A new Trojan dropper dubbed xHelper was observed while slowly but steadily spreading to more and more Android devices since May, with over 32,000 smartphones and tablets having been found infected in the last four months.
Trojan droppers are tools used by threat actors to deliver other more dangerous malware strains to already compromised devices, including but not limited to clicker Trojans, banking Trojans, and ransomware.
xHelper, dubbed Android/Trojan.Dropper.xHelper by Malwarebytes Labs’ researchers who discovered it, was initially tagged as a generic Trojan dropper only to be upgraded to the rank of a fully-fledged menace after climbing into the security vendor’s top 10 most detected mobile malware in just a few months.
Encrypted and obfuscated DEX packages instead of APKs
Besides the large number of devices it was found on, xHelper also comes with a number of other peculiarities including the fact that it spreads using DEX (Dalvik Executable) files camouflaged as JAR archives, containing compiled Android application code.
This method of infecting new Android devices is quite unique given that most mobile Trojan droppers would use an APK (Android Package) bundled with an infected app, APKs which get subsequently dropped within the Assets folder and then installed and executed on the compromised smartphone or tablet.
The encrypted DEX files used by xHelper as part of its infection process are first decrypted and then compiled using the dex2oat compiler tool into an ELF (Executable and Linkable Format) binary which gets executed natively by the device’s processor.
By using this convoluted technique, the xHelper’s authors drastically lower the chance of having their dropper detected and also conceal their true intentions and end goal.
To analyze the encrypted DEX file, the researchers let it infect an Android device to export the decrypted version from its storage. However, this version was obfuscated and featured variations in source code for all discovered samples, “making it difficult to pinpoint exactly what is the objective of the mobile malware.”
“Nevertheless, it’s my belief that its main function is to allow remote commands to be sent to the mobile device, aligning with its behavior of hiding in the background like a backdoor,” says Malwarebytes Labs’ Senior Malware Intelligence Analyst Nathan Collier.
“Regardless of its true intentions, the clever attempt to obfuscate its dropper behavior is enough to classify this as a nasty threat.”
Stealthy but not really
After analyzing all the samples, the researchers also discovered that xHelper comes in two distinct variants, one that goes through its malicious tasks in full stealth mode and another one designed to work its way semi-stealthily through the compromised Android devices while also showing some hints of its presence.
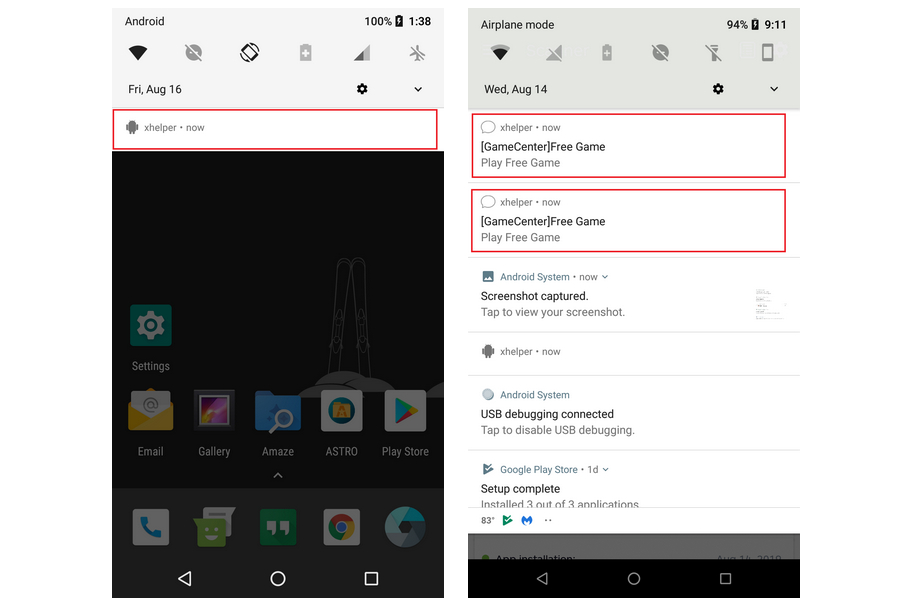
The stealthy variant avoids creating any icons on the infected device and doesn’t show any type of alerts that would reveal its presence, the only sign giving it away being an xhelper listing in the app info section.
The variant with only half of its ninja capabilities enabled is a lot bolder, creating an xhelper icon within the notifications menu and gradually pushing more alerts into the notifications area.
After tapping on one of these notifications, the victims get redirected to websites with browser games which, although harmless, are more than likely allowing the malware operators to collect their share of pay for click profits generated by each visit.
Infection vector still unknown
Given its demonstrated capability of quickly infecting new devices, xHelper is definitely a threat to be taken into consideration. Malwarebytes Labs found it on almost 33,000 mobile devices throughout only four months and that’s only covering the Android devices where Malwarebytes for Android was installed.
As the researchers say, the number of compromised smartphones and tablets is increasing each day, with hundreds of new targets getting infected on a daily basis.
While the precise infection vector has not yet been discovered, “analysis shows that xHelper is being hosted on IP addresses in the United States. One was found in New York City, New York; and another in Dallas, Texas.”
“Therefore, it’s safe to say this is an attack targeting the United States” add the researchers also concluding that “that this mobile infection is being spread by web redirects, perhaps via the game websites mentioned above, which are hosted in the US as well, or other shady websites.”
As a method to prevent getting infected, Malwarebytes Labs recommends being careful while browsing the web on your Android device, cautiously selecting the mobile websites you visit.
Not the first, not the last
This is not the first malware targeting Android users discovered during August, with another Trojan Dropper having been spotted by Kaspersky today in the form of a malicious module hidden within the Android CamScanner app, downloaded over 100 million times from Google’s Play Store.
Doctor Web researchers previously discovered a clicker Trojan bundled within over 33 apps and distributed via Google’s official Android store, also downloaded more than 100 million times by unsuspecting users.
Just last week, yet another Android app including the spyware capabilities of the open-source AhMyth Android RAT was able to bypass Google Play Store’s automated malware protection twice within just two weeks as ESET researchers found.
To read the original article:



