eCommerce servers are being targeted with remote access malware that hides on Nginx servers in a way that makes it virtually invisible to security solutions.
The threat received the name NginRAT, a combination of the application it targets and the remote access capabilities it provides and is being used in server-side attacks to steal payment card data from online stores.
NginRAT was found on eCommerce servers in North America and Europe that had been infected with CronRAT, a remote access trojan (RAT) that hides payloads in tasks scheduled to execute on an invalid day of the calendar.
NginRAT has infected servers in the U.S., Germany, and France where it injects into Nginx processes that are indistinguishable from legitimate ones, allowing it to remain undetected.
RATs enable server-side code modification
Researchers at security company Sansec explain that the new malware is delivered CronRAT, although both of them fulfill the same function: providing remote access to the compromised system.
Willem de Groot, director of threat research at Sansec, told BleepingComputer that while using very different techniques to maintain their stealth, the two RATs appear to have the same role, acting as a backup for preserving remote access.
Whoever is behind these strains of malware, is using them to modify server-side code that allowed them to record data submitted by users (POST requests).
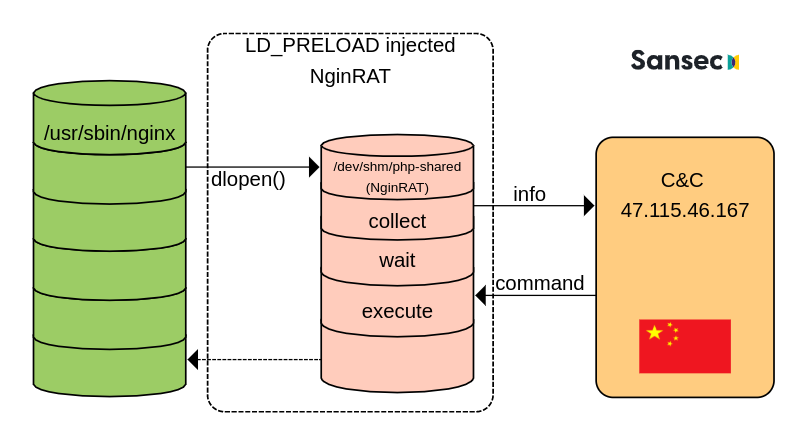
Sansec was able to study NginRAT after creating a custom CronRAT and observing the exchanges with the command and control server (C2) located in China.
The researchers tricked the C2 into sending and executing a rogue shared library payload, as part of the normal malicious interaction, disguising the NginRAT “more advanced piece of malware.”
“NginRAT essentially hijacks a host Nginx application to stay undetected. To do that, NginRAT modifies core functionality of the Linux host system. When the legitimate Nginx web server uses such functionality (eg dlopen), NginRAT intercepts it to inject itself” – Sansec
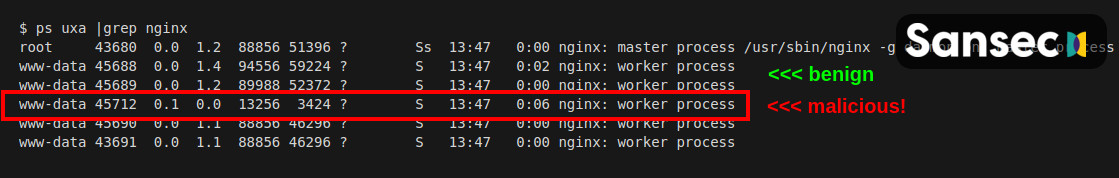
At the end of the process, the Nginx process embeds the remote access malware in a way that makes it virtually impossible to tell apart from a legitimate process.
In a technical report today, Sansec explains that NginRAT lands on a compromised system with the help of CronRAT via the custom “dwn” command that downloads the malicious Linux system library to the “/dev/shm/php-shared” location.
The library is then launched using the LD_PRELOAD debugging feature in Linux that is typically used to test system libraries.
Likely to mask the execution, the threat actor also added the “help” option multiple times at the end. Executing the command injects the NginRAT into the host Nginx app.
Because NginRAT hides as a normal Nginx process and the code exists only in the server’s memory, detecting it may be a challenge.
However, the malware is launched using two variables, LD_PRELOAD and LD_L1BRARY_PATH. Administrators can use the latter, which contains the “typo,” to reveal the active malicious processes by running the following command:
$ sudo grep -al LD_L1BRARY_PATH /proc/*/environ | grep -v self/
/proc/17199/environ
/proc/25074/environSansec notes that if NginRAT is found on the server, administrators should also check the cron tasks because it is very likely that malware is hiding there, too, added by CronRAT.
To read the original article:



