Russian-speaking hackers behind Zebrocy malware have changed their technique for delivering malware to high-profile victims and started to pack the threats in Virtual Hard Drives (VHD) to avoid detection.
The technique was spotted in recent spear-phishing campaigns from threat group APT28 (Fancy Bear, Sofacy, Strontium, Sednit) to infect target systems with a variant of the Zebrocy toolset.
New Zebrocy variants enjoy low detection
Zebrocy comes in many programming languages (AutoIT, C++, C#, Delphi, Go, VB.NET). For the recent campaigns, the threat actor chose the Golang-based version instead of the more common Delphi one.
Windows 10 supports VHD files natively and can mount them as external drives to allow users to view the files within. Last year, security researchers discovered that antivirus engines do not check VHD contents until the disk images are mounted.
Researchers at Intezer discovered at the end of November a VHD uploaded to the Virus Total scanning platform from Azerbaijan. Inside the image were a PDF file and an executable posing as a Microsoft Word document, which Zebrocy malware.
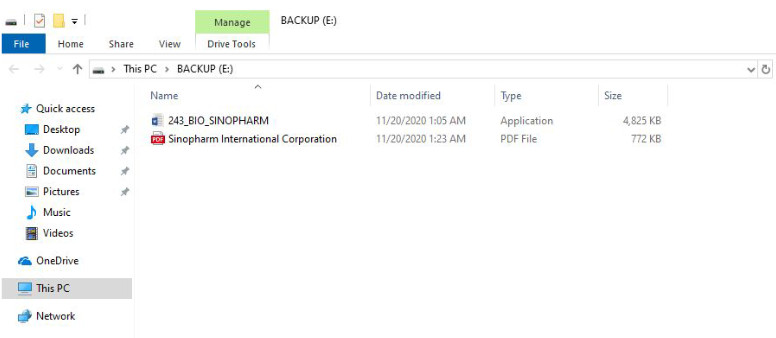
The PDF is a presentation about the Sinopharm International Corporation, a Chinese pharmaceutical company that is currently in phase three trials for a COVID-19 vaccine.
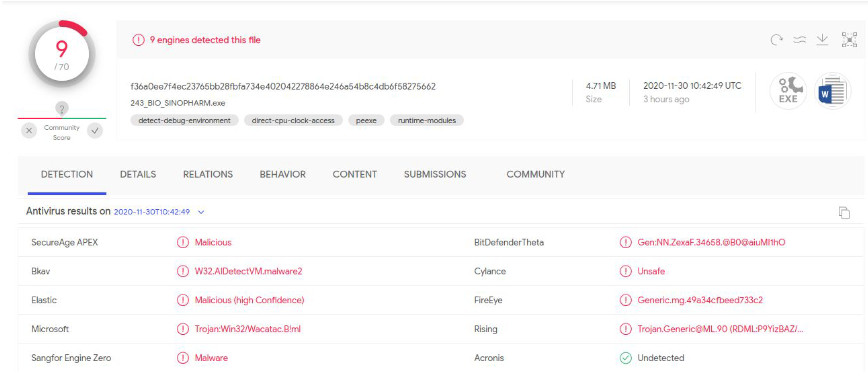
The Zebrocy variant in the VHD file is a new one that enjoyed low detection on Virus Total. On November 30, only nine engines out of 70 detected the malware.
However, Intezer’s analysis showed that the new Zebrocy is genetically similar to a Delphi variant used a year ago in a campaign against targets in Azerbaijan.
VHD files used in other campaigns
Based on clues in the malicious VHD, the researchers discovered that the threat actor had conducted similar campaigns since at least October.
Other disc images used as phishing lures had been uploaded to Virus Total, one of them on November 12 from Kazakhstan and another with a creation timestamp of October 21.
Both of the last two VHD images included a Zebrocy sample impersonating a Microsoft Word document and a PDF file, and they share the same disk ID.
The oldest one, though, delivered a Delphi-based variant of the malware and used a PDF bait written in Russian.
Zebrocy has been used for years and is a set of downloaders, droppers, and backdoors. The Golang-based variant was discovered last year and has been used on and off by the hackers.
The use of VHD disk images appears to be a new page in the malware delivery book of the threat group behind Zebrocy. The technique was seen before in phishing operations from the Cobalt group to distribute the CobInt loader in late December 2019.
In its report published today, Intezer provides indicators of compromise for the command and control server, the VHD files, and the Zebrocy malware samples used in the recent phishing campaigns.
To read the original article:



