A few months back researchers from Tel Aviv University & KU Leuven disclosed serious vulnerabilities named as Dragonblood that reside in WPA3 protocol in last April that enables attackers to steal WiFi passwords.
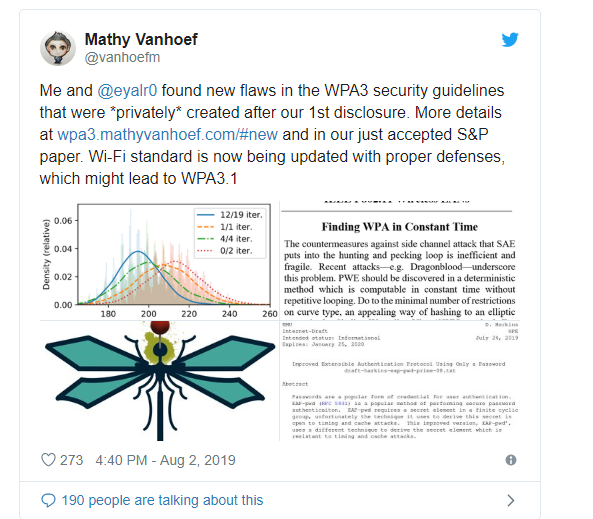
After 3 months, security researchers Mathy Vanhoef and Eyal Ronen discovered new flaws that referred to the second class of side-channel leaks reside in the Dragonfly handshake of WPA3.
WPA3 protocol was recently announced by Wi-Fi Alliance after discovered a severe vulnerability (Krack Attacks) in WPA2. Due to the implementation of powerful Dragonfly handshake in WPA3, Wi-Fi Alliance claims that exploiting the WiFi network that protected by WPA3 and cracks the password is quite impossible.
But the researchers proved that the statement was wrong and discoursed the 2 different design flaw in WPA3 Protocol( Downgrade attacks, Side-channels leaks), and it was patched and released an update by WiFi Alliance.
New Vulnerabilities in WPA3 protocol
1. Side-channel leaks using Brainpool curves (CVE-2019-13377)
Now, researchers reported a new side-channel leak as a first vulnerability that resides in the password encoding algorithm of Dragonfly when it handshake with WPA3 using Brainpoolcurves.
During the process of Dragonfly algorithm tries to find the hash output with Brainpool curves, several iterations may have to be executed before finding a hash output smaller than the prime, but the number of iterations that didn’t have such a valid hash output depends on the password being used and on the MAC address of the client.
“Researchers referred this as a Timing-based side-channel attack against WPA3’s Dragonfly handshake when using Brainpool curves and they confirmed that new Brainpool leak in practice against the lastest Hostapd version, and were able to brute-force the password using the leaked information.”
2. Side-channel leak Information in FreeRADIUS’ EAP-pwd (CVE-2019-13456)
The second vulnerability in WPA3 protocol leaks a piece of information in the EAP-pwd implementation of FreeRADIUS, one of the leading RADIUS servers used in UNIX like operating systems which allows one to set up a RADIUS protocol server.
EAP-PWD is an EAP authentication method, which uses a shared password for authentication and it also helps to find the issues in password-based authenticated key exchange to ensure the implementation of strong shared secret and authentication.
According to the researchers, “More worrisome, we found that the Wi-Fi firmware of Cypress chips only executes 8 iterations at minimum to prevent side-channel leaks. Although this makes attacks harder, it does not prevent them. This strengthens our hypothesis that the backward-compatible countermeasures against our attacks are too costly for lightweight devices.”
To read the original article:



