A new ransomware, dubbed Nemty, appeared in the threat landscape over the weekend, it spreads via compromised RDP connections.
A new ransomware, called Nemty ransomware, has been discovered over the weekend by malware researchers. The name of the ransomware comes after the extension it adds to the encrypted file names, the malicious code also deletes their shadow copies to make in impossible any recovery procedure.
Below the ransom note dropped by the Nemty ransomware after the encryption process is completed. Attackers demand the payment of a 0.09981 BTC ransom (roughly $1,000) through a portal hosted on the Tor network.

Source BleepingComputer
“In BleepingComputer’s tests, the ransom demand was 0.09981 BTC, which converts to around $1,000 at the moment.” reported BleepingComputer that first reported the news.
“The payment portal is hosted on the Tor network for anonymity, and users have to upload their configuration file.”
Victims could upload their configuration file, in turn, the operators behind the ransomware will provide with the link to another website that comes with a chat function and more information on the demands.
The popular malware researcher Vitali Kremez discovered that the Nemty ransomware uses an unusual name for the mutex object, “hate.”
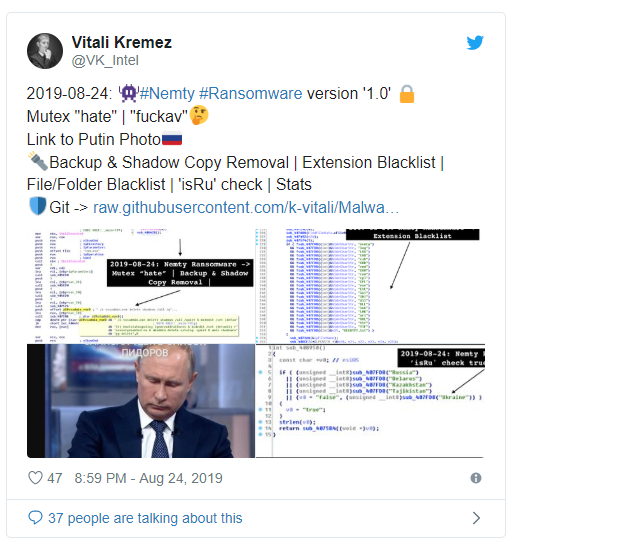

The code also included a link to an image of the Russian President Putin and a message to the antivirus industry.
“Another weird thing Kremez noticed in Nemty’s code is a link to this picture of Vladimir Putin, with a caption saying “I added you to the list of [insult], but only with pencil for now.” continues BleepingComputer.
“At first, the reference seemed an odd thing in the code but a second look at how Nemty worked revealed that it was the key for decoding base64 strings and create URLs is a straight message to the antivirus industry.”
The malware also checks if the ransomware is infecting a computer in Russia, Belarus, Kazakhstan, Tajikistan, and Ukraine, but unlike other threats, this information is not used to halt the encryption process.
According to Kremez, the ransomware is dropped via compromised remote desktop connections.
To read the original article:
https://securityaffairs.co/wordpress/90396/malware/nemty-ransomware.html



