A massive ransomware campaign targeting QNAP devices worldwide is underway, and users are finding their files now stored in password-protected 7zip archives.
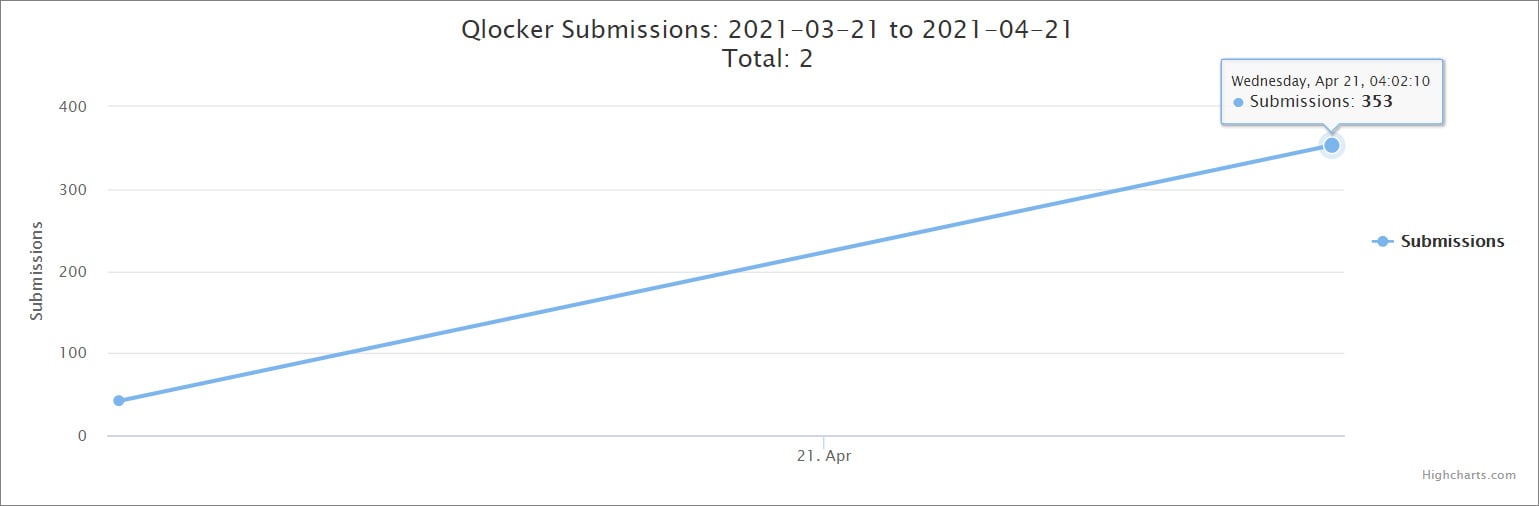
The ransomware is called Qlocker and began targeting QNAP devices on April 19th, 2021. Since then, there has been an enormous amount of activity in our support forum, and ID-Ransomware has seen a surge of submissions from victims.
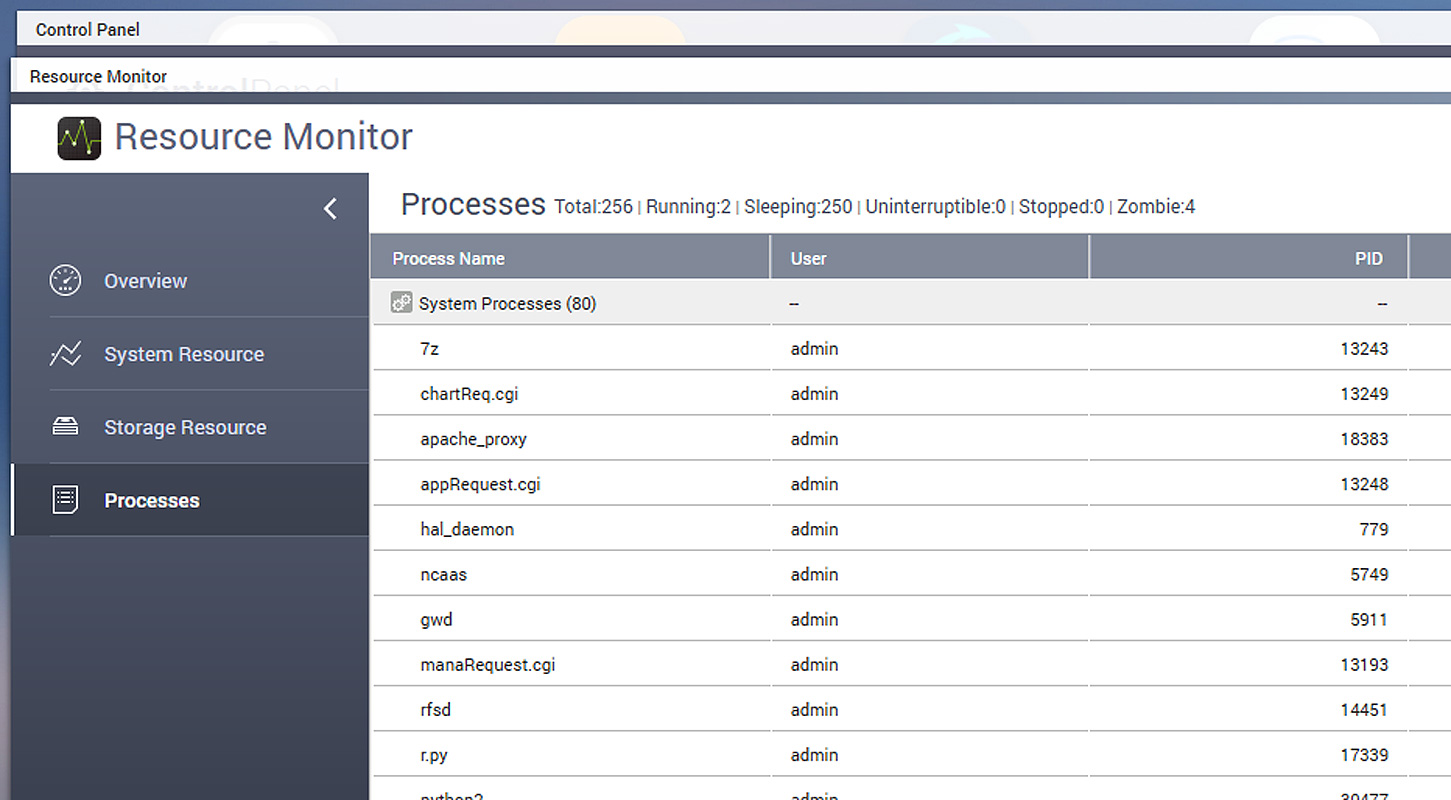
According to reports from victims in a BleepingComputer Qlocker support topic, the attackers use 7-zip to move files on QNAP devices into password-protected archives. While the files are being locked, the QNAP Resource Monitor will display numerous ‘7z’ processes which are the 7zip command-line executable.
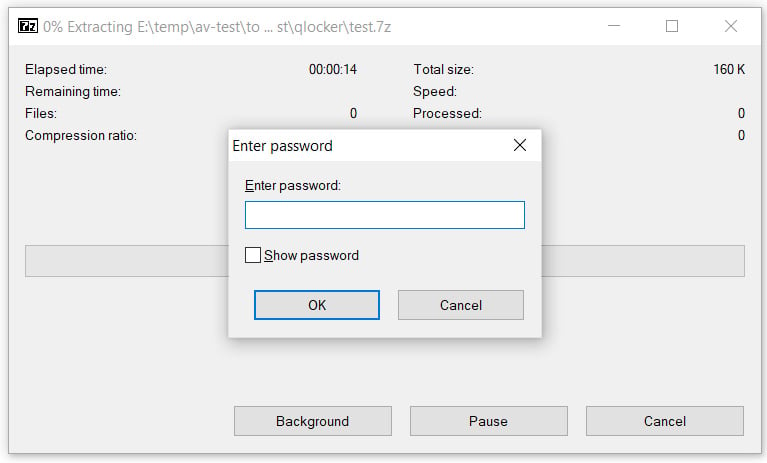
When the ransomware has finished, the QNAP device’s files will be stored in password-protected 7-zip archives ending with the .7z extension. To extract these archives, victims will need to enter a password known only to the attacker.
After QNAP devices are encrypted, users are left with a !!!READ_ME.txt ransom note that includes a unique client key that the victims need to enter to log into the ransomware’s Tor payment site.
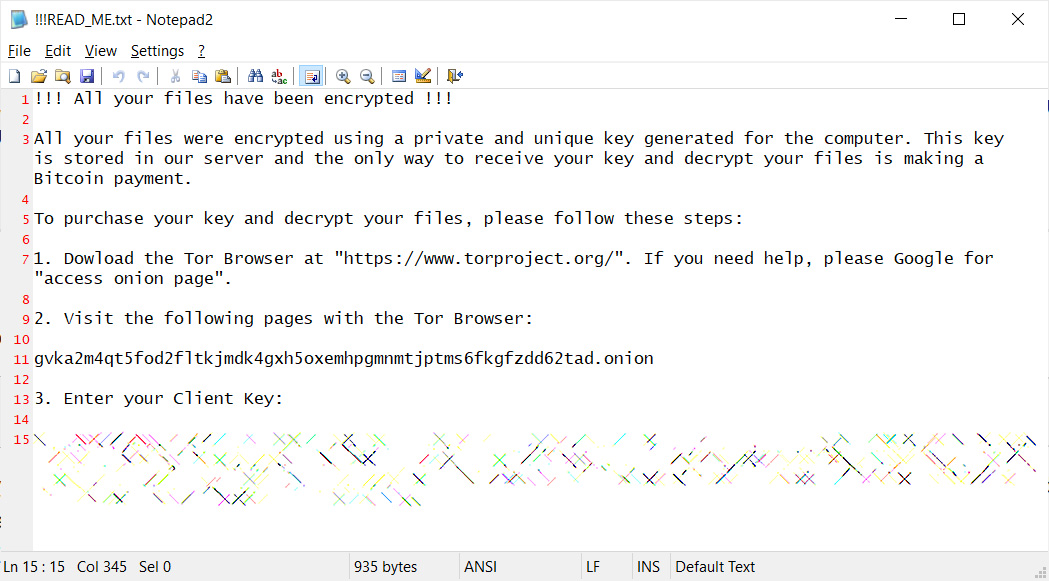
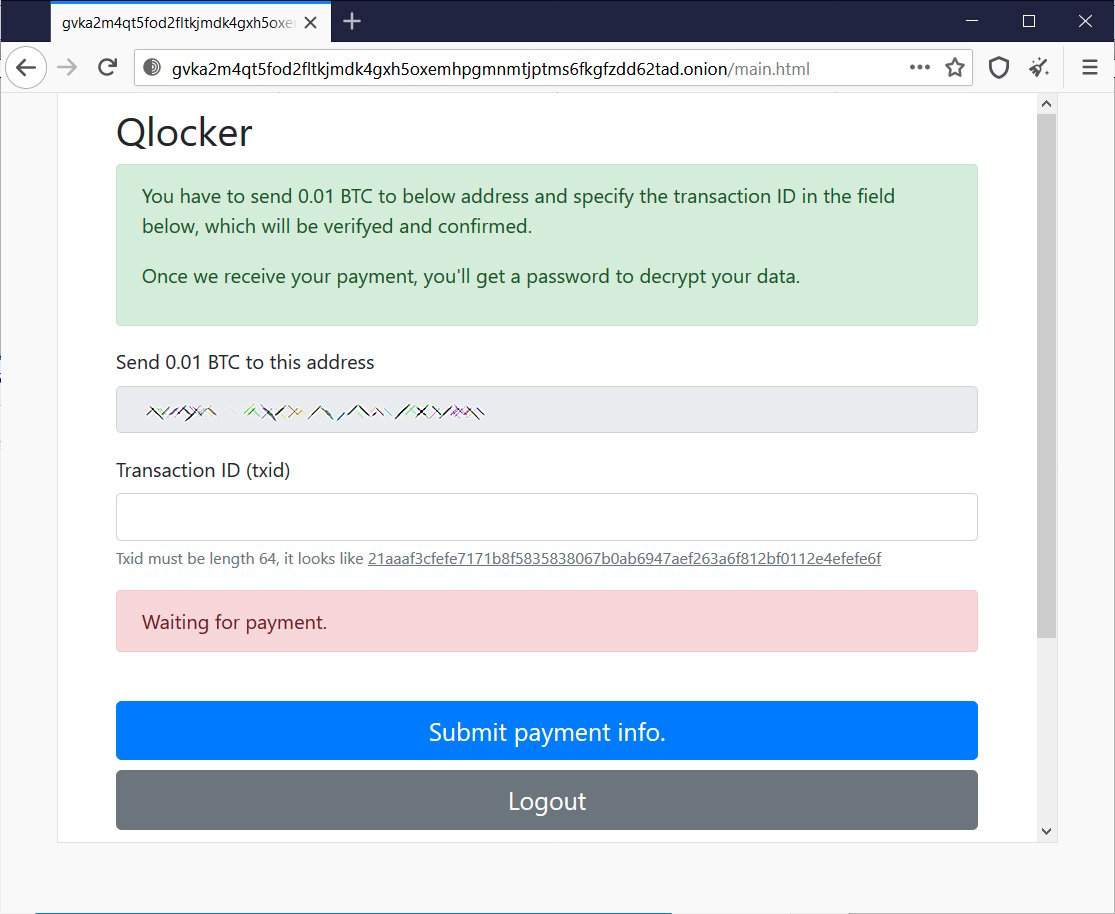
From the Qlocker ransom notes seen by BleepingComputer, all victims are told to pay 0.01 Bitcoins, which is approximately $557.74, to get a password for their archived files.
While the ‘7z’ process is active on a device, it may be possible to recover the password by connecting to the device using SSH or Telnet.
Once you log in to the console, you can run the ps -ef command to see the command line arguments for the 7z program, including the password used to archive your files. If you can access the command line for 7z, please contact us so we can help you extract the password.
BleepingComputer has not tested this method and would love to hear anyone’s feedback regarding whether this technique works.
QNAP believes they are using recent vulnerability
Recently QNAP resolved critical vulnerabilities that could allow a remote actor to gain full access to a device and execute ransomware.
QNAP fixed these two vulnerabilities on April 16th with the following descriptions:
- CVE-2020-2509: Command Injection Vulnerability in QTS and QuTS hero
- CVE-2020-36195: SQL Injection Vulnerability in Multimedia Console and the Media Streaming Add-On
QNAP told BleepingComputer that they believe Qlocker exploits the CVE-2020-36195 vulnerability to execute the ransomware on vulnerable devices.
Due to this, it is strongly recommended to update QTS, Multimedia Console, and the Media Streaming Add-on to the latest versions.
While this will not recover your files, it will protect you from future attacks using this vulnerability.
Qlocker IOCs:
Associated Files:
!!!READ_ME.txtRansom note text:
!!! All your files have been encrypted !!!
All your files were encrypted using a private and unique key generated for the computer. This key is stored in our server and the only way to receive your key and decrypt your files is making a Bitcoin payment.
To purchase your key and decrypt your files, please follow these steps:
1. Dowload the Tor Browser at "https://www.torproject.org/". If you need help, please Google for "access onion page".
2. Visit the following pages with the Tor Browser:
gvka2m4qt5fod2fltkjmdk4gxh5oxemhpgmnmtjptms6fkgfzdd62tad.onion
3. Enter your Client Key:
[client_key]
To read the original article:



