Microsoft warned customers today to patch two Active Directory domain service privilege escalation security flaws that, when combined, allow attackers to easily takeover Windows domains.
The company released security updates to address the two security vulnerabilities (tracked as CVE-2021-42287 and CVE-2021-42278 and reported by Andrew Bartlett of Catalyst IT) during the November 2021 Patch Tuesday.
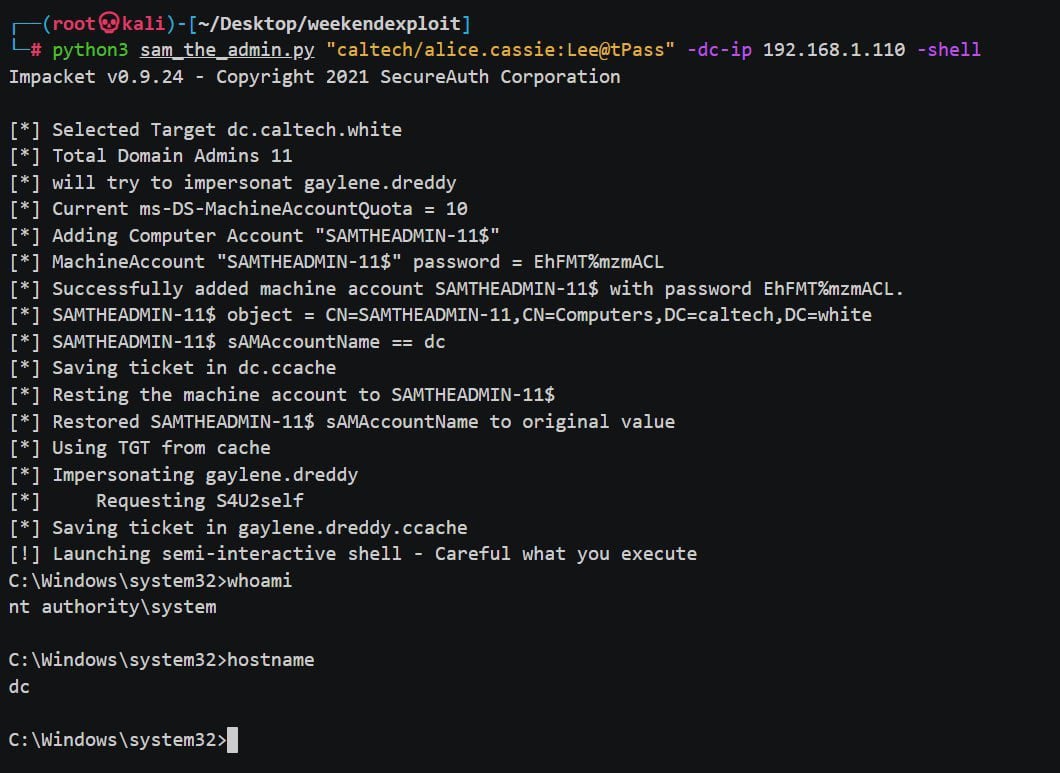
Redmond’s warning to immediately patch the two bugs — both allowing attackers to impersonate domain controllers — comes after a proof-of-concept (PoC) tool that can leverage these vulnerabilities was shared on Twitter and GitHub on December 11.
“When combining these two vulnerabilities, an attacker can create a straightforward path to a Domain Admin user in an Active Directory environment that hasn’t applied these new updates,” Microsoft explains in an advisory published today.
“This escalation attack allows attackers to easily elevate their privilege to that of a Domain Admin once they compromise a regular user in the domain.
“As always, we strongly advise deploying the latest patches on the domain controllers as soon as possible.”
Windows admins are urged to update devices exposed to attacks using the steps and information detailed in the following knowledgebase articles: KB5008102, KB5008380, KB5008602.
Researchers who tested the PoC stated that they were able to easily use the tool to escalate privileges from standard Active Directory user to a Domain Admin in default configurations.
How to detect exploitation, signs of compromise
Microsoft has also shared detailed guidance on detecting signs of exploitation in your environment and identifying potentially compromised servers using Defender for Identity advanced hunting query that looks for abnormal device name changes.
The step-by-step guide requires defenders to:
- The sAMAccountName change is based on event 4662. Please make sure to enable it on the domain controller to catch such activities. Learn more of how to do it here
- Open Microsoft 365 Defender and navigate to Advanced Hunting.
- Copy the following query (which is also available in the Microsoft 365 Defender GitHub Advanced Hunting query):
IdentityDirectoryEvents | where Timestamp > ago(1d) | where ActionType == "SAM Account Name changed" | extend FROMSAM = parse_json(AdditionalFields)['FROM SAM Account Name'] | extend TOSAM = parse_json(AdditionalFields)['TO SAM Account Name'] | where (FROMSAM has "$" and TOSAM !has "$") or TOSAM in ("DC1", "DC2", "DC3", "DC4") // DC Names in the org | project Timestamp, Application, ActionType, TargetDeviceName, FROMSAM, TOSAM, ReportId, AdditionalFields - Replace the marked area with the naming convention of your domain controllers
- Run the query and analyze the results which contain the affected devices. You can use Windows Event 4741 to find the creator of these machines if they were newly created
- We recommend investigating these compromised computers and determining that they haven’t been weaponized.
To read the original article:



