Google on Monday disclosed details about an ongoing campaign carried out by a government-backed threat actor from North Korea that has targeted security researchers working on vulnerability research and development.
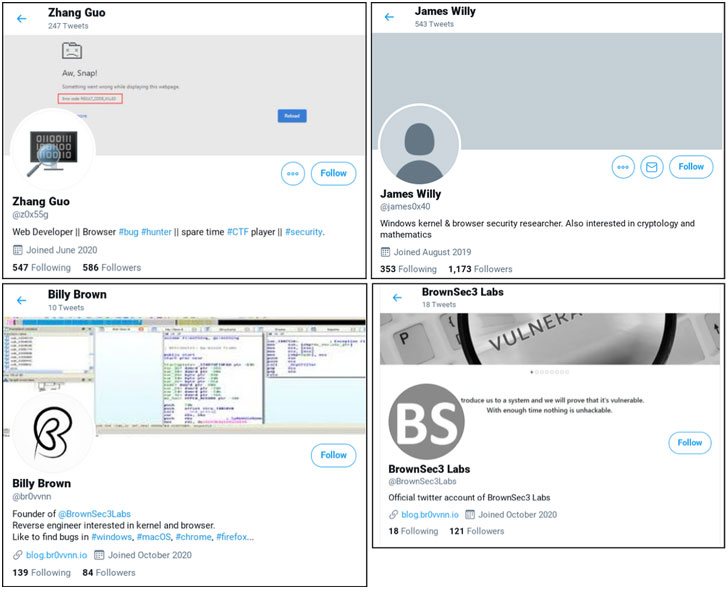
The internet giant’s Threat Analysis Group (TAG) said the adversary created a research blog and multiple profiles on various social media platforms such as Twitter, Twitter, LinkedIn, Telegram, Discord, and Keybase in a bid to communicate with the researchers and build trust.
The goal, it appears, is to steal exploits developed by the researchers for possibly undisclosed vulnerabilities, thereby allowing them to stage further attacks on vulnerable targets of their choice.
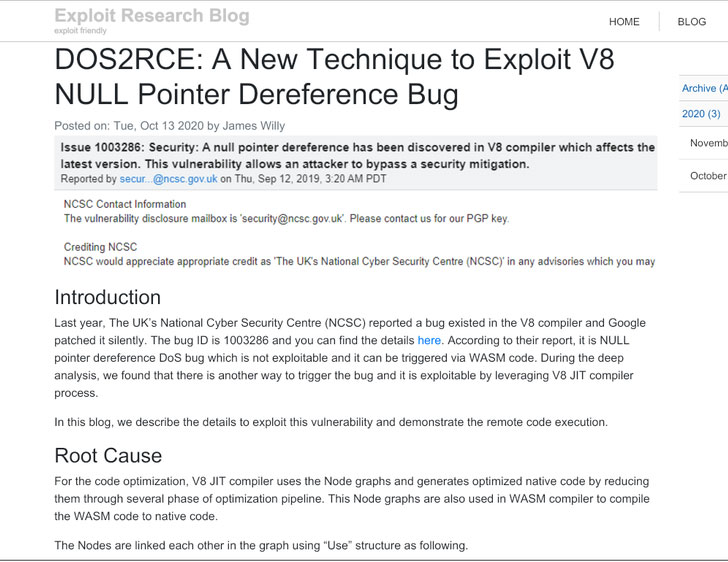
“Their blog contains write-ups and analysis of vulnerabilities that have been publicly disclosed, including ‘guest’ posts from unwitting legitimate security researchers, likely in an attempt to build additional credibility with other security researchers,” said TAG researcher Adam Weidemann.
In one instance, the actor used Twitter to share a YouTube video of what it claimed to be an exploit for a recently patched Windows Defender flaw (CVE-2021-1647), when in reality, the exploit turned out to be fake.
The North Korean hackers are also said to have used a “novel social engineering method” to hit security researchers by asking them if they would like to collaborate on vulnerability research together and then provide the targeted individual with a Visual Studio Project.
This Visual Studio Project, besides containing the source code for exploiting the vulnerability, included a custom malware that establishes communication with a remote command-and-control (C2) server to execute arbitrary commands on the compromised system.
What’s more, TAG said it observed several cases where researchers were infected after visiting the research blog, following which a malicious service was installed on the machine, and an in-memory backdoor would begin beaconing to a C2 server.
With the victim systems running fully patched and up-to-date versions of Windows 10 and Chrome web browser, the exact mechanism of compromise remains unknown. But it’s suspected that the threat actor likely leveraged zero-day vulnerabilities in Windows 10 and Chrome to deploy the malware.
“If you are concerned that you are being targeted, we recommend that you compartmentalize your research activities using separate physical or virtual machines for general web browsing, interacting with others in the research community, accepting files from third parties and your own security research,” Weidemann said.
To read the original article:
https://thehackernews.com/2021/01/n-korean-hackers-targeting-security.html?fbclid=IwAR3rES_6wOeZlziQg8jZqFViB7UPXPybgZVU0NHcr6ChCmWgZnPr916ySsI