Google Chrome will block the browser’s access to TCP port 554 to protect against attacks using the NAT Slipstreaming 2.0 vulnerability.
Last year, security researchers disclosed a new version of the NAT Slipstreaming vulnerability that allows malicious scripts to bypass a website visitor’s NAT firewall and access any TCP/UDP port on the visitor’s internal network.
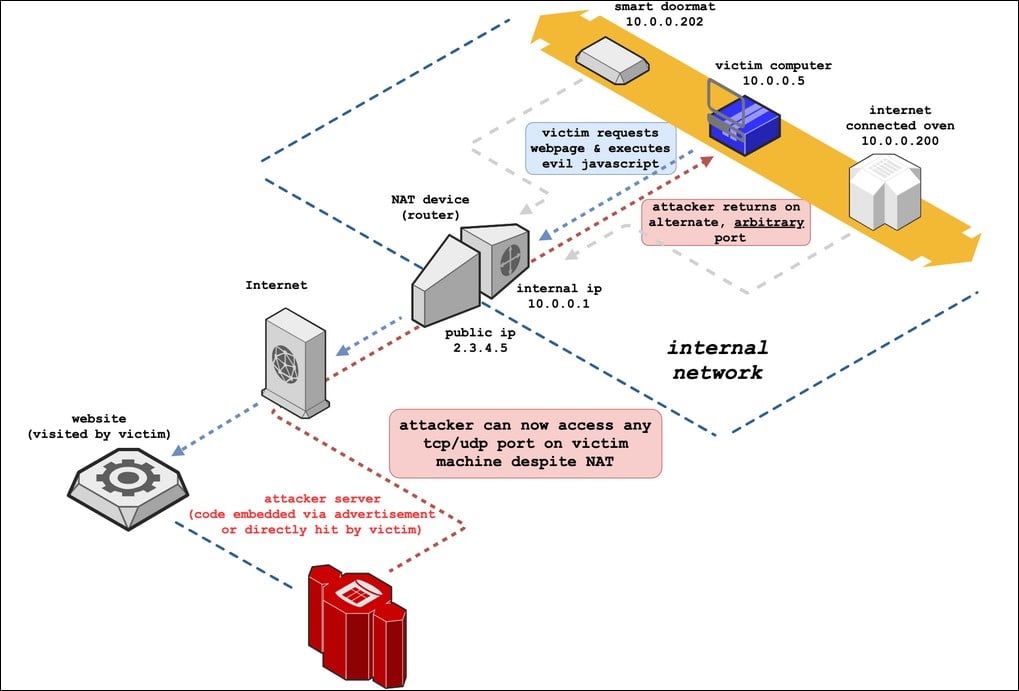
As this vulnerability only works on specific ports monitored by a router’s Application Level Gateway (ALG), browser developers, including Google, Safari, and Mozilla, have been blocking vulnerable ports that do not receive a lot of traffic.
When the vulnerability was first disclosed, Google Chrome 87 began blocking HTTP and HTTPS access to TCP ports 5060 and 5061 to protect against the vulnerability.
In January 2021, Google blocked HTTP, HTTPS, and FTP access to an additional seven ports: ports 69, 137, 161, 1719, 1720, 1723, and 6566.
In the past, Google also blocked port 554 but removed the block after complaints from enterprise users.
“Chrome briefly blocked port 554 before, but it was unblocked due to complaints from enterprise users. However, we have now achieved rough consensus at https://github.com/whatwg/fetch/pull/1148 to block 554,” Chromium engineer Adam Rice announced today.
Google and Safari developers are also discussing blocking access to port 10080, which Firefox already blocks, but are hesitant due to legitimate web browser requests to that port.
Once a port is blocked, when a user attempts to connect to it, users are shown an error message stating ‘ERR_UNSAFE_PORT.’
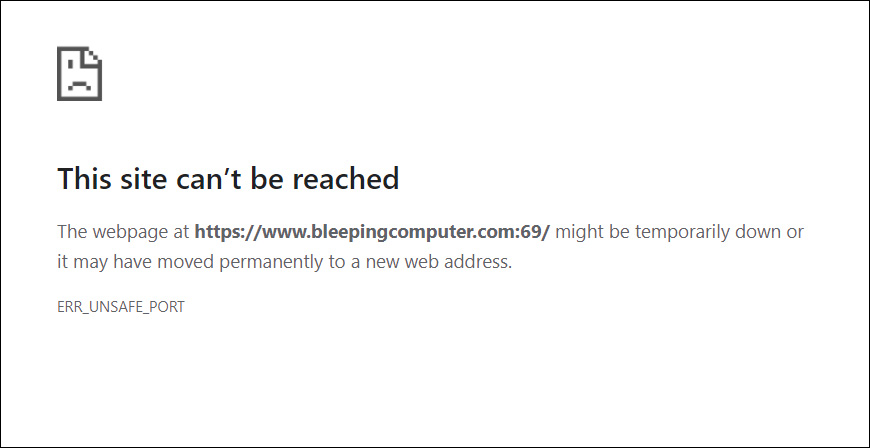
If you host a website on these ports, you should switch to a different port to allow visitors to continue accessing your application.
Firefox 84+ and Safari are already blocking port 554 in their browsers.
To read the original article:



