A malicious Telegram for Desktop installer distributes the Purple Fox malware to install further malicious payloads on infected devices.
The installer is a compiled AutoIt script named “Telegram Desktop.exe” that drops two files, an actual Telegram installer, and a malicious downloader.
While the legitimate Telegram installer dropped alongside the downloader isn’t executed, the AutoIT program does run the downloader (TextInputh.exe).
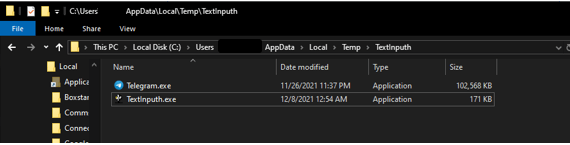
Source: Minerva Labs
When TextInputh.exe is executed, it will create a new folder (“1640618495”) under “C:\Users\Public\Videos\” and connect to the C2 to download a 7z utility and a RAR archive (1.rar).
The archive contains the payload and the configuration files, while the 7z program unpacks everything onto the ProgramData folder.
As detailed in an analysis by Minerva Labs, TextInputh.exe performs the following actions onto the compromised machine:
- Copies 360.tct with “360.dll” name, rundll3222.exe, and svchost.txt to the ProgramData folder
- Executes ojbk.exe with the “ojbk.exe -a” command line
- Deletes 1.rar and 7zz.exe and exits the process
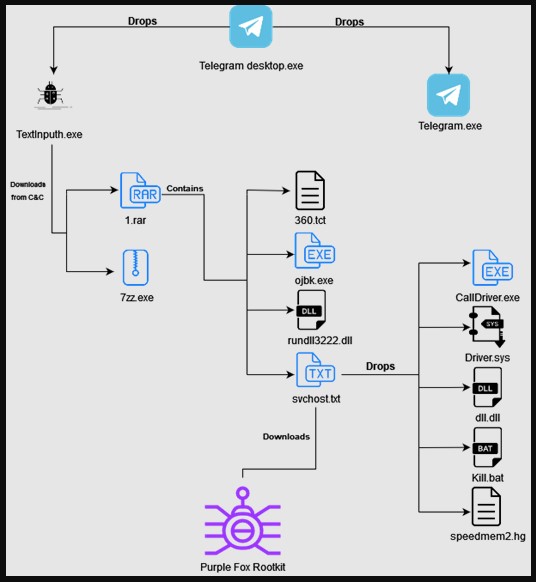
Source: Minerva Labs
Next, a registry key is created for persistence, a DLL (rundll3222.dll) disables UAC, the payload (scvhost.txt) is executed, and the following five additional files are dropped onto the infected system:
- Calldriver.exe
- Driver.sys
- dll.dll
- kill.bat
- speedmem2.hg
The purpose of these extra files is to collectively block the initiation of 360 AV processes and prevent the detection of Purple Fox on the compromised machine.
The next step for the malware is to gather basic system information, check if any security tools are running on it, and finally send all that to a hardcoded C2 address.
Once this reconnaissance process is completed, Purple Fox is downloaded from the C2 in the form of an .msi file that contains encrypted shellcode for both 32 and 64-bit systems.
Upon execution of Purple Fox, the infected machine will be restarted for the new registry settings to take effect, most importantly, the disabled User Account Control (UAC).
To achieve this, the dll.dll file sets the following three registry keys to 0:
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System ConsentPromptBehaviorAdmin
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\EnableLUA
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\PromptOnSecureDesktop
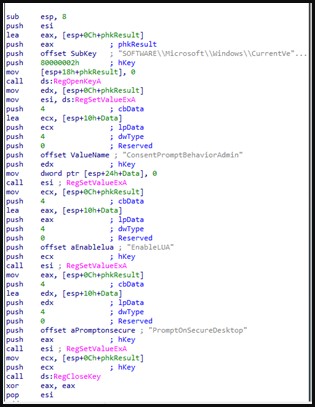
Source: Minerva Labs
Disabling bypassing UAC is vital because it gives any program that runs on the infected system, including viruses and malware, administrator privileges.
In general, UAC prevents the unauthorized installation of apps or the changing of system settings, so it should stay active on Windows at all times.
Disabling it permits Purple Fox to perform malicious functions such as file search and exfiltration, process killing, deletion of data, downloading and running code, and even worming to other Windows systems.
At this time, it is unknown how the malware is being distributed but similar malware campaigns impersonating legitimate software were distributed via YouTube videos, forum spam, and shady software sites.
To read the original article:



