A cyber espionage campaign, which may have ties to North Korea, is suspected of targeting foreign ministries, academic institutions and think thanks that are studying or writing reports about the nation’s regime, according to an analysis by the security firm Anomali.
The campaign was discovered after researchers found a phony portal designed to look like the official website of the French Ministry for Europe and Foreign Affairs, according to Anomali. The fake site bears a strong resemblance to the legitimate French government site, diplomatie.gouv.fr, according to the report.
A further investigation of the IP address that hosted the phony French site led to the discovery of other spoofed sites for such organizations as Stanford University in California; the Royal United Services Institute, a U.K.-based think tank; the Congressional Research Service, a U.S.-based think tank; as well as five email service providers, according to the report.
The Anomali researchers believe the attackers likely sent phishing emails to victims to entice them to log onto the fake websites, where their credentials could be compromised, opening the door to espionage. But they did not discover any of the phishing messages.
And while the researchers could not definitively tie the campaign to the North Korea government, they note that there are some links between the infrastructure used in this campaign and malicious tools and techniques tied to other campaigns by threat groups that have suspected ties that country.
Since discovering the campaign earlier this month, Anomali researchers have worked with Microsoft and Google to black-list the phony websites, the report notes.
Malicious Cloning
On Aug. 9, Anomali researchers came across the fake website posing as a login page for a diplomatic portal linked to the French government.
About 12 government agencies associated with the French Ministry for Europe and Foreign Affairs have limited access to the legitimate diplomatic portal, the researchers say. If any government agents or diplomats logged into the phony page, it’s possible that their credentials and passwords were stolen, according to the report.
The researchers traced the IP address hosting the phony French government site to a hosting provider in Japan called Asia Pacific Network Information Center. Within that IP address, the researchers found over 30 subdomains that appeared to spoof legitimate email services, such as Yahoo, Outlook, Ymail and Google, the report notes.
Digging in further, the Anomali researchers found various spoofed sites associated with other governments, think tanks and academic institutions as well as cloud storage providers, the report notes.
These subdomains included a fake site that resembled the legitimate log-in page for the Stanford University’s secure email service for faculty and staff working at the school who are sending “moderate or high risk” data, according to the report. One the university’s areas of interest is North Korea, the report notes.
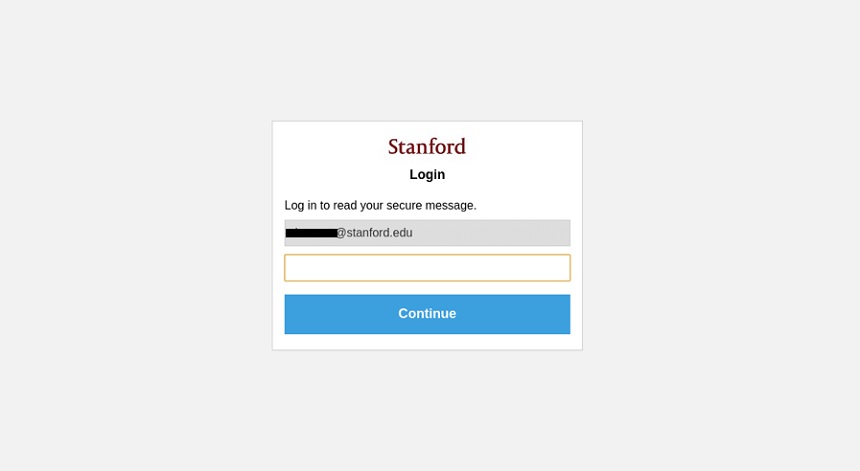
A phony log-in page for Stanford University (Image: Anomoli)
“Stanford University hosts the Center for International Security and Cooperation and the Asia Pacific Research Center – both of which are part of the Freeman Spogli Institute for International Studies,” the researchers note. “These research centers host a number of talks and deliver research on a variety of international issues, including ongoing developments in North Korea.”
The report notes that the motive of the campaign is not clear. “The purpose of this campaign is likely to gain access to the information, but it is difficult to know exactly what the end goal is for the adversary,” it concludes.
North Korean Connection
The researchers found that this newly discovered espionage campaign used tools and techniques similar to those used in an earlier North Korean campaign called ” Smoke Screen,” which security firm ESTSecurity uncovered in in April.
Smoke Screen was a state-sponsored campaign where the threat actor attempted to trick users into opening an email titled “Government official’s remarks about Korea-US Summit,” which contained a malicious document portrayed as containing the remarks, the researchers note.
In that incident, the domain “bigwnet[.]com” was used as a command-and-control server for a Trojan called Kimsuky Babyshark. This malware has been identified by Palo Alto Network’s Unit 42 as having connections to various North Korean campaigns.
The new phishing campaign identified by Anomoli and the previously deployed Trojan share the same IP address, according to security researchers.
The Anomoli report notes, however, that all the targets in these cyberespionage campaigns appear to have a connection to or have looked into work related to North Korea’s nuclear efforts or the international sanctions targeting the country.
North Korean Espionage Activities
In recent years, North Korea has ramped up its cyber capabilities, using them for activities ranging from cyberespionage to theft.
For instance, earlier this month, a leaked UN report revealed that widespread and increasingly sophisticated cyberattacks backed by North Korea enabled the government to divert an estimated $2 billion into developing weapons of mass destruction
To read the original article:
https://www.govinfosecurity.com/cyber-espionage-campaign-uses-spoofed-websites-a-12945



