply stated, offensive operations have a unique economy of scale that on the victim end, sometimes making it feel like you are dealing with something more expansive than reality. Gigamon expects the [FIN8] group to continue their operations, making periodic incremental updates as needed, until their methods are rendered ineffective and they fail to continue profiting from the activities, or until they are discovered and dismantled.”
Money is the key driver, but other factors fuel the success of such groups, including “the conflicting goals of usability and customer satisfaction versus security, the prevalence of flat distributed networks with little to no visibility, etc.,” Warner says. “As organizations continue to gain greater visibility across their enterprise, understand the threats that they face and strategically invest in their organization (people, process, and tech) to defeat these threats, the cost to the attackers will increase and reduce the imbalance of power that primarily favors attackers.”
To read the original article:
https://www.bankinfosecurity.com/fin8-group-returns-targeting-pos-devices-new-tools-a-12819



