Hackers are actively exploiting a critical remote code execution vulnerability allowing unauthenticated attackers to upload scripts and execute arbitrary code on WordPress sites running vulnerable File Manager plugin versions.
On the morning of September 1, Arsys’s Gonzalo Cruz was the first to discover the flaw and the fact that it was already being exploited by attackers to upload malicious PHP files onto vulnerable websites.
The File Manager plugin is currently installed on more than 700,000 WordPress sites and the vulnerability impacts all versions between 6.0 and 6.8.
The plugin’s development team patched the severe flaw within hours after the attacks were spotted by Cruz with the release of versions 6.9.
450,000 sites already probed
Cruz also informed Wordfence’s researchers of this ongoing attack, providing them with a working proof of concept and allowing them to look into how to block the attacks.
The WordPress security company later said that the Wordfence Web Application Firewall was able to block out over 450,000 exploit attempts during the last several days.
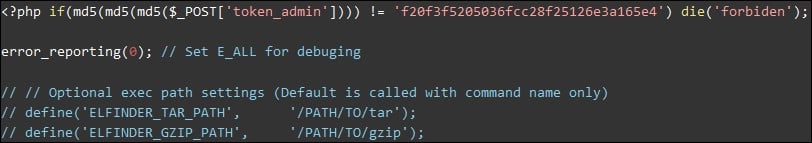
Wordfence said that the hackers are trying to upload PHP files with webshells concealed within images to the wp-content/plugins/wp-file-manager/lib/files/ folder.
They were also seen first probing potentially vulnerable sites with empty files and, only if the attack is successful, trying to inject the malicious scripts.
NinTechNet, who also reported the exploit attempts, said the attackers are attempting to upload a malicious hardfork.php script which allows them to inject malicious code within the WordPress sites’ /wp-admin/admin-ajax.php and /wp-includes/user.php scripts.
What makes the attacks even more interesting is that the hackers will also immediately try to prevent others from compromising an already infected site by password protecting the files exposed to writing by the File Manager vulnerability.
Over 300,000 sites still vulnerable to attacks
“A file manager plugin like this would make it possible for an attacker to manipulate or upload any files of their choosing directly from the WordPress dashboard, potentially allowing them to escalate privileges once in the site’s admin area,” Chloe Chamberland, Wordfence’s Director of Information Security explained.
“For example, an attacker could gain access to the admin area of the site using a compromised password, then access this plugin and upload a webshell to do further enumeration of the server and potentially escalate their attack using another exploit.”
File Manager’s dev team addressed the actively exploited critical vulnerability with the release of File Manager 6.9 yesterday morning.
However, the plugin has only been downloaded just over 126,000 times — including both updates and new installs — within the last two days based on historic download data available on the WordPress plugin portal, leaving 574,000 WordPress sites potentially exposed.
Luckily, only 51,5% of all sites with active File Manager plugin installation (amounting to more than 300,000 websites) are running a vulnerable version that could allow the attackers to execute arbitrary code after successful exploitation.
File Manager users are recommended to immediately update the plugin to version 6.9 as soon as possible to block the ongoing attacks.



