Credit card skimming group Fullz House has compromised and injected the website of US mobile virtual network operator (MVNO) Boom! Mobile with a credit card stealer script.
Boom! Mobile provides US-based customers with postpaid and prepaid no-contract wireless service plans that work on the nation’s largest cellular networks including AT&T, Verizon, and T-Mobile.
This type of compromise is known as a MageCart attack (aka web skimming or e-skimming) it consists of threat actors injecting malicious JavaScript scripts within one or more sections of a compromised website.
These scripts are then used by the hackers to steal payment or personal info submitted by the sites’ customers within e-commerce forms.
Boom’s site still infected with malicious scripts
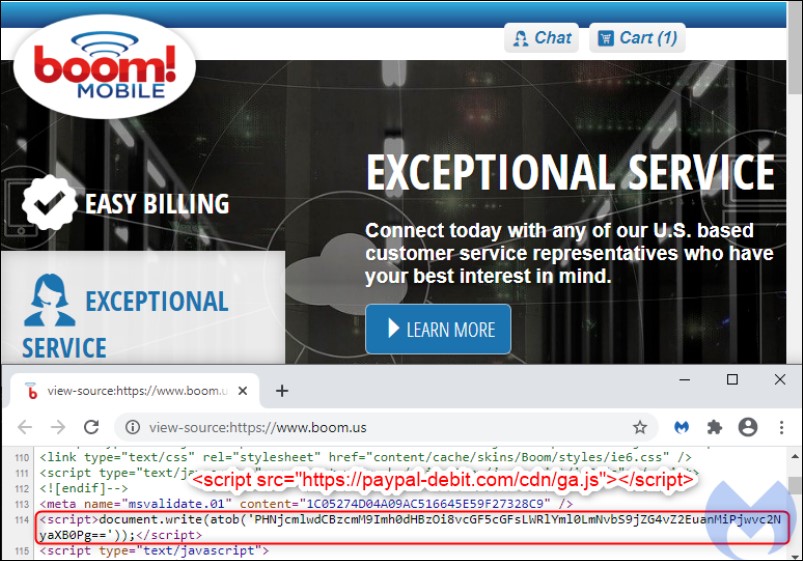
The mobile network operator’s website was still compromised when this article was published, with the Fullz House group’s malicious credit card skimmer still active on the Boom’s shopping cart-based e-commerce platform.
As Malwarebytes’ Threat Intelligence Team found, the attackers injected a single line of code that loads an external JavaScript library from paypal-debit[.]com/cdn/ga.js, camouflaged as a Google Analytics script.
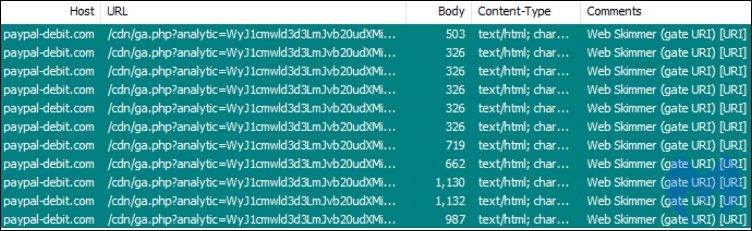
The card skimmer works by collecting payment card information from input fields every time it detects any changes, immediately exfiltrating the harvested data as a Base64 encoded GET request.
While the exact method used by the Fullz House Magecart group to infiltrate Boom’s website is not known, Malwarebytes observed that the company site runs PHP version 5.6.40, a version unsupported since January 2019.
“We reported this incident both via live chat and email to Boom! Mobile but have not heard back from them at the time of writing,” Malwarebytes explained. “Their website is still compromised and online shoppers are still at risk.”
The phishing and skimming combo
Fullz House is known for using a hybrid skimming/phishing tactic as discovered by researchers at digital threat management company RiskIQ.
The group is involved in both skimming and phishing for banking and card info from both payment provider customers and during checkouts on e-commerce platforms.
They put in the effort to develop their own web skimmers instead of relying on pre-made skimmers created by others that they camouflage as a Google Analytics script and gets loaded via a script tag within the compromised online shops (as is the case of the skimmer injected within the Boom! Mobile site.)
However, unlike modern skimmers who only harvest the data when the customers finalize the order, Fullz House’s skimmer scripts are extremely noisy and work more like a keylogger that continually check input fields for changes.
This skimmer was also repurposed by the group to work as a phishing tool that, once the victims hit the Buy button, redirects them from the compromised store to ‘man-in-the-middle’ fake payment pages designed to mimic payment interfaces from legitimate financial institutions.
On this page, they are asked to enter the payment details which get sent to the attackers’ servers once the Pay button is clicked.
Once that happens, the victims are immediately redirected to the store’s real payment processor page to complete the purchase not knowing that their credit card info was stolen.
To read the original article:



