A new ransomware group has been targeting large corporate networks using self-made backdoors and file-encrypting malware for the initial and final stages of the attack.
Researchers are tracking the gang using the codename OldGremlin. Their campaigns appear to have started in late March and have not expanded globally, yet.
Attacks attributed to this group have been identified only in Russia but there is a strong suspicion that OldGremlin is currently operating at smaller scale to fine-tune their tools and techniques before going global.
Custom tools, imaginative phishing
OldGremlin is using custom backdoors (TinyPosh and TinyNode) and ransomware (TinyCrypt, a.k.a decr1pt) along with third-party software for reconnaissance and lateral movement (Cobalt Strike, command line screenshot, NirSoft’s Mail PassView for email password recovery).
The gang is not picky about victims as long they are prominent businesses in Russia (medical labs, banks, manufacturers, software developers), indicating that it’s composed of Russian-speaking members.
The threat actor starts its attacks with spear phishing emails that deliver custom tools for initial access. They use valid names for the sender address, impersonating well-known individuals.
Researchers at Singapore-based cybersecurity company Group-IB says that in one attack against a bank OldGremlin sent out an email under the pretense of setting up an interview with a journalist at a popular business newspaper.
The fake journalist scheduled an appointment using a calendar app and then contacted the victim with a link to alleged interview questions hosted at an online storage service. Clicking on the link downloaded the TinyPosh backdoor.
For another attack targeting a clinical laboratory, the actor impersonated RosBiznesConsulting (RBC), a major media holding company in Russia, that had trouble paying for medical services.
They seem to be well-versed in social engineering and take advantage of current events to make their phishing more credible.
For instance, on August 19 they posed as the CEO of the Minsk Tractor Works informing Russian partners that the company was being investigated for participation in anti-government protests in Belarus and asking them for documents required by the prosecutor’s office.
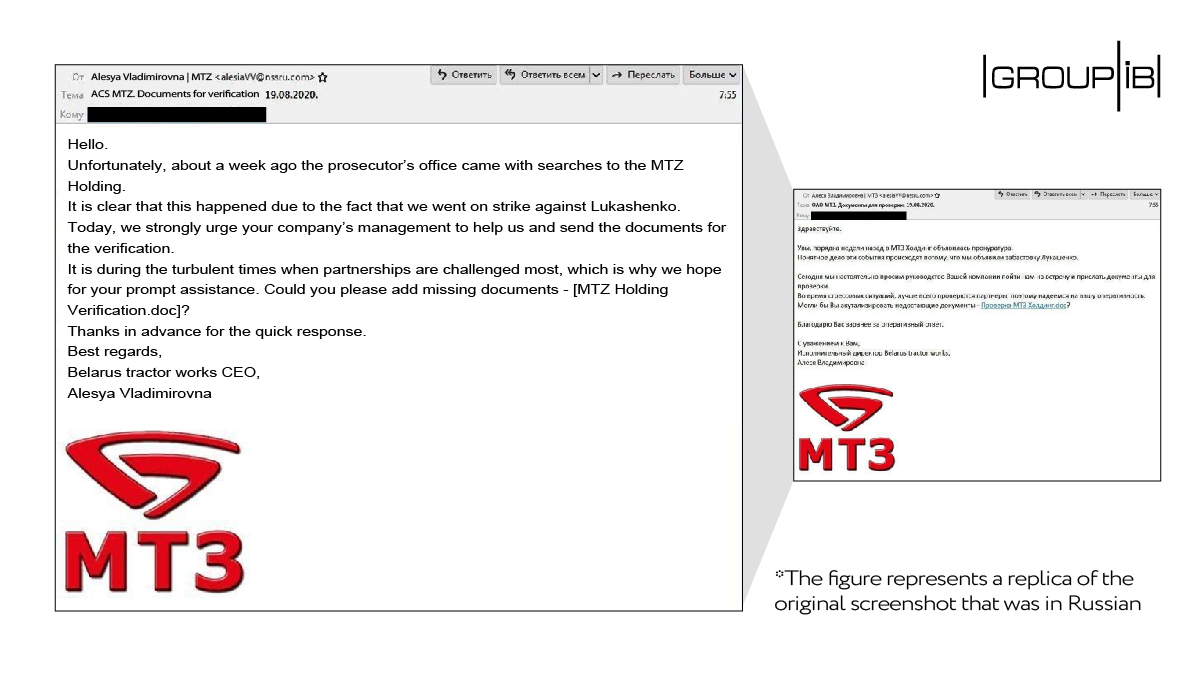
It is worth mentioning that the name used for the sender’s address is not of the factory’s actual CEO. At least 50 messages were sent in this campaign.
The aim is to gain a foothold on the target organization’s network via one of the two backdoors (TinyNode or TinyPosh) that allow expanding the attack via additional modules downloaded from their command and control (C2) server. Remote Desktop Protocol is also used to jump to other systems on the network.
After spending some time on the network identifying valuable systems, the attacker deploys the file-encrypting routine. In the case of the medical laboratory, the attacker obtained domain administrator credentials and created a fallback account with the same elevated privileges to maintain persistence in case the initial one was blocked.
