Google has released Chrome 99.0.4844.84 for Windows, Mac, and Linux users to address a high-severity zero-day bug exploited in the wild.
“Google is aware that an exploit for CVE-2022-1096 exists in the wild,” the browser vendor said in a security advisory published on Friday.
The 99.0.4844.84 version is already rolling out worldwide in the Stable Desktop channel, and Google says it might be a matter of weeks until it reaches the entire userbase.
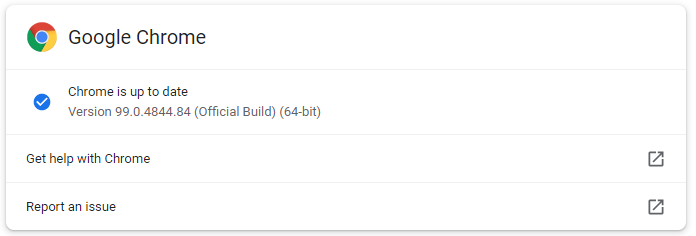
This update was available immediately when BleepingComputer checked for new updates by going into Chrome menu > Help > About Google Chrome.
The web browser will also auto-check for new updates and automatically install them after the next launch.
Exploitation details not revealed
The zero-day bug fixed today (tracked as CVE-2022-1096) is a high severity type confusion weakness in the Chrome V8 JavaScript engine reported by an anonymous security researcher.
While type confusion flaws generally lead to browser crashes following successful exploitation by reading or writing memory out of buffer bounds, attackers can also exploit them to execute arbitrary code.
Even though Google said it detected attacks exploiting this zero-day in the wild, the company did not share technical details or additional info regarding these incidents.
“Access to bug details and links may be kept restricted until a majority of users are updated with a fix,” Google said.
“We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed.”
Google Chrome users should have enough time to upgrade Chrome and prevent exploitation attempts until the browser vendor releases more info.
Second Chrome zero-day patched this year
With this update, Google addressed the second Chrome zero-day since the start of 2022, the other one (tracked as CVE-2022-0609) patched last month.
The Google Threat Analysis Group (TAG) revealed that North Korean-backed state hackers exploited the CVE-2022-0609 zero-day weeks before the February patch. The earliest sign of active exploitation was found on January 4, 2022.
The zero-day was exploited by two separate threat groups backed by the North Korean government in campaigns pushing malware via phishing emails using fake job lures and compromised websites hosting hidden iframes to serve an exploit kit.
“The emails contained links spoofing legitimate job hunting websites like Indeed and ZipRecruiter,” the researchers explained.
“In other cases, we observed fake websites – already set up to distribute trojanized cryptocurrency applications – hosting iframes and pointing their visitors to the exploit kit.”
To read the original article:



