The cybercrime operators behind the notorious TrickBot malware have once again upped the ante by fine-tuning its techniques by adding multiple layers of defense to slip past antimalware products.
“As part of that escalation, malware injections have been fitted with added protection to keep researchers out and get through security controls,” IBM Trusteer said in a report. “In most cases, these extra protections have been applied to injections used in the process of online banking fraud — TrickBot’s main activity since its inception after the Dyre Trojan‘s demise.”
TrickBot, which started out as a banking trojan, has evolved into a multi-purpose crimeware-as-a-service (CaaS) that’s employed by a variety of actors to deliver additional payloads such as ransomware. Over 100 variations of TrickBot have been identified to date, one of which is a “Trickboot” module that can modify the UEFI firmware of a compromised device.
In the fall of 2020, Microsoft along with a handful of U.S. government agencies and private security companies teamed up to tackle the TrickBot botnet, taking down much of its infrastructure across the world in a bid to stymie its operations.
But TrickBot has proven to be impervious to takedown attempts, what with the operators quickly adjusting their techniques to propagate multi-stage malware through phishing and malspam attacks, not to mention expand their distribution channels by partnering with other affiliates like Shathak (aka TA551) to increase scale and drive profits.
More recently, malware campaigns involving Emotet have piggybacked on TrickBot as a “delivery service,” triggering an infection chain that drops the Cobalt Strike post-exploitation tool directly onto compromised systems. As of December 2021, an estimated 140,000 victims across 149 countries have been infected by TrickBot.
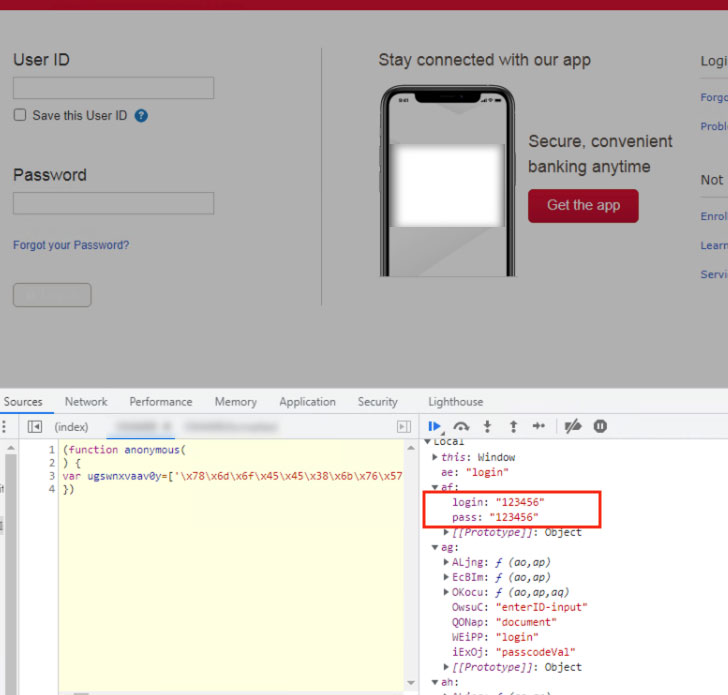
The new updates observed by IBM Trusteer relate to the real-time web injections used to steal banking credentials and browser cookies. This works by steering victims to replica domains when attempting to navigate to a banking portal as part of what’s called a man-in-the-browser (MitB) attack.
Also put to use is a server-side injection mechanism that intercepts the response from a bank’s server and redirects it to an attacker-controlled server, which, in turn, inserts additional code into the webpage before it is relayed back to the client.
“To facilitate fetching the right injection at the right moment, the resident TrickBot malware uses a downloader or a JavaScript (JS) loader to communicate with its inject server,” said Michael Gal, a security web researcher at IBM.
Other lines of defense adopted the latest version of TrickBot shows the use of encrypted HTTPS communications with the command-and-control (C2) server for fetching injections; an anti-debugging mechanism to thwart analysis; and new ways to obfuscate and hide the web inject, including the addition of redundant code and the incorporation of hex representation for initializing variables.
Specifically, upon detecting any attempt made to beautify the injected script, TrickBot’s anti-debugging feature triggers a memory overload that would crash the page, effectively preventing any examination of the malware.
“The TrickBot Trojan and the gang that operates it have been a cyber crime staple since they took over when a predecessor, Dyre, went bust in 2016,” Gal said. “TrickBot has not rested a day. Between takedown attempts and a global pandemic, it has been diversifying its monetization models and growing stronger.”
To read the original article:
https://thehackernews.com/2022/01/trickbot-malware-using-new-techniques.html