Muhstik botnet, also known as Mushtik, has been targeting cloud infrastructure and IoTs for years.
The botnet mainly funds itself by mining cryptocurrency using open source tools like XMRig and cgminer.
New details have emerged related to this malware that shed light on its nefarious activities and origins.
What is Muhstik?
Muhstik is a botnet that leverages known web application exploits to compromise IoT devices, such as routers, to mine cryptocurrency.
It leverages IRC servers for its command-and-control (C2) activities.
Although Muhstik botnet has been around for at least 2018, in December 2019, Palo Alto Networks had identified a new variant of the botnet attacking and taking over Tomato routers.
Some of the vulnerabilities exploited by Muhstik include Oracle WebLogic Server bugs (CVE-2019-2725 and CVE-2017-10271) and Drupal RCE flaw (CVE-2018-7600).
Now, cloud security firm Lacework has provided some additional analysis and observations related to Muhstik.
A Muhstik attack executes in multiple stages.
Firstly, a payload file with name “pty” followed by a number is downloaded from the attacker’s server. Example URLs provided by Lacework include:
hxxp://167.99.39.134/.x/pty3
“Upon successful installation Mushtik will contact the IRC channel to receive commands,” says Chris Hall, cloud security researcher at Lacework.
The IRC servers are the C2 infrastructure powering the Muhstik botnet.
“Usually Muhstik will be instructed to download an XMRrig miner and a scanning module. The scanning module is used for growing the botnet through targeting other Linux servers and home routers,” Hall continued.
Muhstik uses Mirai source code to encrypt the configurations of its payload and scanning module through single-byte XOR encryption.
Lacework explains file samples containing Muhstik configuration data tend to contain the following byte sequence: 4F 57 4A 51 56 4B 49 0F.
This is the XOR’d (by 0x22) equivalent value of the “muhstik” keyword which can be identified in unpacked binaries.
Weird attribution and ‘anime’ references
However, more interesting details emerge when Lacework researchers attempt to trace the botnet’s origins.
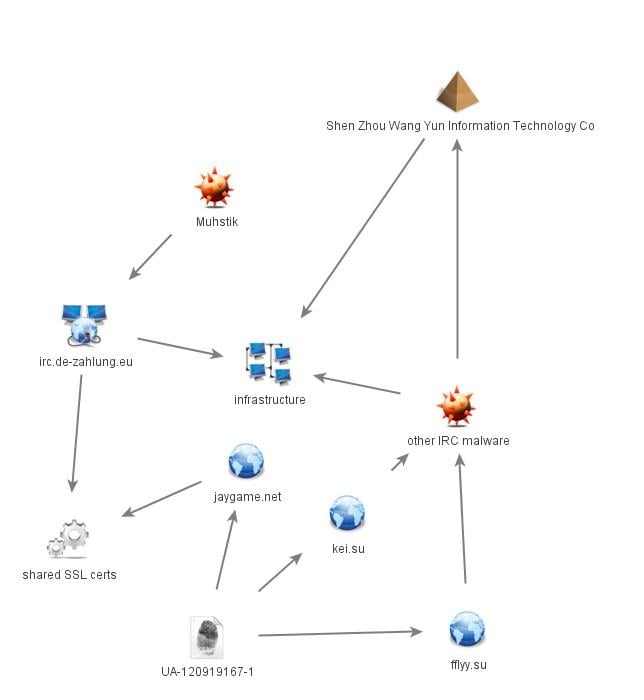
“IRC C2 irc.de-zahlung.eu was found to be sharing an SSL cert with site jaygame.net,” explains Hall.
“Jaygame.net is an amateur site about a game involving an Anime character named ‘Jay’. The site is currently leveraging Google Analytics ID UA-120919167-1.”
This analytics ID has been found to be associated with other two domains: fflyy.su and kei.su.
In tests by BleepingComputer, we observed the stated Analytics ID to indeed be present on jaygame.net but no longer on the other two domains.
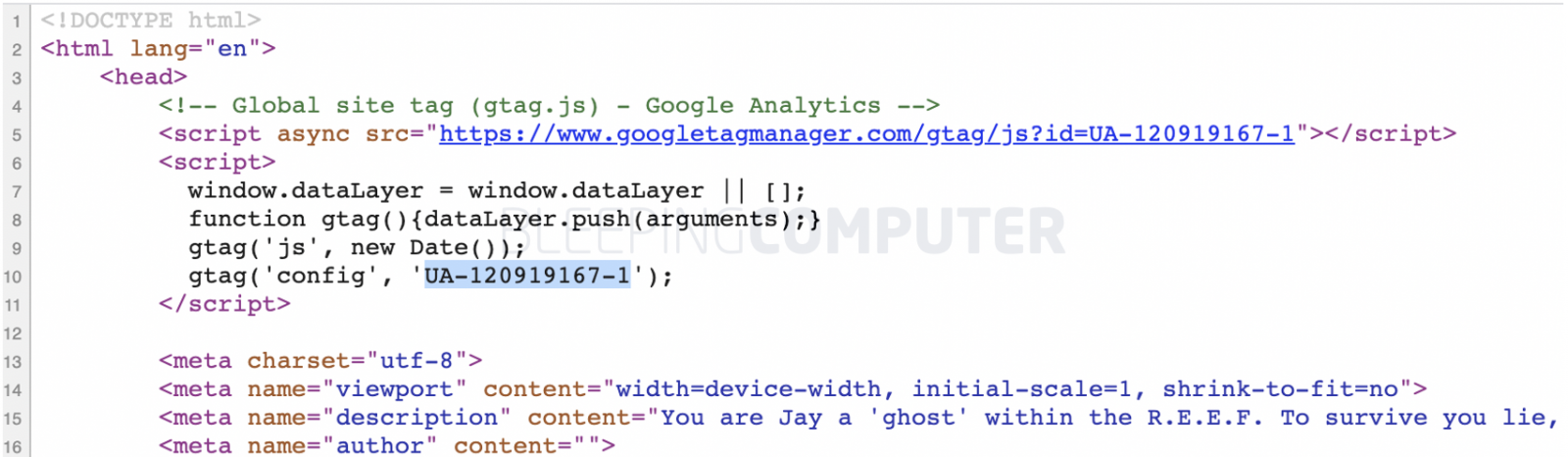
Source: BleepingComputer
However, it is worth noting anyone, including a malicious actor, can include a Google Analytics ID of a legitimate website into their own website.
Another domain with references to anime used by Muhstik is pokemoninc.com. Whereas, Kei (in kei.su) could be a reference to an anime character too, according to Lacework.
By tracking similar correlations, Lacework traced the origin of Muhstik to a Chinese forensics firm.
“These all have links to the same malware upload path belonging to Chinese forensics firm Shen Zhou Wang Yun Information Technology Co., Ltd,” explains their blog post.
Additionally, Lacework mentions the original malware samples were uploaded to VirusTotal all at once before Muhstik attacks were observed in the wild.
These samples had multiple strings mentioning “shenzhouwangyun,” such as in /home/wys/shenzhouwangyun/shell/downloadFile/tomato.deutschland-zahlung.eu_nvr
This indicates, “Shen Zhou Wang Yun is likely the malware originator and not simply the first uploader,” suggested Hall.
In the past, researchers have also linked Shen Zhou Wang Yun to the HiddenWasp Linux malware.
Muhstik’s up to date Indicators of Compromise (IOCs) have been provided in a CSV by Lacework.
To read the original article:



