The Magniber ransomware has been spotted using Windows application package files (.APPX) signed with valid certificates to drop malware pretending to be Chrome and Edge web browser updates.
This distribution method marks a shift from previous approaches seen with this threat actor, which typically relies on exploiting Internet Explorer vulnerabilities.
Browser update notification
The infection begins by visiting a payload dropping website, researchers at Korea cybersecurity company AhnLab note in a report published today.
How victims get to the website, remains unclear. The lure could be delivered via phishing emails, links sent through IMs on social media, or other distribution methods.
Two of the URLs distributing the payload are “hxxp://b5305c364336bqd.bytesoh.cam”, and “hxxp://hadhill.quest/376s53290a9n2j”, but these may not be the only ones.
Visitors to these sites receive an alert to update their Edge/Chrome browser manually, and are offered an APPX file to complete the action.
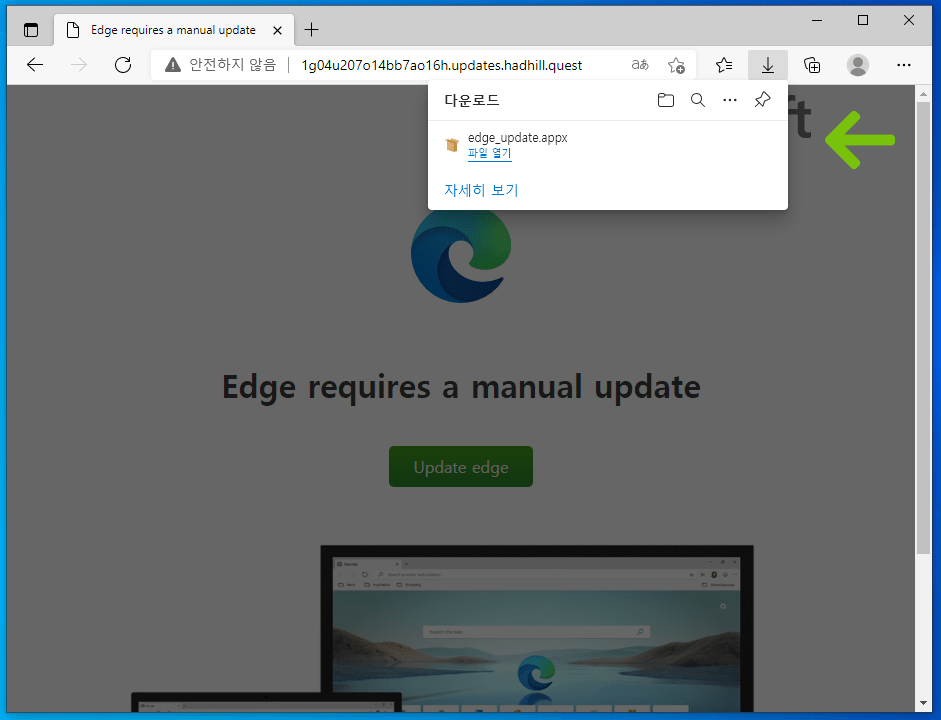
Source: ASEC
APPX files are Windows application package files created for streamlined distribution and installation, and have been abused by various threats in the past for malware distribution.
In the case of Magniber ransomware, the disguised APPX file is digitally signed with a valid certificate, so Windows sees them as trusted files that do not trigger a warning.
The threat actor’s choice to use APPX files is most likely driven by the need to reach a wider audience, since the market share for Internet Explorer is dwindling into extinction.
Dropping the payload
Accepting the malicious APPX file results in creating two files on the “C:\Program Files\WindowsApps” directory, namely the ‘wjoiyyxzllm.exe’ and the ‘wjoiyyxzllm.dll’.
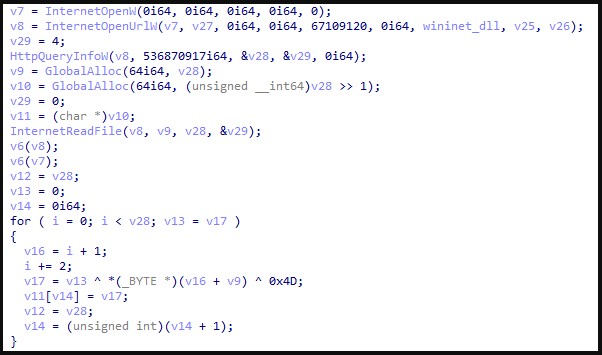
Source: ASEC
These files execute a function that fetches the Magniber ransomware payload, decodes it, and then executes it.
After encrypting the data on the system, the threat creates the following ransom note:
.png)
Source: ASEC
Although the note is in English, it is worth noting that Magniber ransomware targets Asian users exclusively these days.
At the moment there is no possibility to decrypt files locked by this malware free of charge.
Unlike most ransomware operations, Magniber did not adopt the double extortion tactic, so it does not steal files before encrypting the systems.
Backing up the data on a regular basis is a good solution to recover from attacks with low-tier ransomware like Magniber.



