A phishing campaign targeting users of Outlook Web Access and Office 365 services collected thousands of credentials relying on trusted domains such as SendGrid.
The threat actor behind this activity, which received the name “Compact,” has been operating since at least the beginning of 2020 and likely collected more than 400,000 credentials in multiple campaigns.
Zooming in on credentials
Using Zoom invites as a lure and an extensive list of email addresses, the operators of the phishing campaign delivered messages from hacked accounts on the SendGrid cloud-based email delivery platform.
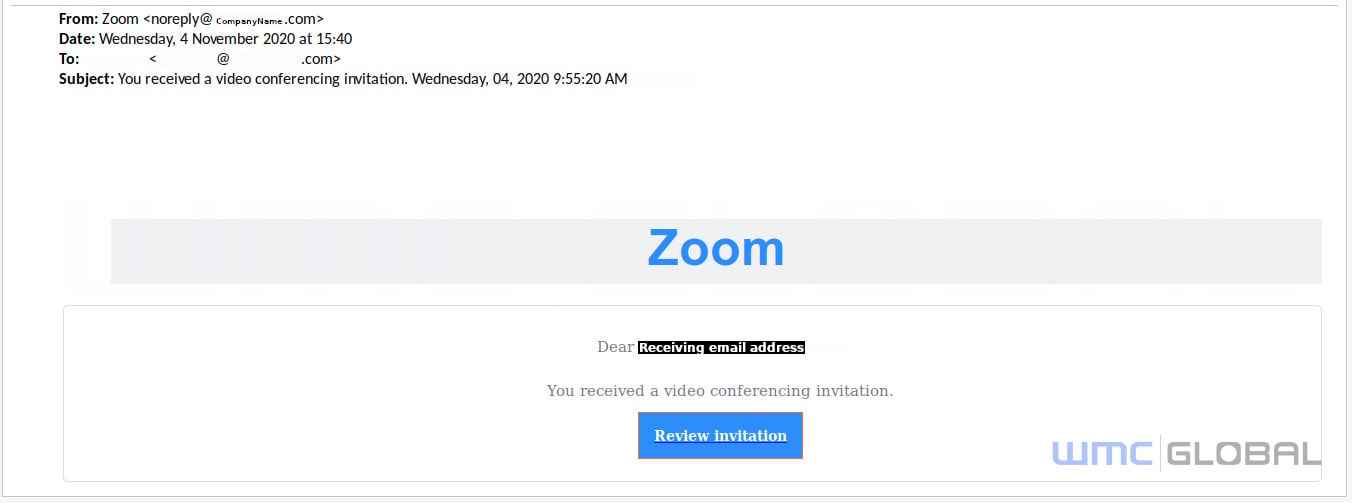
Because SendGrid is a trusted SMTP provider, the messages had a greater chance to reach their destination and not be blocked by email protection technology.
Researchers at WMC Global, makers of the PhishFeed real-time phishing intelligence service, capitalized on some mistakes of the threat actor that allowed them to analyze how the credentials moved from the phishing site into the hands of the operator.
Thousands of credentials collected
They estimate that each phishing wave collected 3,700 unique credentials, which would make the total from multiple Compact campaigns upwards of 400,000.
Earlier operations used compromised SendGrid accounts to deliver the phishing emails and then moved to MailGun, a developer-centric email service with APIs that allows sending, receiving, and tracking messages.
WMC Global believes that the switch to a different service was determined by their collaboration with SendGrid to restore compromised accounts to the legitimate owners.
According to the researchers, the phishing website of the Compact campaign had distinct fingerprints in the code that permitted monitoring and detecting of a new site as soon as it became live.
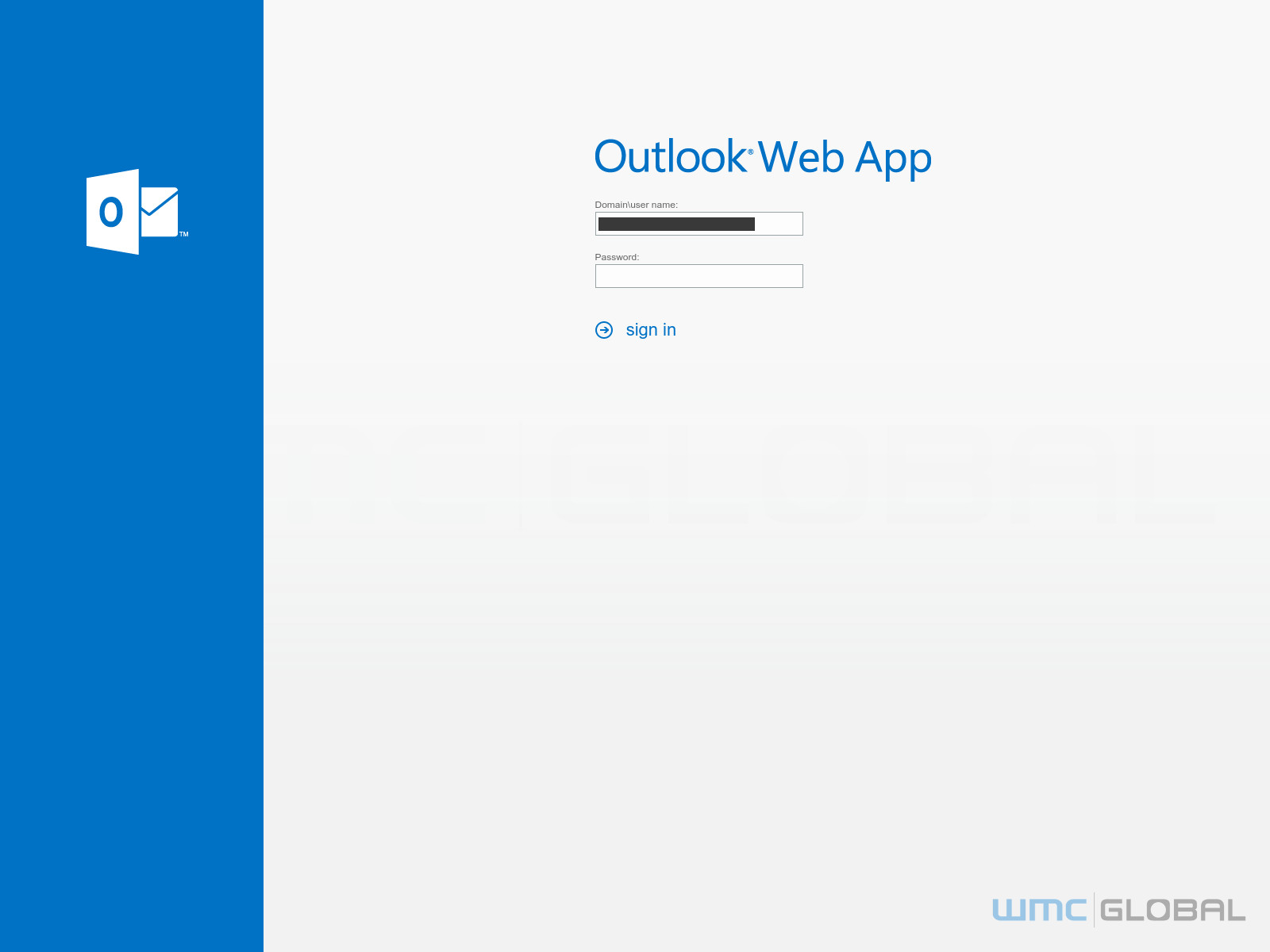
They found a landing site impersonating Outlook Web App in December 2020 and another one in January 2021 that pretended to be for Office 365 login.
Looking at the website source code, the researchers were able to pull exfiltration locations and credential logs in text files. The hackers behind the Compact campaigns hosted the exfiltration code on numerous compromised legitimate websites.
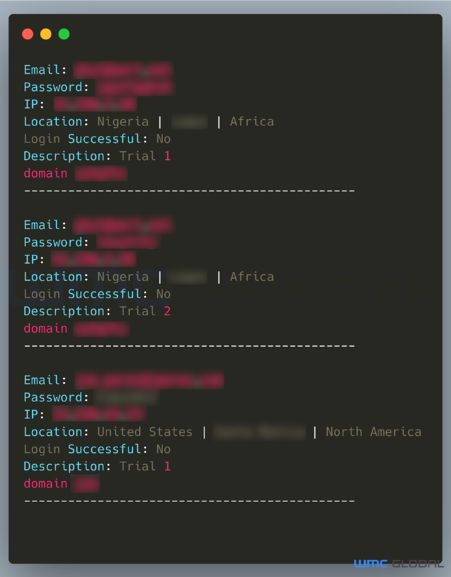
Analyzing the logs, the researchers found that employees at “large and notable” companies had fallen for the Compact phishing campaign.
They also noticed in mid-January that a credential poisoning operation was underway, diluting the set of legitimate credentials collected by the threat actor.
“Some cybersecurity companies use credential poisoning to hide legitimate credentials in pools of fake logins, causing the threat actor difficulty detecting the authentic logins. Some threat actors may also poison the results of their competitors” – WMC Global
Opsec blunders
While the operators of the Compact campaigns appear to be technically knowledgeable, they blundered by leaving a misconfigured exfiltration script and exposing a web shell that allowed the researchers to download multiple copies of the exfiltration code.
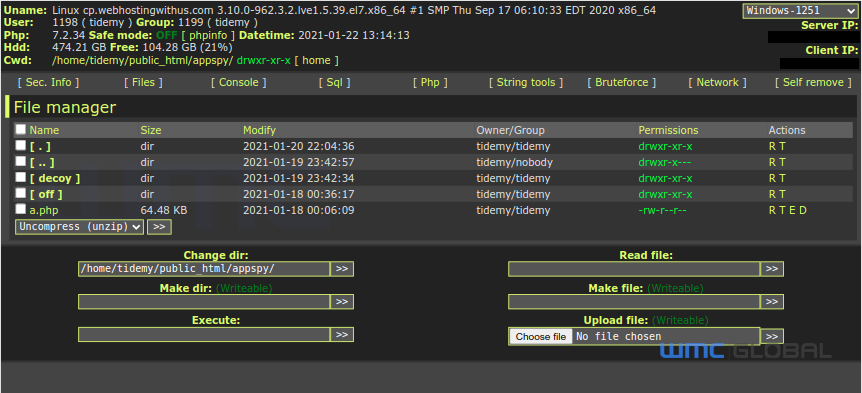
These opsec slipups enabled the researchers to understand how the actors handled the POST data and note that the code was more complex than expected for a phishing operator.
The investigation also revealed two email addresses connected to the operators. The researchers believe that these accounts were registered to receive the phishing logs.
WMC Global says that the latest email campaigns were noisy enough to attract attention but the tactics, techniques, and procedures observed point to other campaigns that used different phishing themes (Excel, OWA, Outlook Web Access Exchange, 1&1 Ionos, Rackspace).
Since September, the threat actor started using an Office 365 theme that continues to be active and is the most prevalent.
In their technical analysis today, the WMC Global Threat Intelligence Team also released a set of indicators of compromise that include locations for storing media files used in the campaigns, hashes, and a long list of phishing sites.
To read the original article:



