Although the global financial industry has made strides in protecting its data from malware, including Trojans, cyberthreats such as network intrusion, ransomware and criminal gang cooperation are presenting fresh challenges, according to a report issued this week by the Carnegie Endowment for International Peace.
In a paper titled, “Enduring Cyber Threats and Emerging Challenges to the Financial Sector,” researchers at the think tank note that while financial institutions are pushing various digital transformation projects to make their organizations more agile, the pace of change has created more opportunities for attacks against networks and infrastructure.
And while financial institutions have improved security in recent years, including doing a better job of defending against malware threats and improving the security around systems such as SWIFT – the global money-transfer network – the challenges that come from ransomware and other attacks is making an impact.
“One of the most significant threats today is from network intrusions that lead to ransom and extortion,” according to the report, which included input from the World Economic Forum. “Over a dozen threat groups are using the same business model and finding it very effective. The estimated loss to victims caused by these groups in 2020 has reached hundreds of millions of dollars, with the REvil group, aka Sodinokibi, claiming over $100 million in profits in one year, the report states. “And the rate of attack is still accelerating.”
Adrian Nish, Saher Naumaan and James Muir, the report’s authors, note that the threats from network intrusion and ransomware that lead to data theft and extortion are likely to continue into 2021, so private industry and governments worldwide must develop better responses.
The authors also call for banks and governments to collaborate on developing a collective defense against such attacks.
“A response may include sanctions, arrests, asset seizures, or other actions,” the researchers note. “For such actions to be justified, there must be a mutual understanding that a line has been crossed; in addition, since sanctions and other actions to hold actors accountable may provoke an escalatory response, financial actors will need to have a minimum level of resilience so that they can withstand such responses.”
Network Intrusion
One of the biggest threats facing financial institutions is the use of network intrusion techniques by cybercriminal gangs to gain a foothold within networks and then use move laterally around the infrastructure looking for files and data, as well as other weaknesses, according to the report.
In many cases, attackers are using legitimate penetration testing tools, such as Cobalt Strike and PowerShell Empire, to gain initial access. At the same time, living-off-the-land techniques that leverage Windows tools, such as PowerShell, help maintain persistence and assist with reconnaissance.
Other techniques attackers are increasingly using to target bank networks include the use of fileless malware that avoids security tools and leaves little forensic trace as well as domain name system command-and-control modules, which can effectively evade web-proxy controls and intrusion detection tools, according to the report.
Ransomware and Extortion
Perhaps the greatest cyberthreats facing financial institutions are ransomware gangs that threaten to release exfiltrated data if the victim does not pay, the report notes. Over the past several months, these cybercriminal gangs have become even more brazen with their tactics.
“Banks in Chile and Seychelles, as well as financial technology companies like Silverlake Axis, a supplier of core banking systems throughout the Asia-Pacific, are all reportedly victims of separate ransom and extortion attempts,” the report notes.
The report notes that the New Year’s Even attack against Travelex, a London-based foreign currency exchange, is a prime example of how these tactics can produce a significant payday for gangs.
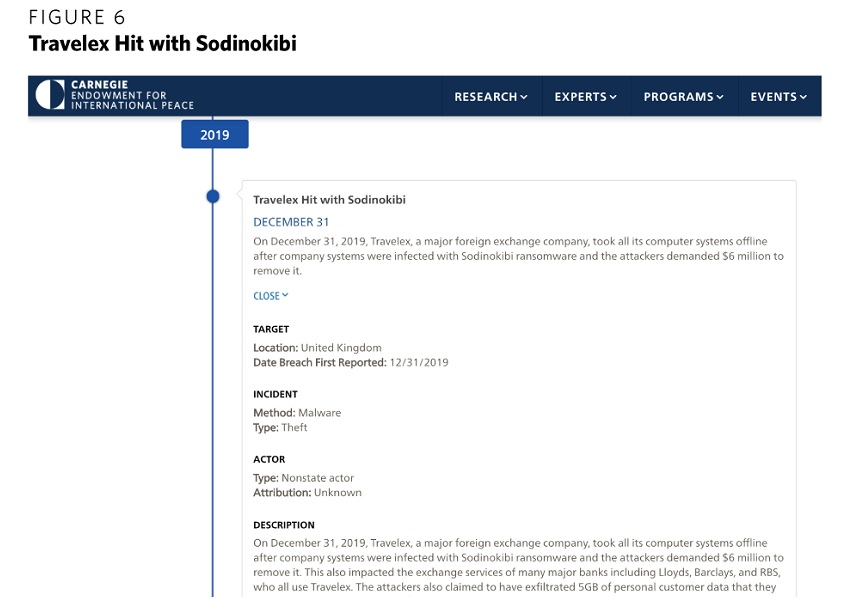 Source: Carnegie Endowment for International Peace
Source: Carnegie Endowment for International Peace
Other criminal gangs have put a fresh twist on older tactics, such as distributed denial-of-service attacks, often demanding payments to stop an attack. DDoS attacks have been on the rise over the past few months, with criminal groups targeting the New Zealand Stock Exchange over several.
Criminal Overlap
The researchers also note that threat actors and criminal gangs have created an active underground ecosystem that is strengthened by collaboration.
In 2018, for example, several attacks linked to North Korea-based Lazarus Group happened on networks within the same timeframe as a Russian-speaking criminal group known as TA505, which was also probing these networks. Forensic evidence from the incident response confirmed that the Russian criminal actors effectively handed over access to Lazarus, according to the report.
TA505, which is also referred to as Hive0065 by IBM X-Force, is a financially motivated cybercrime group that has been active since at least 2014.
“TA505, has been busy providing access to other groups. For example, Silence, a Russian-speaking criminal group, also appears to have a relationship with TA505,” the report notes. “During a 2019 BAE Systems investigation of a Silence intrusion against a European bank, Silence malware was deployed off the back of an initial TA505 intrusion. This suggests the group also has links to other parties within the criminal underground.”
Tom Kellermann, head of cybersecurity strategy at VMware Carbon Black, who also sits on the Cyber Investigations Advisory Board for the U.S. Secret Service, tells Information Security Media Group that his team’s researchers have determined this level of criminal overlap continues to grow.
“Cybercriminals have formed cybercrime cartels, and they maintain their untouchable status from law enforcement because they are seen as national assets by rogue regimes as ways to offset economic sanctions,” Kellermann says. “They have capitalized on the intersection of cybercrime and fraud in their operation of modern criminal enterprises.”
To read the original article:
lhttps://www.bankinfosecurity.com/global-financial-industry-facing-fresh-round-cyberthreats-a-15409



