FBI’s Internet Crime Complaint Center (IC3) says that Business Email Compromise (BEC) scams are continuing to grow every year, with a 100% increase in the identified global exposed losses between May 2018 and July 2019.
Also, between June 2016 and July 2019, IC3 received victim complaints regarding 166,349 domestic and international incidents, with a total exposed dollar loss of over $26 billion.
| Statistics reported in victim complaints to the IC3 between June 2016 and July 2019: | |
| Domestic and international incidents: | 166349 |
| Domestic and international exposed dollar loss: | $26,201,775,589.00 |
BEC aka EAC (short for Email Account Compromise) fraud schemes are scams carried out by crooks who will wire out funds without authorization to bank accounts they control via computer intrusion or after tricking key employees into doing it using social engineering.
This type of attack targets small, medium, and large businesses alike, as well as individuals, and it has a high success rate due to the fraudsters’ choice to pose as someone that the employees trust like a CEO or a business partner.
“One variation involves compromising legitimate business email accounts and requesting employees’ Personally Identifiable Information or Wage and Tax Statement (W-2) forms,” adds IC3.
The scam behind losses worth billions
Even though the number of BEC scams has also grown, the heightened awareness regarding this type of fraud scheme has also contributed to more reports coming from victims from all over the world which also added to the increased exposed losses reported for the last twelve months.
BEC scams have been reported throughout all U.S. States and in 177 countries around the world according to IC3, with scam-related transfers having been sent to banks from roughly 140 countries.
While accounts from banks from China and Hong Kong were the recipients of the largest share of fraudulent transfers, the FBI has also observed “an increase of fraudulent transfers sent to the United Kingdom, Mexico, and Turkey.”
IC3 derived a number of BEC statistics based on data received from several sources including “IC3 and international law enforcement complaint data and filings from financial institutions between October 2013 and July 2019.”
Based on the number of victim complaints received during October 2013 and July 2019, IC3 saw a total exposed dollar loss of over $10 billion for U.S. victims, and of just over $1 billion for non-U.S. victims.
| BEC/EAC statistics reported in victim complaints to the IC3 between October 2013 and July 2019: | |
| Total U.S. victims: | 69384 |
| Total U.S. exposed dollar loss: | $10,135,319,091.00 |
| Total non-U.S. victims: | 3624 |
| Total non-U.S. exposed dollar loss: | $1,053,331,166.00 |
When it comes to the number of financial recipients of fraudulent transactions stemming from BEC scams, IC3 reports that just over 32,000 recipients from U.S. collected an exposed dollar loss of more than $3 billion, while non-U.S. recipients almost hit $5 billion.
| Statistics reported in victim complaints to the IC3 between June 2016 and July 2019: | |
| Total U.S. financial recipients: | 32367 |
| Total U.S. financial recipient exposed dollar loss: | $3,543,308,220.00 |
| Total non-U.S. financial recipients: | 14719 |
| Total non-U.S. financial recipient exposed dollar loss: | $4,843,767,489.00 |
Payroll diversion schemes with intrusion events are BEC scams
Besides the run-of-the-mill BEC scam where fraudsters redirect wire transfers to their own accounts instead of a business partner, IC3 has also recently started to associate payroll diversion schemes that include an intrusion event with this type of fraud.
This type of scam requires the crooks to first phish for employees’ credentials and then use them to change the victims’ direct deposit accounts to attacker-controlled ones.
“Payroll diversion schemes that include an intrusion event have been reported to the IC3 for several years,” says IC3. “Only recently, however, have these schemes been directly connected to BEC actors through IC3 complaints.”
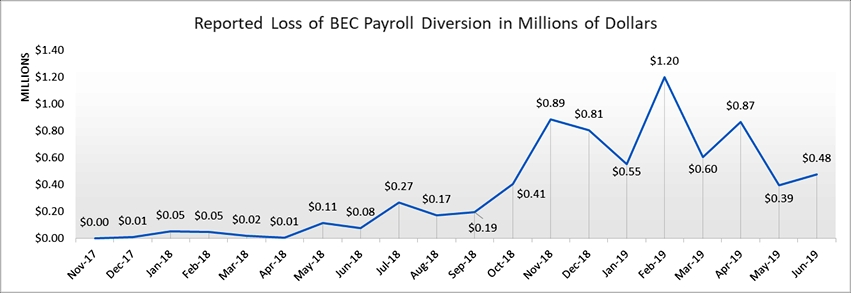
The total reported loss for this scam from January 1, 2018, to June 30, 2019, was of $8,323,354 after analyzing a total of 1,053 complaints received by IC3.
Defensive measures against BEC scams
IC3 provides the following guidelines for employees containing both reactive measures and preventative strategies:
- Use secondary channels or two-factor authentication to verify requests for changes in account information.
- Ensure the URL in emails is associated with the business it claims to be from.
- Be alert to hyperlinks that may contain misspellings of the actual domain name.
- Refrain from supplying login credentials or PII in response to any emails.
- Monitor their personal financial accounts on a regular basis for irregularities, such as missing deposits.
- Keep all software patches on and all systems updated.
- Verify the email address used to send emails, especially when using a mobile or handheld device by ensuring the senders address email address appears to match who it is coming from.
- Ensure the settings the employees’ computer are enabled to allow full email extensions to be viewed.
In addition, to make sure that their employees will not fall victims to BEC attacks, companies have to implement strict vendor processes to check and authenticate payment info changes via multiple types of methods.
This includes both face-to-face meetings and/or direct phone calls when any changes to payment information are being detected.
If you discover that you are the victim of a BEC scam, you have to immediately get in touch with your financial institution “to request a recall of funds and your employer to report irregularities with payroll deposits.”
The FBI also suggests to “file a complaint regardless of the amount with www.ic3.gov or, for BEC/EAC victims, BEC.IC3.gov.”
To read the original article:



