A Windows Point-of-Sale (POS) malware has been discovered using the DNS protocol to smuggle stolen credit cards to a remote server under attacker’s control.
POS malware is installed on point of sale systems to monitor for payments using credit cards. When a payment is processed on a remote terminal or the local machine, the malware will scrape the credit card information from the computer’s memory and send it to a remote command and control server operated by the attackers.
The attackers then collect the credit card data and use it to make fraudulent purchases, clone credit cards, or sell the data on dark web marketplaces.
Alina POS malware uses DNS to evade detection
When securing POS systems, it is common to lock them down so that they can only connect to specific protocols that are needed. In many cases, these restrictions include locking down the HTTP protocol so that POS systems can’t connect to web servers.
This restriction would prevent the malware from connecting back to command and control servers for POS malware that uses the HTTP protocol to send stolen credit cards.
However, the DNS protocol is not commonly blocked as it is required for a variety of Windows services and the general operation of a machine.
Knowing this, the Alina POS malware has added the ability to use encoded DNS requests to communicate with its command and control server.
In a new report by IT services company CenturyLink, researchers explain how one of their machine-learning models detected unusual DNS queries to a specific domain in April and discovered the Alina POS malware caused it.
“The theft was discovered after one of Black Lotus Labs’ machine-learning models flagged unusual queries to a specific domain in April 2020. Rigorous research determined that the Alina POS malware was utilizing Domain Name System (DNS) – the function that converts a website name into an IP address – as the outbound communication channel through which the stolen data was exfiltrated,” the report stated.
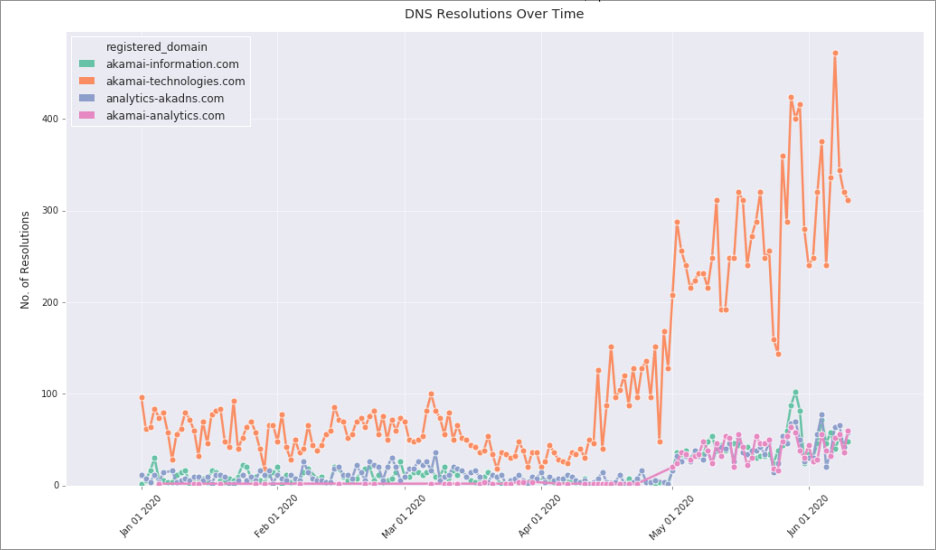
Source: CenturyLink
After further research, they detected that four domains were being used by the Alina malware to talk to the command and control servers over DNS.
analytics-akadns[.]com
akamai-analytics[.]com
akamai-information[.]com
akamai-technologies[.]com
sync-akamai[.]com (not active)Data smuggled using encoded DNS queries
When communicating with the command and control servers, the Alina malware will encode DNS queries and append them to a domain as if they were a subdomain.
For example, below is data encoded and appended as a subdomain to akamai-technologies.com.
yeTLxcbvkOjr6eH_-pCYkPrDxM0.akamai-technologies[.]comWhen the threat actor’s C2 server receives this query, it will decode the encoded subdomain to extract either a PING command, to tell the attackers that the malware is still running, or the stolen credit card information.
“Each of the DNS queries uncovered are either checking in with the C2, such as the “Ping” query above, or they contain credit card information. The queries that contain credit card numbers contain an executable name in the field following the location or descriptor field. This appears to be the process which the malware identified as containing the credit card information in memory,” CenturyLink’s report explained.
If it is a PING, the data will be sent in the format [Victim_id]:[Location]:Ping, as shown below.
cNaolE:BACKTT:2:PingFor queries that contain credit card information, the data will be in the format[Victim_id]:[Location]:[Scraped Process]:[Credit Card Data].
[viYaKNsY:BACKOFFICEz2::ddcdsrv1.exe::CenturyLink observed the following processes being scraped for credit cards and included in the DNS queries:
DSIMercuryIP_Dial.exe
EdcSvr.exe
fpos.exe
Brain.exe
Focus.exe
appidt.exe
ddcdsrv1.exe
fontdvrhost.exe
tcopy.exeThe final data contained in the Credit Card Data section includes the credit card number, expiration date, and an unknown seven digits.
[Credit card digits removed]=DDMMYYYY[Unknown seven digits]With the exfiltrated data being encoded in DNS queries, security software and gateways will be hard-pressed to detect it as malicious.
CenturyLink recommends organizations monitor DNS traffic for repeated suspicious queries to the same domain.
“We recommend all organizations, including retailers using point of sale systems, to monitor DNS traffic for suspicious queries,” CenturyLink suggests.
Alina is not the only malware utilizing DNS to send data to remote servers.
In February, BleepingComputer reported on the new Mozart backdoor malware that was using DNS TXT records for C2 communication.
To read the original article:
https://www.bleepingcomputer.com/news/security/windows-pos-malware-uses-dns-to-smuggle-stolen-credit-cards/



