Researchers analyzing the leaked chats of the notorious Conti ransomware operation have discovered that teams inside the Russian cybercrime group were actively developing firmware hacks.
According to messages exchanged between members of the cybercrime syndicate, Conti developers had created proof-of-concept (PoC) code that leveraged Intel’s Management Engine (ME) to overwrite flash and gain SMM (System Management Mode) execution.
The ME is an embedded microcontroller within Intel chipsets running a micro-OS to provide out-of-band services. Conti was fuzzing that component to find undocumented functions and commands they could leverage.
From there, Conti could access the flash memory that hosted UEFI/BIOS firmware, bypass write protections, and perform arbitrary code execution on the compromised system.
The final goal would be to drop an SMM implant that would run with the highest possible system privileges (ring-0) while practically undetectable from OS-level security tools.
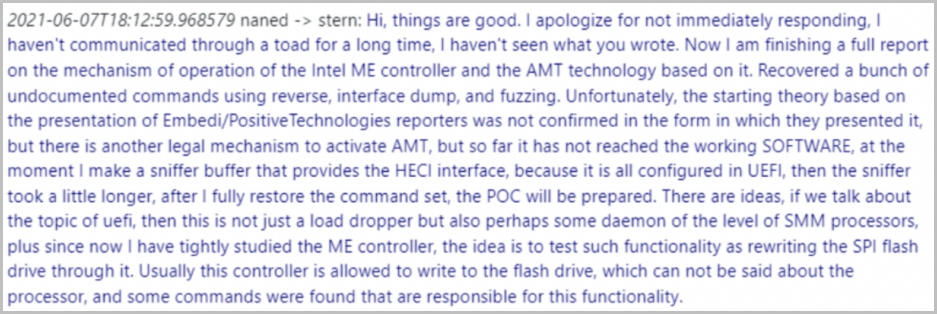
It is important to note that contrary to TrickBot’s module that targeted UEFI firmware flaws, aiding Conti infections and later undertaken by the ransomware group, the new findings indicate that the malicious engineers were striving to discover new, unknown vulnerabilities in the ME.
Firmware attacks in ransomware
For a firmware attack to be possible, the ransomware actors would first need to access the system via a common pathway such as phishing, exploiting a vulnerability, or performing a supply chain attack.
After compromising the ME, the attackers would have to follow an attack plan based on what “out-of-write protection” regions they are allowed to access, depending on the ME implementation and various restrictions/protections.
Eclypsium says these could be either access to overwrite the SPI Descriptor and move the UEFI/BIOS outside the protected area or direct access to the BIOS region.
.png)
There’s also the scenario of the ME not having access to either, in which case the threat actors could leverage Intel’s Management Engine to force a boot from virtual media and unlock PCH protections that underpin the SPI controller.
Conti could use this attack flow to brick systems permanently, gain ultimate persistence, evade anti-virus and EDR detections, and bypass all security controls at the OS layer.
Conti gone, but code still alive
While the Conti operation appears to have shut down, many of its members have moved to other ransomware operations where they continue to conduct attacks.
This also means that all the work done to develop exploits like the one spotted by Eclypsium in the leaked chats will continue to exist.
As the researchers explain, Conti had a working PoC for these attacks since last summer, so it’s likely that they already had the chance to employ it in actual attacks.
The RaaS might return in a rebranded form, the core members might join other ransomware operations, and overall, the exploits will continue to be used.
To protect from the threats, apply the available firmware updates for your hardware, monitor ME for configuration changes, and verify the integrity of the SPI flash regularly.
To read the original article:



