A new ransomware tracked as Lilocked (or Lilu) by researchers is actively targeting servers and encrypting the data stored on them.
The Lilocked ransomware has already infected thousands of Linux-based web servers since mid-July.
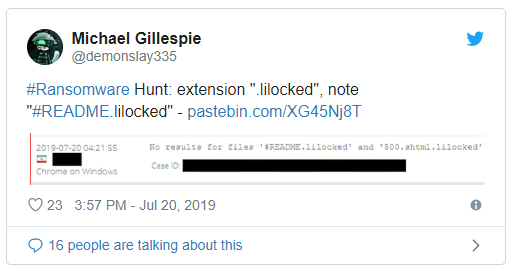
The Lilocked ransomware was first reported at the end of July by the popular malware researcher Michael Gillespie after a sample has been uploaded to his ID Ransomware service.
The infection caused the encrypted files to appear in the Google search results.

According to the Tweet user Jay Gairson, who discovered that his web server, was compromised by this ransomware, the malware leverages an Exim exploit to target the servers.
This thesis is also supported on a thread on a Russian-speaking forum that speculates the hackers have been targeting systems running outdated Exim software.
At the time of writing security experts are searching for a Lilocked sample to analyze to shed the light on its infection process.
The ransomware encrypts files and appends the .lilocked extension to the file name, then it drops a ransom note named #README.lilocked.

The ransom note instructs victims on how to make ransom payments through a Tor payment portal, it also includes a key to log in to the payment site.

The payment portal includes detailed instructions to pay the ransom, including the bitcoin address and ransom amount, that is approximately $100 USD worth of Bitcoin.
“At this time, there is no known way to decrypt files encrypted by Lilu, but if a sample is discovered that may change.” reads the post published by BleepingComputer.
“BleepingComputer has also reached out to the contact email listed on the Tor site with questions, but had not heard back at the time of this publication.
To read the original article:
https://securityaffairs.co/wordpress/90903/malware/lilocked-ransomware-linux-server.html