OldGremlin moved to the encryption stage a few weeks after the initial access, deleting server backups and locking hundreds of computers on the corporate network.
The ransom note left behind asked close to $50,000 in cryptocurrency for the decryption key and provided a Proton email address for contact.
In total, Group-IB detected multiple attacks attributed to OldGremlin between May and August 2020, all against targets in Russia, Group-IB told BleepingComputer.

This tactic sets the group apart from other threat actors and was previously seen with financially-motivated groups Silence and Cobalt, which also ran smaller operations in Russia and before moving to targets outside country borders and beyond the former Soviet space.
Typically, Russian hackers avoid attacking organizations in Russia and former Soviet countries. Several big-game ransomware groups and threat actors are adamant about this.
“This indicates that the attackers are either fine-tuning their techniques benefiting from home advantage before going global, as it was the case with Silence and Cobalt, or they are representatives of some of Russia’s neighbors who have a strong command of Russian” – Oleg Skulkin, Group-IB senior Digital Forensics analyst
Skulkin says that OldGremlin is the only Russian-speaking ransomware actor to ignore this rule and that their tactics and techniques are similar to those from advanced hacking groups.
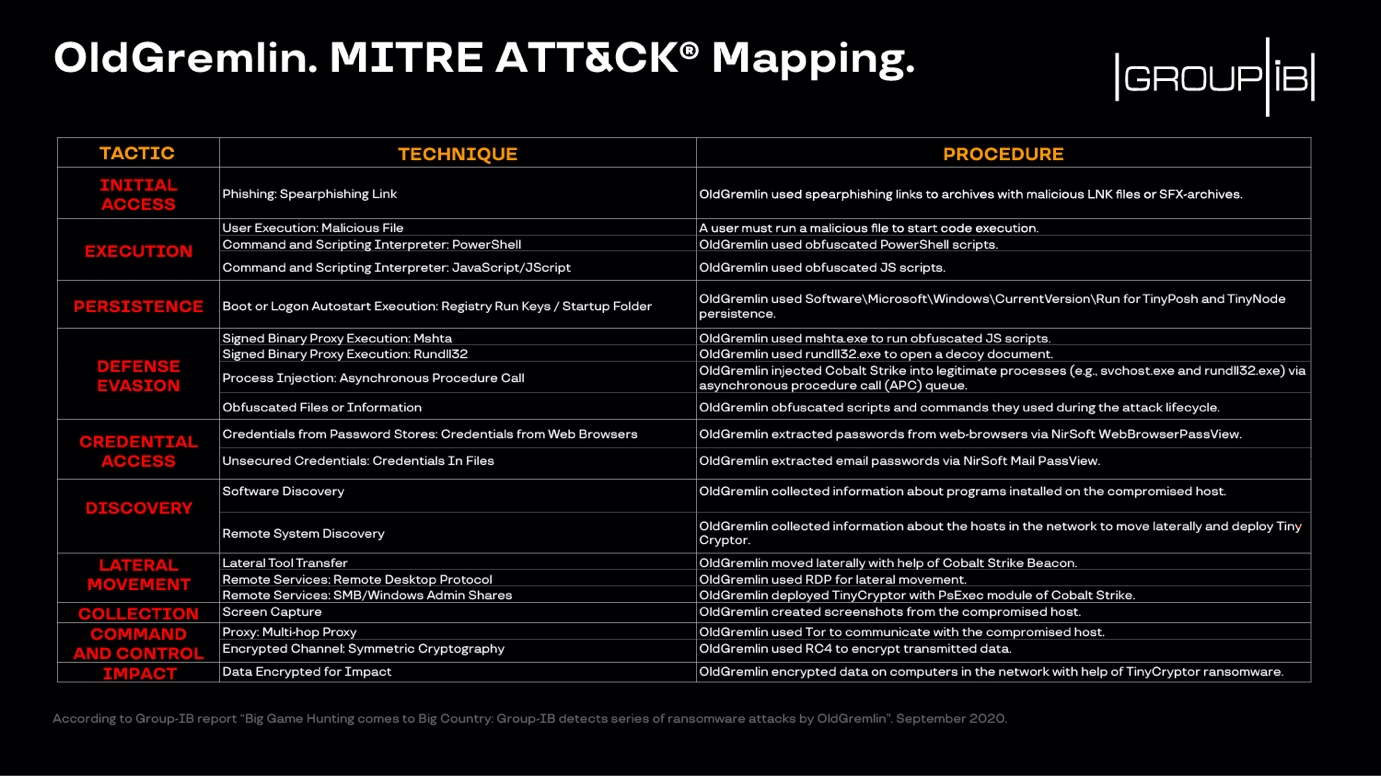
In their blog post today, Group-IB provides a list with indicators of compromise for OldGremlin along with details about the tactics, techniques, and procedures below observed in attacks attributed to this new group.
To read the original article: https://www.bleepingcomputer.com/news/security/new-ransomware-actor-oldgremlin-uses-custom-malware-to-hit-top-orgs/?fbclid=IwAR2oSeCcCN6zvnls0BYop-3EI_b5R7QyCC9qII1QUpnYW0wRc6-jBlFRmes



