Vulnerability in Click2Gov Software Has Been Patched, Vendor Says.
More than 20,000 payment card records have been harvested from the Click2Gov payment portals of eight U.S. cities in a second wave of attacks that follows a large one last year, according to a firm that tracks stolen payment card data.
Gemini Advisory says the stolen records have turned up on an underground market for sale. The company reached out to the affected cities, which are located in five states. While some did not respond, their Click2Gov portals were subsequently taken offline, Gemini says.
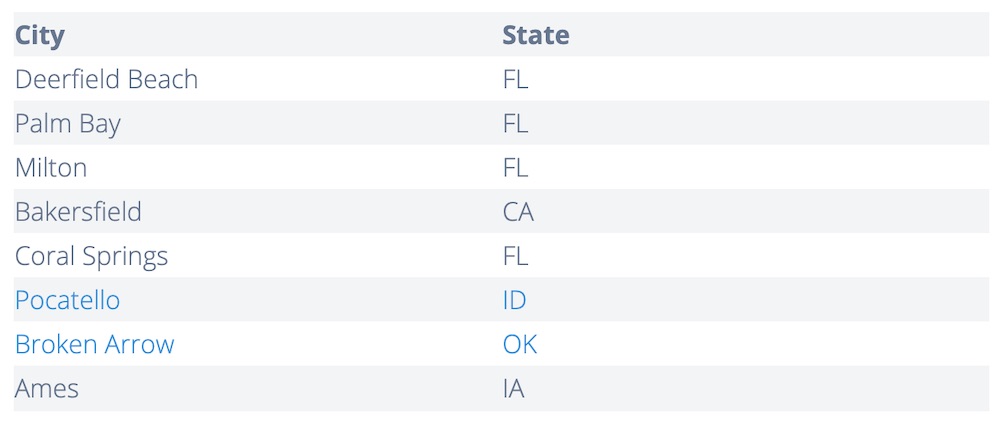 The list of affected cities. (Source: Gemini Advisory)
The list of affected cities. (Source: Gemini Advisory)
Click2Gov, which is developed by CentralSquare Technologies, offers citizens a convenient way to pay their utility bills, parking tickets and other city bills.
CentralSquare Technologies was formed in September 2018 after the merger of Superion, TriTech Software Systems, Zuercher Technologies and Aptean, making it one of the largest software developers for the public sector. Click2Gov was developed by Superion.
In a statement provided to Information Security Media Group, CentralSquare says “a small number” of customers reported unauthorized access affecting consumer credit card data on its customers’ servers. The company says it is working closely with forensic security experts and investigative agencies.
“We have immediately conducted an extensive forensic analysis and contacted each and every customer that uses this specific software, and are working diligently with them to keep their systems updated and protected,” the company says. “At this time, only a small number of customers have reported unauthorized access. For security and confidentiality reasons, we cannot disclose any information about our customers, their environments or their security.”
CentralSquare Technologies, however, gave a more detailed statement to DataBreaches.net. The company acknowledged that the Click2Gov software contained a vulnerability, but says it “existed for a limited number of Click2Gov customers and has been closed.”
The company did not respond to ISMG when asked for confirmation that a software flaw was the cause of the compromises.
Compromises Despite Patching
Gemini Advisory reached out some of the affected cities, which all believed they were running fully patched versions of Click2Gov, says Stas Alforov, Gemini Advisory’s director of research and development.
Some of the cities compromised in the latest attacks were also hit between 2017 and late 2018, when Gemini Advisory reported that 300,000 payment records taken from the Click2Gov systems of 46 U.S and one Canadian city turned up for sale. Gemini Advisory estimated sales of those records generated more than $1.9 million.
 The Click2Gov portal of Laredo, Texas. It was not one of the cities affected.
The Click2Gov portal of Laredo, Texas. It was not one of the cities affected.
Alforov says that since those attacks, cities have become alert and more diligent about patching despite usually having small IT departments. Nonetheless, “if criminals try hard enough, they can break into anything,” he says.
The first round of ClickToGov attacks occurred in 2017 and ran through last year. Superion acknowledged an incident in October 2017 and then wrote an update in June 2018 saying it had helped customers with patching. Superion’s old domain now redirects to CentralSquare website, and the updates appear to only be in the Wayback Machine.
In September 2018, the computer security firm FireEye wrote that it noticed a campaign targeting on-premises installations of Click2Gov. FireEye wrote that it was unsure of how the attackers initially compromised Click2Gov webservers, but they started by uploading a SJavaWebManage webshell.
“Through interaction with the webshell, the attacker enabled debug mode in a Click2Gov configuration file causing the application to write payment card information to plaintext log files,” FireEye wrote. “The attacker then uploaded a tool, which FireEye refers to as FIREALARM, to the webserver to parse these log files, retrieve the payment card information, and remove all log entries not containing error messages.”
A second tool, which FireEye calls SPOTLIGHT, was used to intercept payment card information from web traffic.
“This tool offered the attackers better persistence to the host and continuous collection of payment card data, ensuring the mined data would not be lost if Click2GovCX log files were deleted by an administrator,” FireEye writes.
Who’s Behind the Attacks?
FireEye says the group that attacked Click2Gov last year didn’t appear to be related to other hacking groups it tracks that target the finance sector. It’s possible a single individual conducted the attacks, but it’s more likely that the attacks were the work of a team, the company says.
“Given the manner in which underground forums and marketplaces function, it is possible that tool development could have been contracted to third parties and remote access to compromised systems could have been achieved by one entity and sold to another,” FireEye writes. “There is much left to be uncovered about this attacker.”
Alforov says Gemini Advisory homed in on the second wave of attacks after seeing centralized pockets of payment card billing addresses related to the affected cities, which is somewhat aberrant in underground markets. He says the affected cities are attempting to figure out whose data was compromised and will send notifications.
Card-not-present data, which is the term for payment details for transactions completed without the physical card, is usually put up for sale quickly while it is still valid and could be used for fraud, Alforov says.
To read the original article:
https://www.bankinfosecurity.com/eight-us-cities-see-payment-card-data-stolen-a-13127



