BadPackets experts observed on August 22 a mass scanning activity targeting Pulse Secure “Pulse Connect Secure” VPN endpoints vulnerable to CVE-2019-11510.
On August 22, BadPackets experts observed a mass scanning activity targeting Pulse Secure “Pulse Connect Secure” VPN endpoints vulnerable to CVE-2019-11510. Recently another popular cybersecurity expert, Kevin Beaumont, has also observed attackers attempting to exploit the CVE-2018-13379 in the FortiOS SSL VPN web portal and CVE-2019-11510 flaw in Pulse Connect Secure.
The CVE-2019-11510 flaw in Pulse Connect Secure is a critical arbitrary file read vulnerability.
“Unauthenticated remote attacker with network access via HTTPS can send a specially crafted URI to perform an arbitrary file reading vulnerability.” reads the advisory.
The vulnerability could be easily exploitable by using publicly available proof-of-concept code.
The scanning activity detected by the honeypots of BadPackets was originated from a host in Spain, threat actors aim at gaining access into the private VPN network.
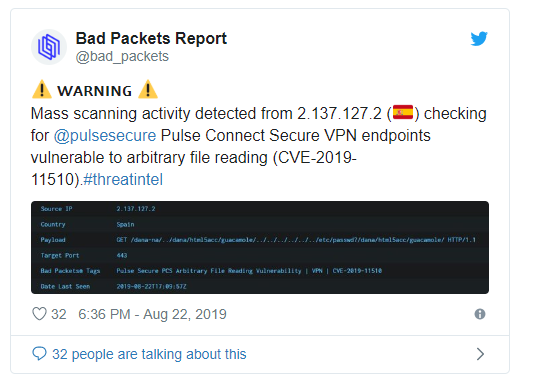
Attackers attempted to download the “etc/passwd” file that contains the usernames associated with the VPN server (not client accounts).
“A successful “HTTP 200/OK” response to this scan indicates the VPN endpoint is vulnerable to further attacks. Given the ongoing scanning activity, it’s likely the attackers have enumerated all publicly accessible hosts vulnerable to CVE-2019-11510.” reads the post published by BadPackets.
BadPackets analyzed the number of Pulse Secure VPN endpoints vulnerable to the CVE-2019-11510. Using the online scanning service BinaryEdge the researchers found 41,850 Pulse Secure VPN endpoints exposed online, 14,528 of them vulnerable to CVE-2019-11510.
Most of the vulnerable hosts were in the U.S. (5,010), followed by Japan (1,511), the U.K. (830) and Germany (789).

The researchers also analyzed the distribution of the vulnerable hosts by industry and discovered that the flaw affects hosts in:
- U.S. military, federal, state, and local government agencies
- Public universities and schools
- Hospitals and health care providers
- Electric utilities
- Major financial institutions
- Numerous Fortune 500 companies
BadPackers did not disclose the list of affected organizations to avoid that threat actors will target them.
“Pulse Secure VPN administrators need to immediately ensure they’re not using versions of the “Pulse Connect Secure” server software vulnerable to CVE-2019-11510. Pulse Secure has provided guidance on how to update to fixed versions.” concludes the post.
To read the original article:
https://securityaffairs.co/wordpress/90356/hacking/pulse-secure-vpn-endpoints-cve-2019-11510.html



