A new targeted phishing campaign includes the novel obfuscation technique of using Morse code to hide malicious URLs in an email attachment.
Samuel Morse and Alfred Vail invented morse code as a way of transmitting messages across telegraph wire. When using Morse code, each letter and number is encoded as a series of dots (short sound) and dashes (long sound).
Starting last week, a threat actor began utilizing Morse code to hide malicious URLs in their phishing form to bypass secure mail gateways and mail filters.
BleepingComputer could not find any references to Morse code being used in phishing attacks in the past, making this a novel obfuscation technique
The novel Morse code phishing attack
After first learning of this attack from a post on Reddit, BleepingComputer was able to find numerous samples of the targeted attack uploaded to VirusTotal since February 2nd, 2021.
The phishing attack starts with an email pretending to be an invoice for the company with a mail subject like ‘Revenue_payment_invoice February_Wednesday 02/03/2021.’
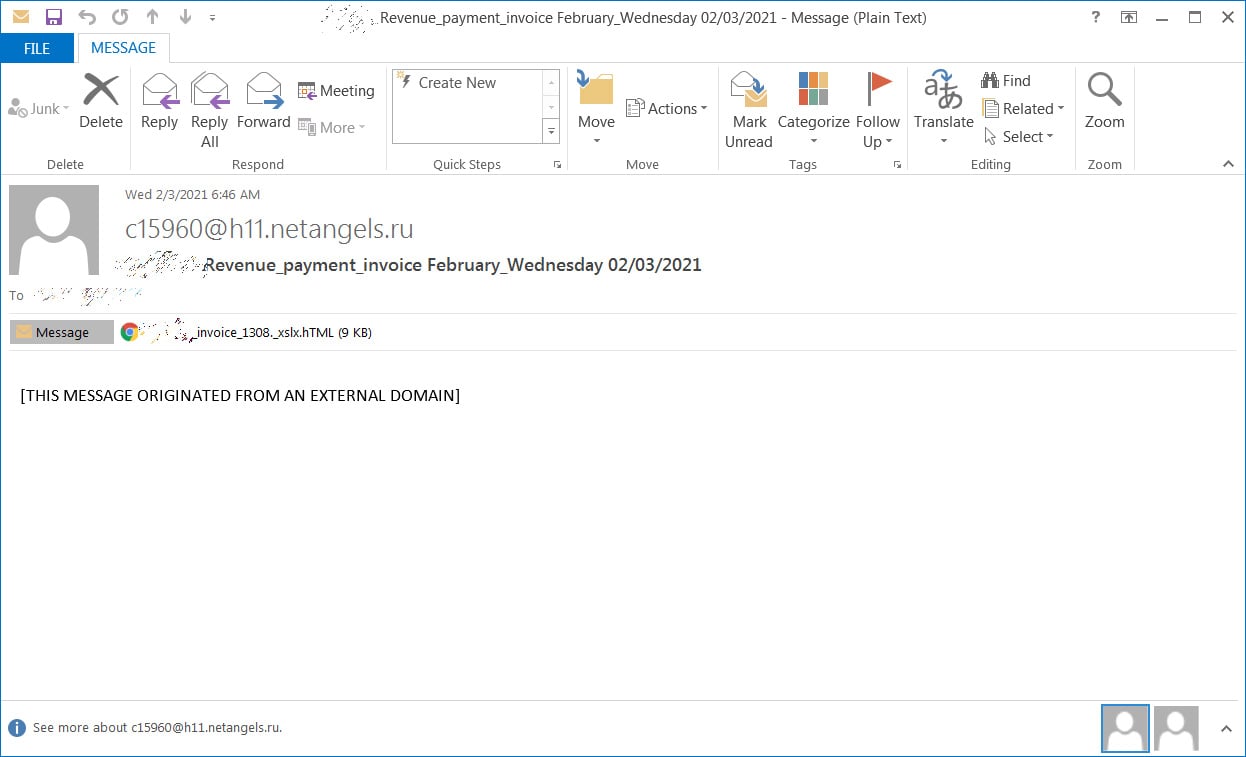
This email includes an HTML attachment named in such a way as to appear to be an Excel invoice for the company. These attachments are named in the format ‘[company_name]_invoice_[number]._xlsx.hTML.’
For example, if BleepingComputer was targeted, the attachment would be named ‘bleepingcomputer_invoice_1308._xlsx.hTML.’
When viewing the attachment in a text editor, you can see that they include JavaScript that maps letters and numbers to Morse code. For example, the letter ‘a‘ is mapped to ‘.-‘ and the letter ‘b‘ is mapped to ‘-…‘, as shown below.
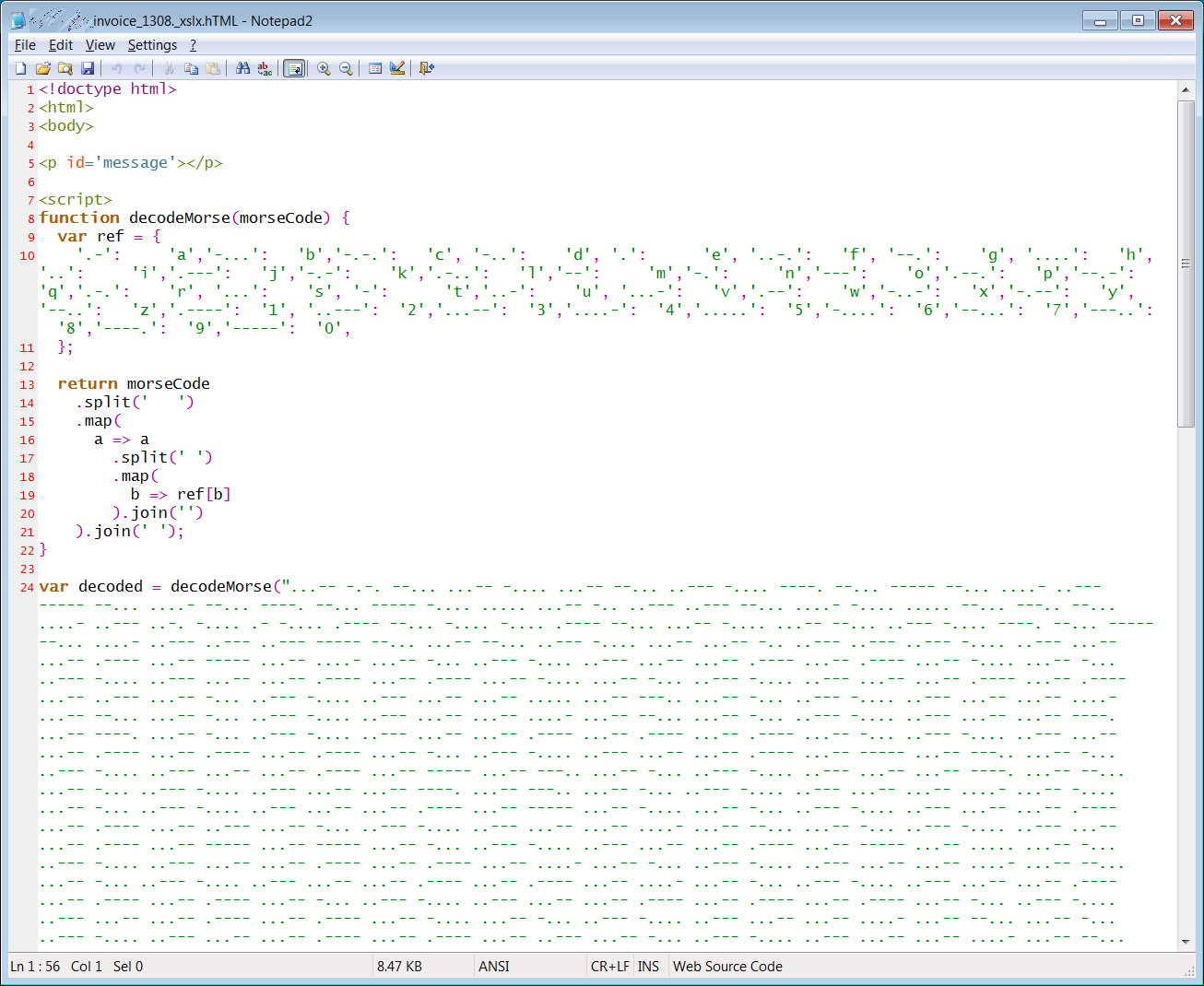
The script then calls a decodeMorse() function to decode a Morse code string into a hexadecimal string. This hexadecimal string is further decoded into JavaScript tags that are injected into the HTML page.
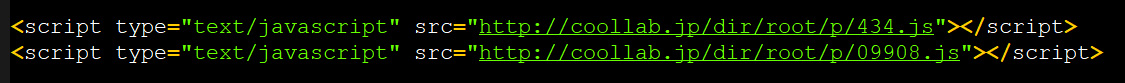
These injected scripts combined with the HTML attachment contain the various resources necessary to render a fake Excel spreadsheet that states their sign-in timed out and prompts them to enter their password again.
