Mobile dropper Trojans are one of today’s most rapidly growing classes of malware. In Q1 2019, droppers are in the 2nd or 3rd position in terms of share of total detected threats, while holding nearly half of all Top 20 places in 2018. Since the droppers’ main task is to deliver payload while sidestepping the protective barriers, and their developers are fully bent on countering detection, this is probably one of the most dangerous classes of malware.
One of the most dangerous and widely spread families of Trojan droppers is Trojan-Dropper.AndroidOS.Hqwar. Originally created as a MaaS infrastructure, today Hqwar is used for both small-scale attacks and big ones affecting thousands of users all over the world.
The very first versions of Hqwar saw the light in early 2016, getting quite popular by the end of the same year. It peaked in Q3 2018, when substantial numbers of financial malware payloads would come “packaged” with this dropper. Yet, beginning Q4 2018, we observe its decline. The likely reason is the tool is not updated frequently enough by its author, causing a customer outflow.
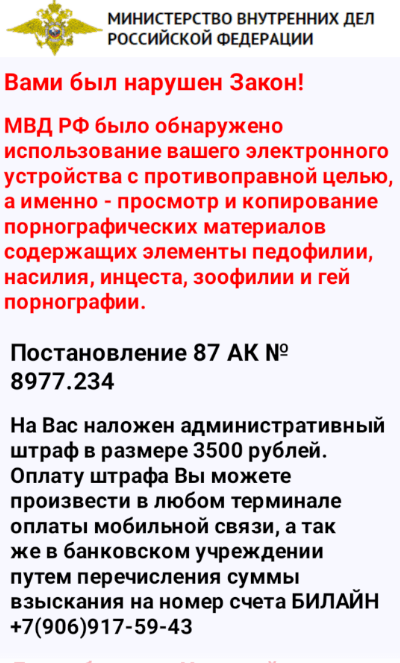
The very first Trojan packed with Hqwar was a piece of ransomware targeting Russian users. This is how this disgrace introduced itself to the victims, impersonating the Ministry of Internal Affairs (note that Hqwar was built by a Russian-speaking author, and many of its clients prey on Russian users):
Now one can say that only the lazy did not use Hqwar: Kaspersky’s collection of viruses features over 200,000 Trojans packed using Hqwar. When decrypting and unpacking these malicious objects, we found that almost 80% of them are financial threats, while nearly one third represent the banking Trojan family of Faketoken. In fact, it was the first ever banking Trojan whose authors began using Hqwar.
The Top 10 list of payloads most often bundled with Hqwar features such widely distributed Trojans as Asacub, Marcher and Svpeng. On several occasions, the dropper was carrying Korean bankers of the Wroba family and such famous SMS Trojans as Opfake and Fakeinst. But their authors seem to have used Hqwar just to try things out, so to speak: these “matryoshkas” did not gain much popularity. All in all, we know of 22 families of different Trojans packed with Hqwar, which shows how much interest cybercriminals take in droppers.
| Family | %* | |
| 1 | HEUR:Trojan-Banker.AndroidOS.Faketoken | 28.81% |
| 2 | HEUR:Trojan.AndroidOS.Boogr | 14.53% |
| 3 | HEUR:Trojan-Banker.AndroidOS.Asacub | 10.10% |
| 4 | HEUR:Trojan-Banker.AndroidOS.Marcher | 8.44% |
| 5 | HEUR:Trojan-Banker.AndroidOS.Grapereh | 7.67% |
| 6 | HEUR:Trojan-Spy.AndroidOS.SmsThief | 7.20% |
| 7 | HEUR:Trojan-Banker.AndroidOS.Gugi | 6.18% |
| 8 | HEUR:Trojan-Banker.AndroidOS.Svpeng | 5.38% |
| 9 | HEUR:Trojan-Banker.AndroidOS.Agent | 5.24% |
| 10 | HEUR:Trojan-Banker.AndroidOS.Palp | 1.97% |
* percentage of all unpacked objects
What’s inside
From the technical viewpoint, the dropper is a wrapper around the payload’s DEX file to be decrypted and loaded, comprising two classes.
If we are to simplify and forget about obfuscation, the dropper’s workflow can be presented as follows:
- open a file from assets;
- decrypt it using RC4 and a hardwired key;
- delegate control with the help of DexClas`sLoader LoadClass.
Everything the unpacked Trojan needs to operate is in the dropper’s APK file: all activity, receiver and service records are written down in the manifest, the pictures are where they should be (with unique names generated for all objects). As Hqwar doesn’t “drop” the APK file but only loads the code, there is no need for an app installation request which can potentially be declined by the user (however, this approach is not exactly good for persistency: once the dropper is deleted by the user, the Trojan is deleted, too). The main Trojan’s body is obfuscated, so the original malware cannot be recognized.
Interesting fact: for some time Hqwar had co-existed with a Trojan called Trojan-SMS.AndroidOS.Fakeinst.hq, with which it had quite a few things in common:
- The two used similar line obfuscation methods (it might be that the authors of both had used a ready-made decryption algorithm).
- A setup was used in which a portion of code was loaded from AES-encrypted asset files. It is worth noting that in Fakeinst.hq one of the encrypted files was an APK file, while the other one was a DEX file used to install a secondary APK (payload). This made for a triple matryoshka: the original dropper at level one, an encrypted DEX file at level two, and an encrypted APK at three. This was done to preserve infection after the dropper itself was deleted. Broadly speaking, the trick is not new, but unlike other similar occasions, Hqwar and Fakeinst.hq used encrypted files with the same extension – DAT.
- In both cases, a similar certificate generation pattern was used:
This evidence proves nothing, of course. But it can be assumed that the author of Hqwar had begun with Russian SMS Trojans, while at the same time working on the “wrapper” infrastructure.
Services
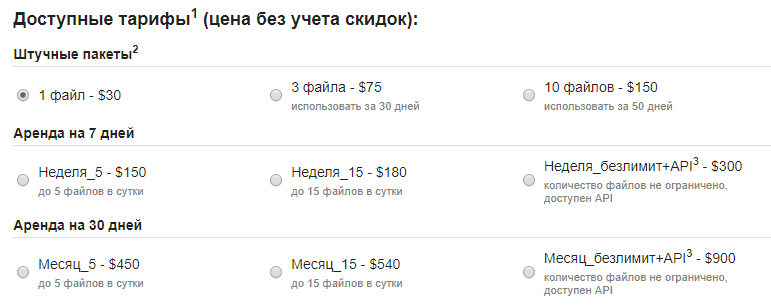
Hqwar owns its popularity to convenient infrastructure and pricing policy (as well as the fact that its maker is still at large and has no fear of being called to account for his actions).
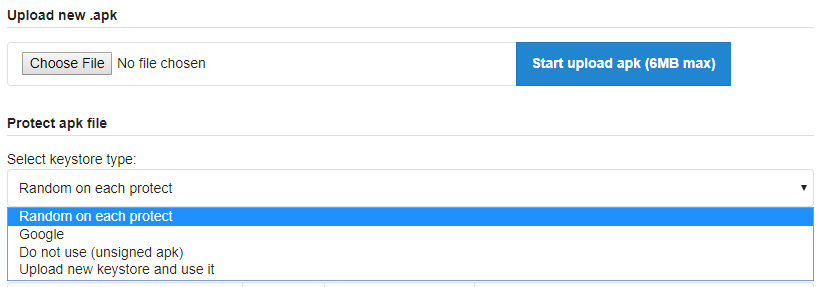
An API exists to have the malware mass-produced. It is likely used by the makers of Trojans like Faketoken, Asacub, Marcher, etc.:
The need to have a certificate for each APK file is one of the places that could give one “a foothold” in Hqwar to reconstruct the certificate generation system. Therefore, the author has made it possible to load a random certificate – either stolen or from a legitimate application.
Conclusion
Despite all the convenient features the dropper’s author has built into it, we believe Hqwar (and similar wrappers) may soon lose much of their popularity: their counter-detection mechanisms have become obsolete, while the structure of the APK file implies there are places that cannot be “littered”, allowing for timely detection of threats (exactly what Kaspersky’s protective solutions are for).
To read the original article:https://securelist.com/hqwar-the-higher-it-flies-the-harder-it-drops/93689/