A new zero-day vulnerability in the for Windows impacting over 96 million users was disclosed by researcher Vasily Kravets.
A news zero-day flaw in the Steam client for Windows client impacts over 96 million users. The flaw is a privilege escalation vulnerability and it has been publicly disclosed by researcher Vasily Kravets.
Kravets is one of the researchers that discovered a first zero-day flaw in the Steam client for Windows, the issue was initially addressed by Valve, but the researcher Xiaoyin Liu disclosed a bypass to the fix implemented by Valve to re-enable to issue.
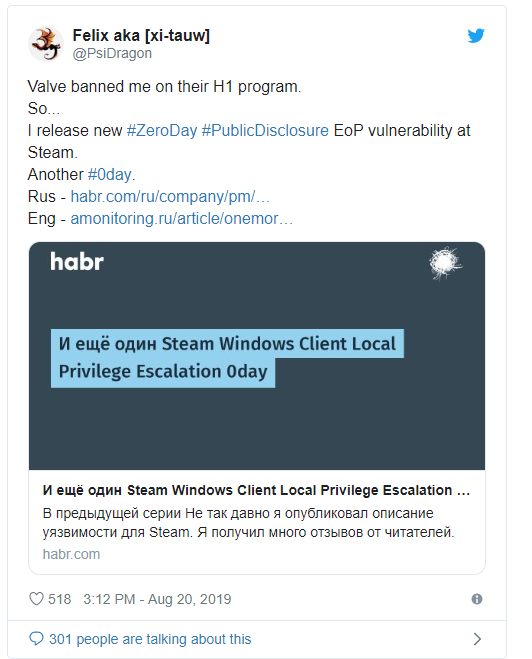
Valve did not award Kravets and banned him from it bug bounty program.
Kravets decided to publicly disclose the privilege escalation that could be exploited by attackers run executables using the privilege of Steam Client Service’s NT AUTHORITY\SYSTEM.
The expert explained that it used the BaitAndSwitch, a technique, that combines creation of links and oplocks to win TOCTOU (time of check\time of use).
The attack scenario sees hackers getting remote code execution privileges by exploiting a vulnerability in a Steam game, a Windows app, or the OS itself, then elevating privileges by triggering this second zero-day to run a malicious payload using SYSTEM permissions.
“As a result any code code could be executed with maximum privileges, this vulnerability class is called «escalation of privileges» (eop) or «local privilege escalation» (lpe). Despite any application itself could be harmful, achieving maximum privileges can lead to much more disastrous consequences.” wrote Kravetz. “For example, disabling firewall and antivirus, rootkit installation, concealing of process-miner, theft any PC user’s private data — is just a small portion of what could be done. “
Kravets published the following two PoC videos for this second zero-day flaw in Steam client for Windows. He demonstrated two methods that could be exploited by attackers to gain SYSTEM permissions on any Windows system running an unpatched Steam version.
To read the original article:
https://securityaffairs.co/wordpress/90207/breaking-news/second-steam-0day.html