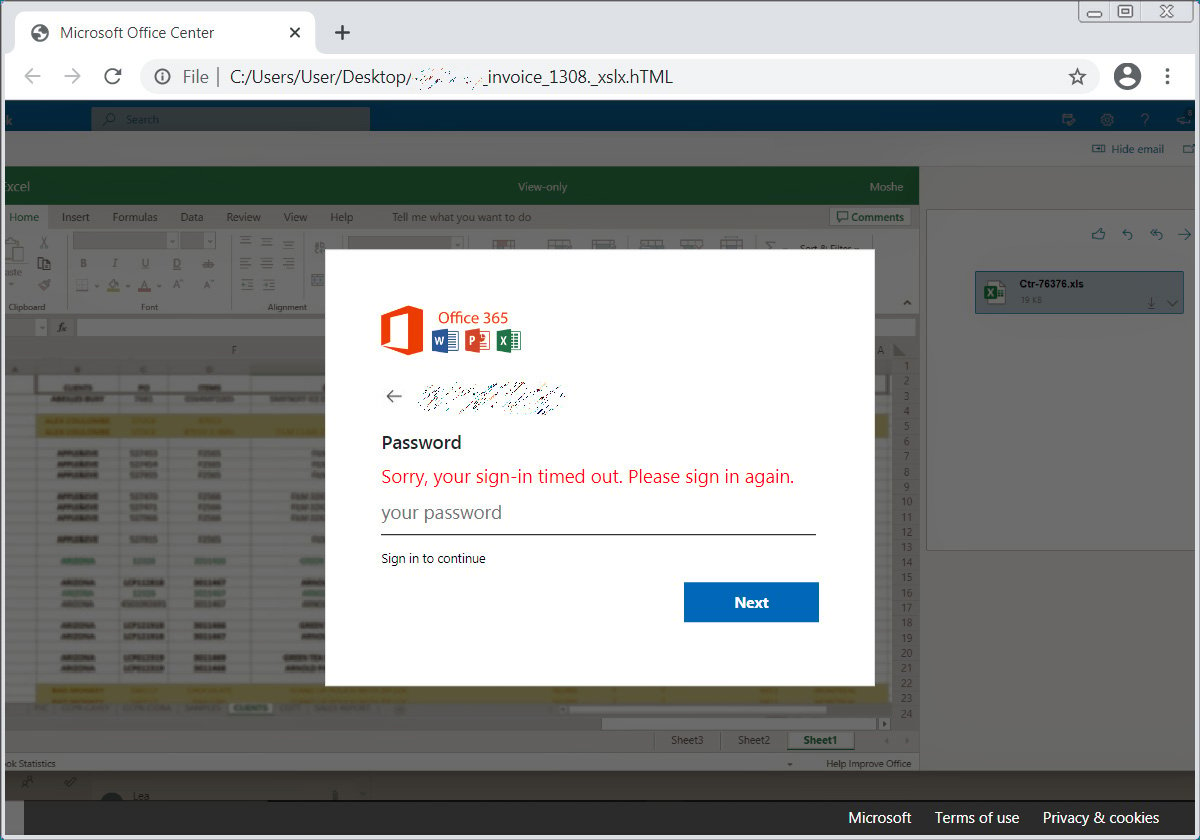
Once a user enters their password, the form will submit the password to a remote site where the attackers can collect the login credentials.
This campaign is highly targeted, with the threat actor using the logo.clearbit.comservice to insert logos for the recipient’s companies into the login form to make it more convincing. If a logo is not available, it uses the generic Office 365 logo, as shown in the image above.
BleepingComputer has seen eleven companies targeted by this phishing attack, including SGS, Dimensional, Metrohm, SBI (Mauritius) Ltd, NUOVO IMAIE, Bridgestone, Cargeas, ODDO BHF Asset Management, Dea Capital, Equinti, and Capital Four.
Phishing scams are becoming more intricate every day as mail gateways become better at detecting malicious emails.
Due to this, everyone must pay close attention to URLs and attachment names before submitting any information. If something looks at all suspicious, recipients should contact their network administrators to investigate further.
As this phishing email uses attachments with double-extension (xlxs and HTML), it is important to make sure that Windows file extensions are enabled to make it easier to spot suspicious attachments.
To read the original article:



